Security researchers have revealed that North Korean cyber operatives are increasingly targeting global companies by impersonating legitimate professionals on LinkedIn. The threat actors are applying for remote roles using real LinkedIn accounts, often tied to verified email addresses and identity badges, to make their applications appear authentic.
This long-running campaign, tracked as Jasper Sleet, PurpleDelta, and Wagemole, has two primary objectives: generate revenue to fund DPRK’s weapons programs and conduct cyber espionage by stealing sensitive corporate data. In some instances, attackers have escalated operations to demand ransoms to prevent information leaks.
Remote Work Scheme as a Revenue Engine
Silent Push described the North Korean remote worker initiative as a “high-volume revenue engine,” enabling operatives to gain administrative access to code repositories and persist undetected within corporate systems. Salaries earned are converted into cryptocurrency using chain-hopping, token swapping, and decentralized smart contracts to obscure the money trail, according to Chainalysis.
To mitigate the threat, experts advise individuals suspecting identity misuse to post warnings on social media, share verified communication channels, and confirm account ownership via company emails or direct LinkedIn connections.
The Norwegian Police Security Service (PST) confirmed multiple cases where Norwegian firms unknowingly employed what were likely DPRK operatives. PST warned that salaries paid may indirectly finance the country’s weapons programs.
Contagious Interview: A Social Engineering Variant
Alongside the remote worker scheme, DPRK-linked actors operate a Contagious Interview campaign. Victims are lured via fake hiring flows on LinkedIn and asked to complete skill assessments that deploy malicious code.
In one documented attack mimicking Fireblocks’ hiring process, candidates were instructed to clone a GitHub repository and execute npm commands, which installed malware. EtherHiding, a blockchain-based technique, was used to host command-and-control infrastructure, making takedown efforts more difficult.
Recent variants leverage malicious VS Code task files to run JavaScript malware disguised as web fonts, deploying tools like BeaverTail and InvisibleFerret for persistent access and theft of cryptocurrency wallets and browser credentials.
Koalemos RAT Deployment
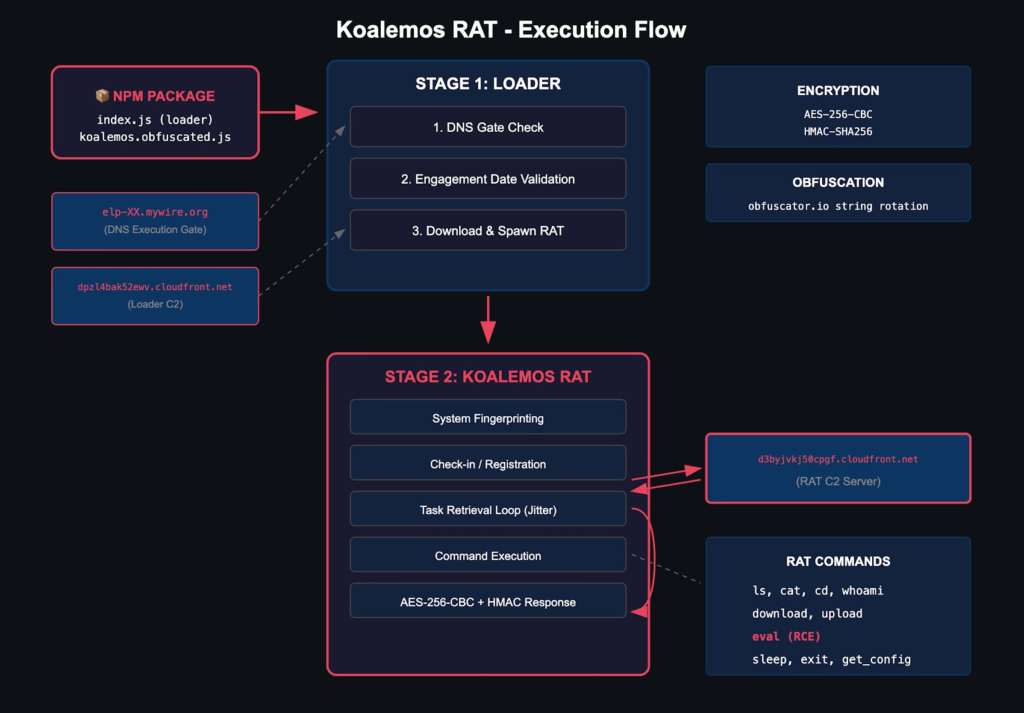
Panther researchers observed attackers using malicious npm packages to deliver the Koalemos modular JavaScript RAT. The RAT supports 12 commands, including filesystem operations, file transfers, discovery tasks, and remote code execution. Initial loaders implement DNS-based gating and engagement date validation before spawning RAT modules as detached processes.
Koalemos performs system fingerprinting, encrypted command-and-control communication, and full remote access capabilities, granting attackers comprehensive control over compromised endpoints.
Labyrinth Chollima Divides into Specialized Units
CrowdStrike reports that the North Korean hacking group Labyrinth Chollima has split into three operational clusters:
- Core Labyrinth Chollima – focused on cyber espionage.
- Golden Chollima (aka AppleJeus, Citrine Sleet, UNC4736) – performs smaller-scale cryptocurrency thefts.
- Pressure Chollima (aka Jade Sleet, TraderTraitor, UNC4899) – targets high-value assets with advanced implants.
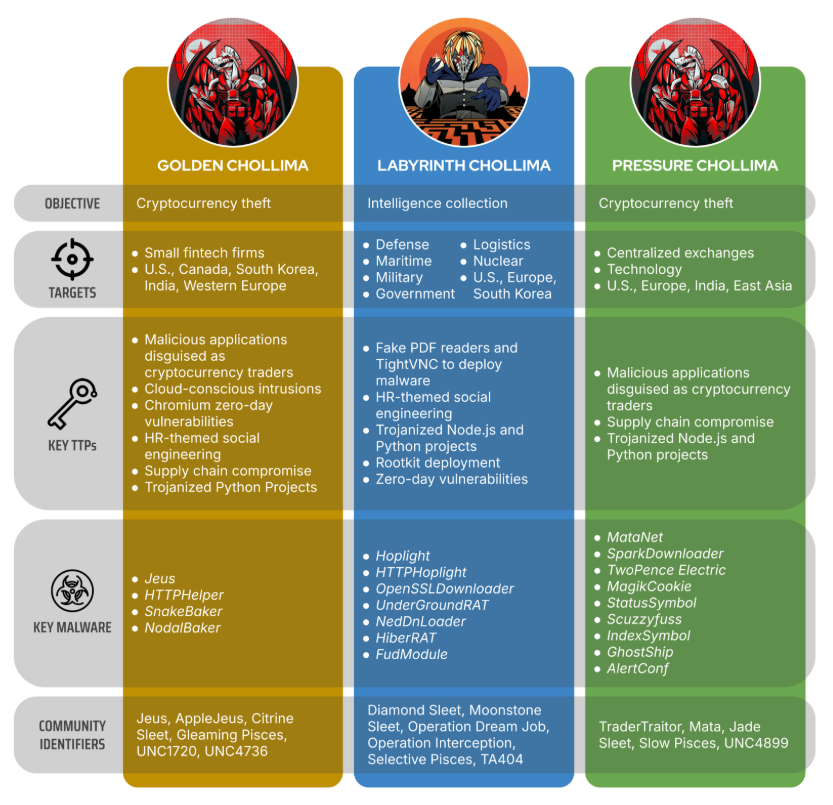
These clusters maintain shared infrastructure and toolsets, including HR-themed social engineering, trojanized legitimate software, and malicious Node.js and Python packages. The group is linked to the Lazarus Group, with BlueNoroff splintering into TraderTraitor and CryptoCore (aka Sapphire Sleet). Operations like Operation Dream Job employ the FudModule rootkit to maintain stealth while collecting intelligence.
CrowdStrike emphasized the continued coordination across clusters, with overlapping tools and tradecraft suggesting centralized DPRK cyber apparatus management.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


