The North Korean threat group known as ScarCruft has been linked to a sophisticated cyber espionage campaign that leverages cloud storage services and removable media to infiltrate even isolated environments.
Security researchers at Zscaler ThreatLabz have named the operation Ruby Jumper. The campaign, uncovered in December 2025, introduces several new malware families designed to conduct surveillance, move laterally across systems, and breach air gapped networks.
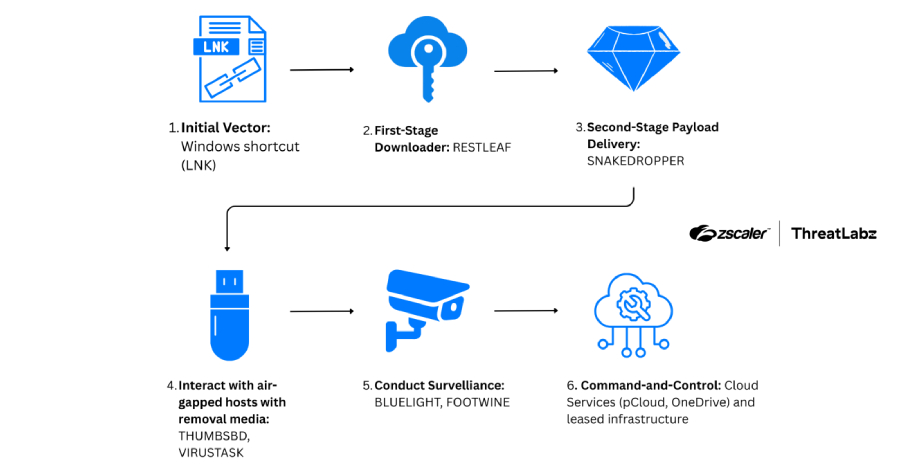
Multi Stage Infection Chain
The attack begins when a victim opens a malicious shortcut file. Once triggered, the file launches a PowerShell command that scans its directory and extracts multiple embedded components based on file size. These embedded payloads include a decoy document, an executable file, an additional PowerShell script, and a batch file.
One lure document analyzed by researchers contained an article discussing the Palestine Israel conflict, translated into Arabic from a North Korean news source, suggesting geopolitical themes are used to entice targets.
The batch script launches PowerShell, which decrypts and loads shellcode into memory. The Windows executable payload, identified as RESTLEAF, is executed directly in memory to avoid detection.
Abuse of Zoho WorkDrive for Command and Control
RESTLEAF marks a new development in ScarCruft operations by abusing Zoho WorkDrive for command and control communications. Using a valid access token, the malware authenticates with the cloud service and downloads additional shellcode. This code is injected into processes, eventually deploying another component called SNAKEDROPPER.
SNAKEDROPPER installs a Ruby runtime environment, establishes persistence through a scheduled task, and drops two additional payloads, THUMBSBD and VIRUSTASK.
USB Malware Enables Air Gap Breach
THUMBSBD is disguised as a Ruby script and plays a central role in bypassing network isolation. It monitors for removable media devices and creates hidden directories on them to store attacker issued commands and execution results. This enables data transfer between internet connected systems and air gapped machines.
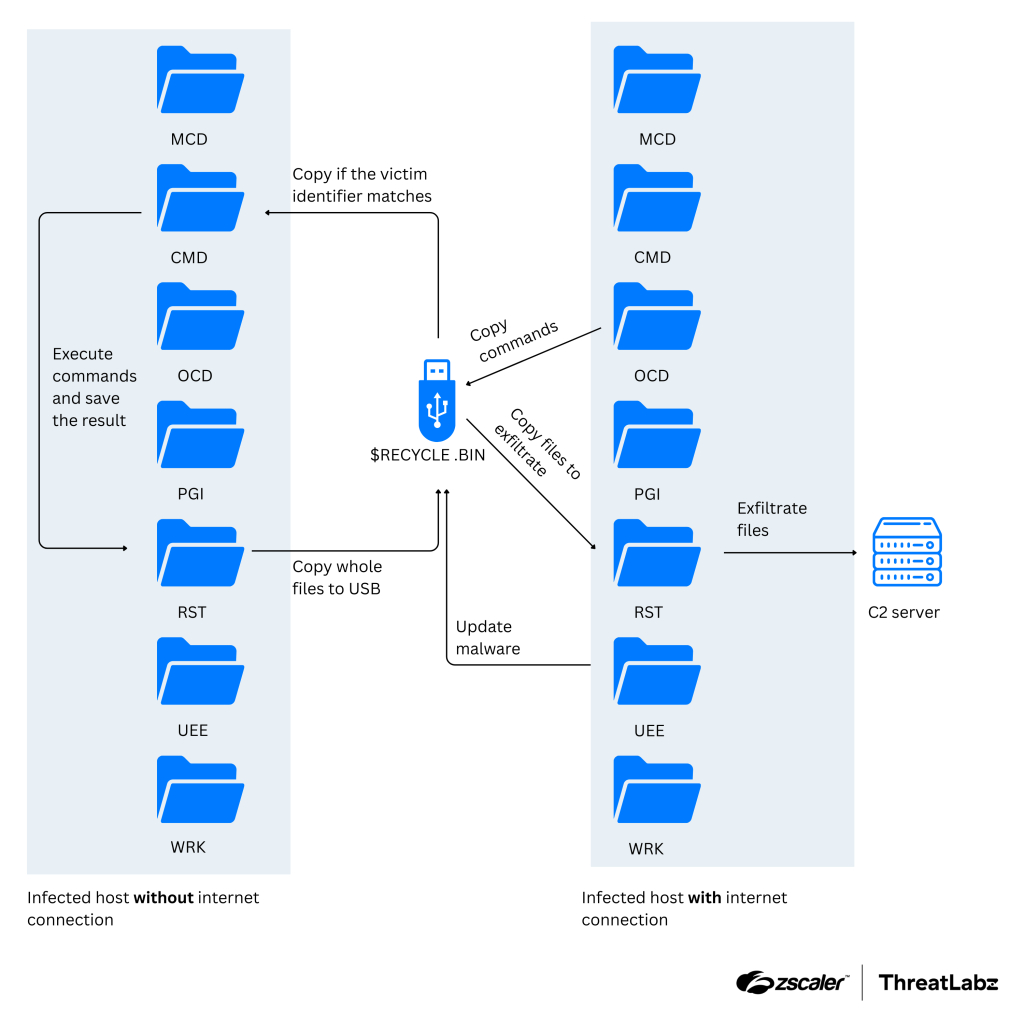
THUMBSBD can collect system data, retrieve secondary payloads, exfiltrate sensitive files, and execute arbitrary commands. One of the payloads it deploys is FOOTWINE, an encrypted surveillance tool equipped with keylogging, audio recording, and video capture capabilities. FOOTWINE communicates with its command server using a custom binary protocol over TCP.
Supported commands include interactive shell access, file management, registry modification, process enumeration, screenshot capture, audio and video monitoring, batch script execution, proxy setup, and dynamic library loading.
Distribution of BLUELIGHT and Additional Backdoors
THUMBSBD is also capable of distributing BLUELIGHT, a backdoor previously associated with ScarCruft since at least 2021. This malware abuses well known cloud platforms such as Google Drive, Microsoft OneDrive, pCloud, and BackBlaze to execute commands, explore file systems, upload or download data, and remove traces of infection.
VIRUSTASK, another Ruby based component delivered in the campaign, focuses exclusively on spreading through removable drives. Unlike THUMBSBD, which handles command execution and data exfiltration, VIRUSTASK is dedicated to achieving initial access on isolated systems by weaponizing USB media.
Strategic Targeting of Isolated Environments
Researchers emphasize that Ruby Jumper represents a carefully engineered multi stage infection chain. It combines malicious shortcut files, encrypted payloads, and a self contained Ruby execution environment while blending into legitimate cloud services to evade detection.
Most notably, the coordinated use of THUMBSBD and VIRUSTASK demonstrates a deliberate effort to compromise air gapped environments, which are typically considered secure due to their lack of internet connectivity.
The campaign underscores a growing trend among advanced threat actors to exploit trusted cloud platforms and physical media to overcome network segmentation. Organizations operating critical infrastructure or sensitive systems are advised to strengthen removable media policies, monitor unusual cloud authentication activity, and restrict execution of unauthorized scripts to reduce exposure to similar attacks.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.