The cyber threat cluster identified as SloppyLemming has been linked to a new wave of targeted attacks against government institutions and critical infrastructure organizations in Pakistan and Bangladesh, according to fresh research from Arctic Wolf.
The activity reportedly occurred between January 2025 and January 2026 and involved two separate malware delivery chains. These attack paths deployed a backdoor known as BurrowShell alongside a Rust based keylogger designed for data theft.
Evolution in SloppyLemming’s Malware Toolkit
Arctic Wolf highlighted a significant shift in the group’s technical capabilities. Earlier operations showed reliance on conventional compiled programming languages and publicly available adversary simulation frameworks such as Cobalt Strike and Havoc, along with a custom remote access tool named NekroWire RAT.
However, the recent use of Rust marks a strategic upgrade in their development practices. Rust is increasingly favored in cyber operations due to its performance, cross platform flexibility, and difficulty of reverse engineering.
SloppyLemming, also tracked under aliases such as Outrider Tiger and Fishing Elephant, has been active since at least 2022. The group has historically targeted sectors including government, law enforcement, energy, telecommunications, and technology across Pakistan, Sri Lanka, Bangladesh, and China.
Past campaigns have featured malware strains like Ares RAT and WarHawk, tools frequently associated with threat groups SideCopy and SideWinder.
Spear Phishing and ClickOnce Exploitation
The latest campaign began with spear phishing emails containing PDF decoys and macro enabled Excel documents. These lures initiated carefully structured infection chains.
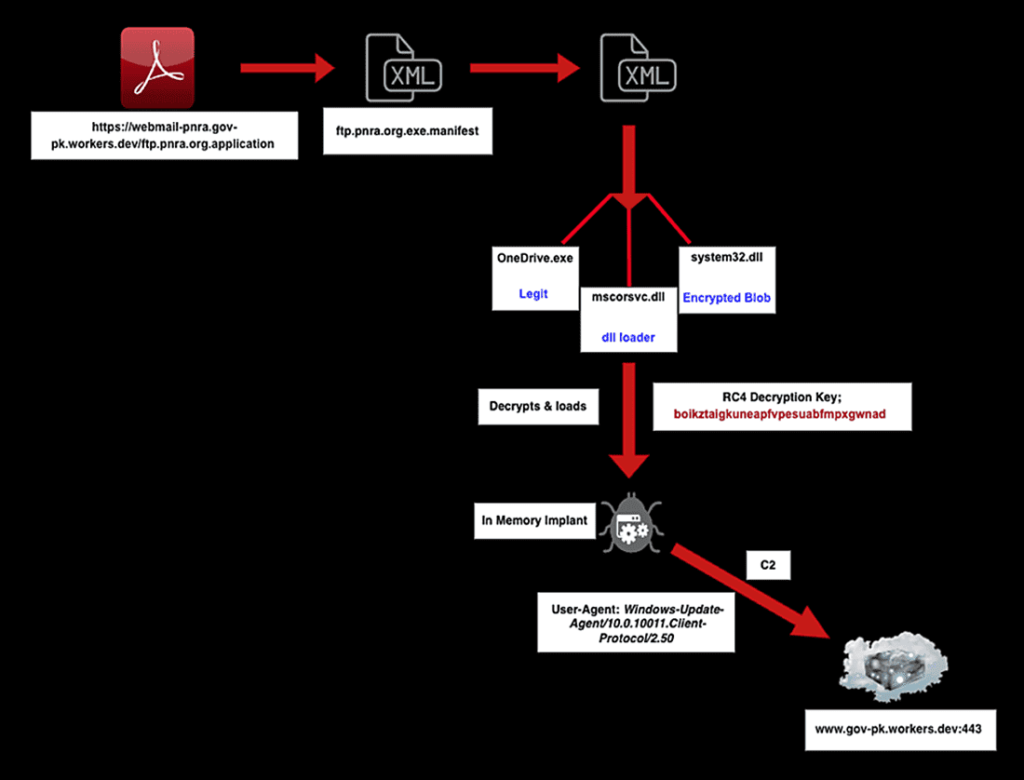
In the first attack scenario, PDF files embedded URLs that redirected victims to ClickOnce application manifests. These manifests downloaded a legitimate Microsoft .NET runtime executable named NGenTask.exe alongside a malicious dynamic link library file called mscorsvc.dll.
Through a technique known as DLL side loading, the malicious DLL was executed, decrypting and launching a custom 64 bit shellcode implant referred to as BurrowShell.
BurrowShell Backdoor Capabilities
BurrowShell functions as a comprehensive backdoor, granting attackers control over infected systems. Its features include file system manipulation, screenshot capture, remote command execution, and SOCKS proxy capabilities for network tunneling.
To evade detection, the malware disguises its command and control communications as Windows Update traffic. It also uses RC4 encryption with a 32 character key to secure transmitted payloads.
Rust Based Keylogger and Network Reconnaissance
The second infection chain leveraged Excel documents embedded with malicious macros. Once activated, these macros deployed a Rust based keylogger capable of capturing keystrokes and stealing sensitive information.
In addition to credential harvesting, the malware included functionality for port scanning and network enumeration, enabling broader reconnaissance within compromised environments.
Expanding Cloudflare Workers Infrastructure
Arctic Wolf’s investigation revealed that the threat actor registered 112 domains using Cloudflare Workers infrastructure over the course of a year. This represents a sharp increase compared to the 13 domains identified in September 2024.
The continued use of Cloudflare Workers, often with government themed typo squatting domain patterns, strengthens attribution to SloppyLemming. Additional indicators include deployment of the Havoc command and control framework, reliance on DLL side loading, and consistent victim targeting patterns.
Some elements of the campaign, including ClickOnce based execution methods, overlap with tradecraft observed in a SideWinder campaign documented in October 2025.
Strategic Targeting in South Asia
The selection of targets suggests an intelligence collection motive aligned with regional strategic competition in South Asia.
In Pakistan, victims reportedly included nuclear regulatory authorities, defense logistics entities, and telecommunications infrastructure providers. In Bangladesh, the campaign focused on energy utilities and financial institutions.
Researchers concluded that the dual payload strategy reflects operational flexibility. BurrowShell enables covert command and control operations and network tunneling, while the Rust based keylogger supports credential harvesting and data theft.
The campaign underscores ongoing cyber espionage activity targeting sensitive government and infrastructure sectors across South Asia, with evolving technical sophistication and expanding infrastructure footprint.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


