A major international cybersecurity operation has successfully dismantled Tycoon 2FA, a large phishing-as-a-service platform that enabled cybercriminals to launch advanced phishing attacks targeting organizations worldwide.
The takedown was coordinated by the European law enforcement agency Europol along with multiple cybersecurity firms and global investigators. Authorities confirmed that the platform was responsible for tens of thousands of phishing incidents and widespread credential theft.
Tycoon 2FA had become one of the most active phishing infrastructures on the internet, allowing criminals to bypass security mechanisms such as multi-factor authentication and gain access to corporate accounts.
How Tycoon 2FA Operated
Tycoon 2FA functioned as a subscription-based phishing toolkit that allowed cybercriminals to run phishing campaigns with minimal technical knowledge.
The platform first appeared in August 2023 and was promoted primarily through encrypted messaging platforms such as Telegram and Signal.
Access to the toolkit required a paid subscription:
- $120 for 10 days of access
- $350 for one month of access to a web-based control panel
Investigators allege that the platform’s main developer is Saad Fridi, who is believed to be operating from Pakistan.
The phishing panel served as the central command interface for attackers, enabling them to manage and monitor their campaigns in real time.
Features of the Phishing Control Panel
The Tycoon 2FA administration panel provided a complete environment for launching credential-stealing operations. Key features included:
- Pre-built phishing page templates
- Domain and hosting configuration tools
- Attachment-based phishing delivery
- Campaign monitoring dashboards
- Victim tracking and login attempt analysis
Attackers could collect sensitive information such as:
- usernames and passwords
- multi-factor authentication codes
- browser session cookies
These stolen details could then be downloaded directly from the panel or automatically forwarded to Telegram channels for immediate monitoring.
According to Europol, this infrastructure allowed thousands of cybercriminals to secretly access corporate email systems and cloud accounts.
Massive Scale of Global Phishing Campaigns
Security researchers estimate that the platform generated tens of millions of phishing emails every month.
Investigations revealed that the phishing campaigns facilitated unauthorized access to nearly 100,000 organizations worldwide, including:
- hospitals
- schools
- government agencies
- corporate enterprises
As part of the law enforcement action, authorities successfully shut down 330 domains that hosted the phishing pages and backend control systems.
Over 64,000 Phishing Incidents Linked to the Platform
Threat intelligence firm Intel 471 described Tycoon 2FA as a particularly dangerous phishing toolkit due to its scale and automation capabilities.
The company linked the platform to more than 64,000 phishing incidents and tens of thousands of malicious domains.
Technology giant Microsoft tracked the operators of Tycoon 2FA under the threat group name Storm-1747. According to Microsoft, the platform became the most active phishing infrastructure observed in 2025.
In October 2025 alone, Microsoft blocked more than 13 million phishing emails associated with Tycoon 2FA.
By mid-2025, the phishing kit was responsible for approximately 62 percent of all phishing attempts blocked by Microsoft, including more than 30 million malicious emails in a single month.
Researchers estimate that the operation targeted around 96,000 victims globally, including over 55,000 Microsoft customers.

Global Distribution of Victims
Threat intelligence data collected by SpyCloud revealed the geographic spread of victims affected by the platform.
Countries with the highest number of compromised accounts included:
- United States – 179,264 victims
- United Kingdom – 16,901 victims
- Canada – 15,272 victims
- India – 7,832 victims
- France – 6,823 victims
Researchers noted that most targeted accounts belonged to enterprise environments and corporate domains, suggesting that the phishing campaigns were primarily aimed at organizations rather than individual users.
AiTM Phishing Techniques Used by Tycoon 2FA
Email security company Proofpoint identified Tycoon 2FA as the largest source of adversary-in-the-middle phishing attacks.
In February 2026 alone, Proofpoint observed more than three million phishing messages generated by the toolkit.
Cybersecurity firm Trend Micro reported that the phishing platform had approximately 2,000 active users who were running phishing campaigns across multiple industries.
The attacks targeted organizations in sectors such as:
- healthcare
- education
- finance
- government
- non-profit organizations
Each month, phishing emails generated by the service reached over 500,000 organizations worldwide.
Impersonating Trusted Online Services
Tycoon 2FA enabled attackers to impersonate widely used digital platforms by cloning legitimate login pages, including:
- Microsoft 365
- OneDrive
- Outlook
- SharePoint
- Gmail
These fake login pages were designed to look identical to legitimate authentication portals, tricking users into entering their credentials.
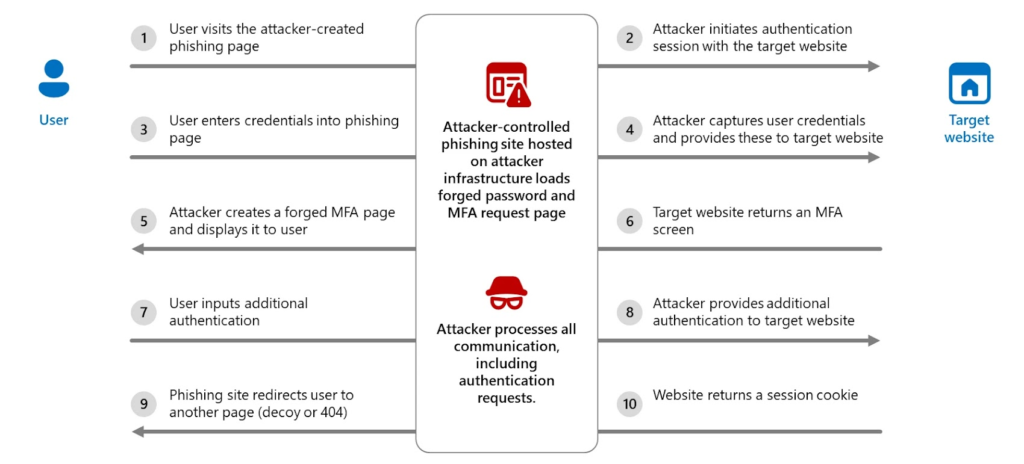
Microsoft explained that the toolkit intercepted login data by acting as a proxy between the victim and the real authentication service, allowing attackers to capture session cookies and bypass MFA protections.
Even if victims later changed their passwords, attackers could maintain access unless active sessions and authentication tokens were revoked.
Advanced Evasion and Anti-Detection Techniques
The phishing kit incorporated several advanced techniques designed to evade security detection, including:
- keystroke monitoring
- anti-bot protection systems
- browser fingerprinting
- heavy code obfuscation
- self-hosted CAPTCHA systems
- dynamic decoy pages
Another tactic involved hosting phishing infrastructure on rapidly changing domains, often using different top-level domains and temporary fully qualified domain names.
These domains typically remained active for only 24 to 72 hours, making it difficult for defenders to maintain effective blocklists.
ATO Jumping Attack Method
Attackers using Tycoon 2FA frequently used a technique known as Account Takeover Jumping (ATO Jumping).
In this method, once an email account is compromised, attackers use the victim’s account to send phishing messages containing malicious links to their contacts.
Because these messages appear to originate from trusted senders, victims are far more likely to click the links and enter their credentials.
According to Proofpoint, this strategy significantly increases the success rate of phishing attacks.
Growing Threat to Enterprise Security
Security experts warn that identity-based attacks continue to rise rapidly across organizations.
Proofpoint threat researcher Selena Larson noted that in 2025, 99 percent of organizations experienced account takeover attempts, while 67 percent reported at least one successful account compromise.
Even more concerning, 59 percent of compromised accounts had multi-factor authentication enabled, demonstrating how sophisticated phishing techniques can bypass traditional defenses.
Successful account takeover attacks often serve as the starting point for larger cyber incidents, including ransomware attacks and data breaches.
Why Organizations Must Strengthen Identity Security
Experts stress that organizations must adopt stronger identity protection strategies to defend against phishing platforms like Tycoon 2FA.
Recommended defenses include:
- continuous email threat monitoring
- stronger phishing detection systems
- session token revocation policies
- user security awareness training
- zero-trust authentication frameworks
Security researchers warn that as attackers increasingly focus on identity systems, corporate email accounts remain one of the most valuable targets in modern cyber operations.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


