A cyber espionage campaign linked to China has been targeting telecommunications infrastructure across South America since 2024. The attackers are focusing on Windows servers, Linux systems, and network edge devices, deploying multiple sophisticated malware implants to maintain long term access.
Security researchers from Cisco Talos are monitoring this activity under the name UAT-9244, a threat cluster that appears closely related to another known cyber espionage group called FamousSparrow.
Possible Connection to Other Chinese Threat Groups
Experts note that FamousSparrow shares tactical similarities with Salt Typhoon, a cyber espionage operation previously associated with attacks against global telecom providers. Although the targets and techniques appear similar, analysts say there is no confirmed technical evidence proving that UAT-9244 and Salt Typhoon are directly connected.
The campaign mainly focuses on compromising telecommunications infrastructure, an attractive target for intelligence gathering and surveillance activities.
Three Newly Identified Malware Implants
Researchers discovered three previously undocumented malware tools used during the attacks.
The implants include:
TernDoor
A Windows based backdoor used to gain persistent access to compromised machines.
PeerTime
A Linux peer to peer backdoor designed to infect servers and embedded systems.
BruteEntry
A tool deployed on network edge devices to conduct large scale brute force attacks against internet facing services.
Each implant serves a different purpose within the attackers’ operational toolkit.
TernDoor Backdoor Targets Windows Systems
The attackers deploy the TernDoor malware through a technique known as DLL side loading. In this process, a legitimate executable named wsprint.exe is used to load a malicious dynamic library called BugSplatRc64.dll.
Once executed, the malicious DLL decrypts and runs the final payload directly in memory. TernDoor is believed to be a variant related to Crowdoor, which itself is derived from SparrowDoor, another malware family linked to FamousSparrow operations.
After infection, TernDoor establishes persistence using scheduled tasks or the Windows Registry Run key. The malware can also load a custom driver that allows attackers to control system processes, including suspending, resuming, or terminating them.
Command and Control Communication
Before activating, the malware checks whether it has been injected into the msiexec.exe process. After verifying this condition, it decrypts its configuration and retrieves command and control server details.
Through this connection, attackers can perform various actions such as:
- Creating new processes
- Executing arbitrary commands
- Reading and modifying files
- Gathering system information
- Deploying additional malicious components
This allows attackers to maintain persistent remote control over compromised systems.
PeerTime Linux Backdoor Uses Peer-to-Peer Communication
Further analysis revealed a Linux based backdoor called PeerTime, designed to operate on multiple hardware architectures including:
- ARM
- AARCH
- PPC
- MIPS
This allows the malware to target embedded systems and networking devices commonly used in telecommunications infrastructure.
The malware is delivered through a shell script that installs an ELF binary known as an instrumentor. This binary checks whether Docker is installed on the infected machine. If Docker is detected, the PeerTime loader is executed.
Researchers discovered debug strings written in Simplified Chinese inside the malware, suggesting that the tool was likely developed by Chinese speaking threat actors.
BitTorrent-Based Command Infrastructure
PeerTime uses an unusual command and control method. Instead of traditional centralized servers, the malware uses the BitTorrent protocol to retrieve command information and download additional payloads.
The malware also disguises itself by renaming its process to appear legitimate, making detection more difficult for security tools.
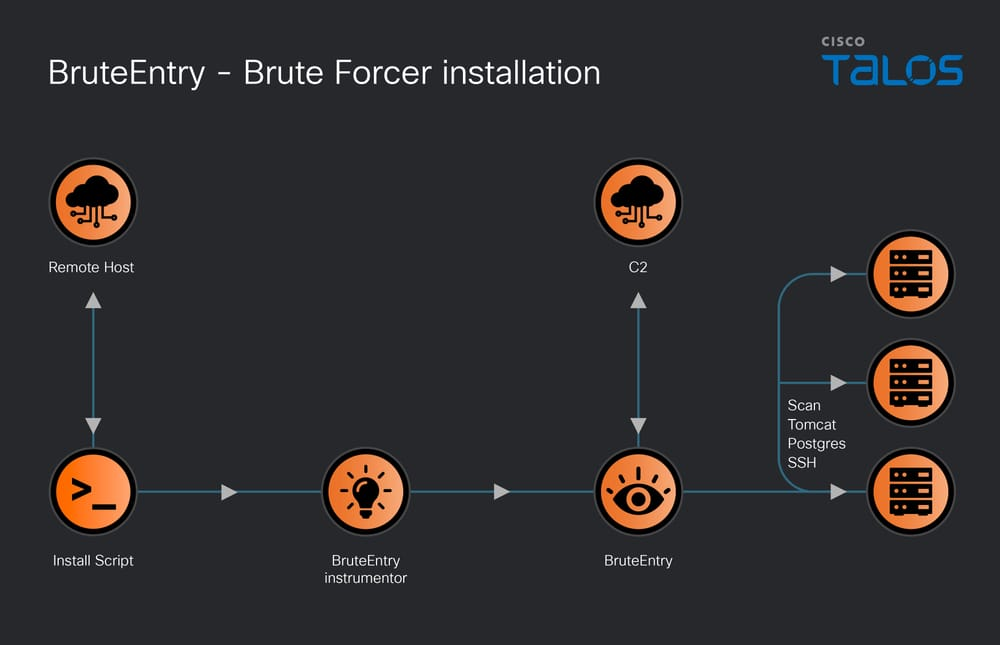
BruteEntry Converts Devices into Attack Proxies
Another component discovered during the investigation is BruteEntry, a brute force scanning tool deployed on network edge devices.
This malware converts compromised systems into scanning nodes within an Operational Relay Box (ORB) infrastructure. The tool performs brute force attacks against services such as:
- PostgreSQL databases
- SSH servers
- Apache Tomcat systems
The malware attempts multiple credential combinations to gain unauthorized access. Successful login attempts are reported back to the attackers’ command servers.
Growing Threat to Global Telecommunications
The campaign highlights the increasing focus of advanced persistent threat groups on telecommunications networks. These systems provide valuable intelligence opportunities because they process massive amounts of communications data.
Security researchers warn that telecom providers should carefully monitor their networks, update outdated systems, and strengthen security controls to prevent similar intrusions.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


