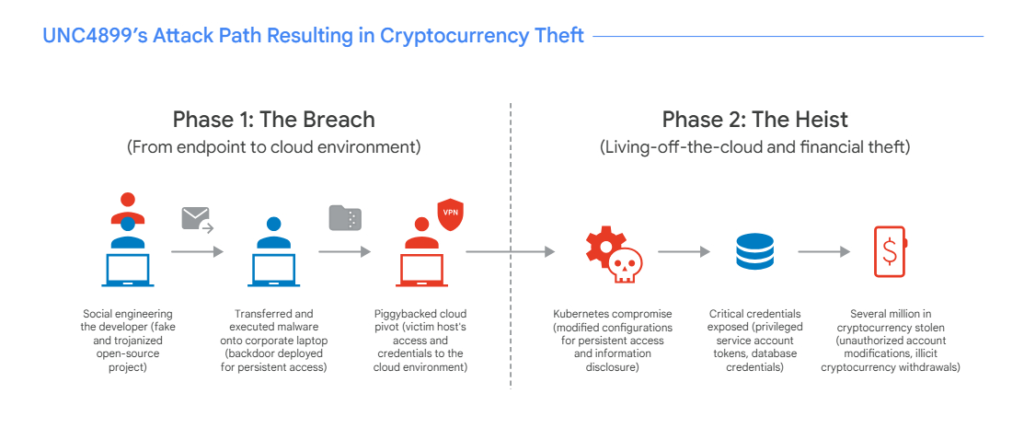
A sophisticated cyberattack attributed to the North Korean threat group UNC4899 has reportedly compromised a cryptocurrency organization in 2025, resulting in the theft of millions of dollars worth of digital assets. The attack demonstrates how modern cyber operations combine social engineering, cloud exploitation, and supply chain style infiltration.
Security researchers have linked the activity with moderate confidence to a state backed hacking group known by several names, including Jade Sleet, PUKCHONG, Slow Pisces, and TraderTraitor.
According to findings published in Google Cloud’s H1 2026 Cloud Threat Horizons Report, the incident stands out because it combined multiple attack techniques, beginning with social engineering and eventually moving into cloud infrastructure using what researchers describe as living off the cloud (LOTC) methods.
Attack Begins With Social Engineering
The attack began when the threat actors targeted a developer working for the cryptocurrency company. Using social engineering tactics, the attackers convinced the developer to download a compressed archive file as part of what appeared to be a legitimate open source project collaboration.
After downloading the file onto a personal device, the developer later transferred it to their corporate workstation using AirDrop, a peer to peer file sharing feature commonly used on Apple devices.
Once the archive reached the corporate machine, the developer opened and interacted with its contents using an AI assisted Integrated Development Environment (IDE).
This action triggered malicious Python code hidden inside the archive. The script launched a binary program disguised as the Kubernetes command line tool.
Malware Establishes Backdoor Access
The disguised binary immediately contacted a server controlled by the attackers and created a backdoor on the corporate system.
Through this backdoor, attackers were able to move from the compromised workstation into the organization’s Google Cloud environment. They likely leveraged existing authenticated sessions and credentials stored on the developer’s machine.
Once inside the cloud infrastructure, the attackers began an extensive reconnaissance phase to gather information about services, projects, and internal configurations.
Attackers Target Kubernetes Infrastructure
During the reconnaissance process, the attackers discovered a bastion host, a system used for secure access to internal infrastructure.
The threat actors modified the bastion host’s multi factor authentication (MFA) policy attribute to gain access. This allowed them to continue exploring the network and inspect Kubernetes pods running within the cloud environment.
The attackers then shifted to a living off the cloud (LOTC) strategy. Instead of introducing additional malware, they abused legitimate cloud features and administrative workflows.
For persistence, they altered Kubernetes deployment configurations so that a malicious bash command would automatically execute whenever a new pod was created. This command downloaded a hidden backdoor.
Privilege Escalation and Lateral Movement
Further investigation revealed that the attackers manipulated Kubernetes resources connected to the company’s CI/CD platform.
They injected commands that forced the system to print service account tokens into log files. These tokens allowed attackers to authenticate as privileged service accounts.
Using these credentials, the attackers escalated their privileges and moved laterally through the environment. They specifically targeted a Kubernetes pod responsible for handling network policies and load balancing.
The stolen service account token allowed them to authenticate to a privileged infrastructure pod running in privileged mode, enabling them to escape the container environment and deploy another backdoor for long term persistence.
Access to Sensitive Customer Systems
After expanding their access, the attackers conducted additional reconnaissance and eventually located a workload responsible for managing customer account information.
This system handled sensitive data including:
- User identity information
- Account security settings
- Cryptocurrency wallet data
Within this environment, the attackers discovered static database credentials stored insecurely in environment variables.
Using these credentials, they connected to the production database through Cloud SQL Auth Proxy.
Manipulating Accounts to Steal Cryptocurrency
Once connected to the database, the attackers executed SQL commands that altered account security settings.
The changes included:
- Resetting passwords
- Updating multi factor authentication seeds
- Modifying account authentication controls
These modifications allowed the attackers to gain control of several high value accounts belonging to the cryptocurrency platform.
Using the compromised accounts, they successfully withdrew millions of dollars worth of cryptocurrency.
Security Lessons From the Incident
Researchers noted that the attack highlights serious security risks created by personal to corporate file transfer methods such as AirDrop.
When files move directly from personal devices to corporate systems, attackers can bypass many traditional security controls.
The incident also exposed weaknesses in:
- privileged container configurations
- insecure storage of credentials
- insufficient isolation in cloud environments
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


