The Russia linked threat group APT28 has been observed deploying two malware implants, BEARDSHELL and COVENANT, in cyber espionage operations targeting Ukrainian military personnel.
According to a new investigation by ESET, the malware tools have been actively used since April 2024 to maintain persistent access and conduct long term surveillance.
APT28, also widely known by aliases such as Fancy Bear, Sednit, Pawn Storm, and TA422, is believed to operate under Unit 26165 of Russia’s military intelligence agency, the GRU.
SLIMAGENT Malware Used for Data Collection
One of the tools in the group’s arsenal is SLIMAGENT, a spyware implant designed for surveillance and information theft. The malware can perform several data collection functions, including:
- recording keystrokes
- capturing screenshots
- collecting clipboard content
SLIMAGENT was first publicly documented in June 2025 by the CERT‑UA, Ukraine’s national computer emergency response team.
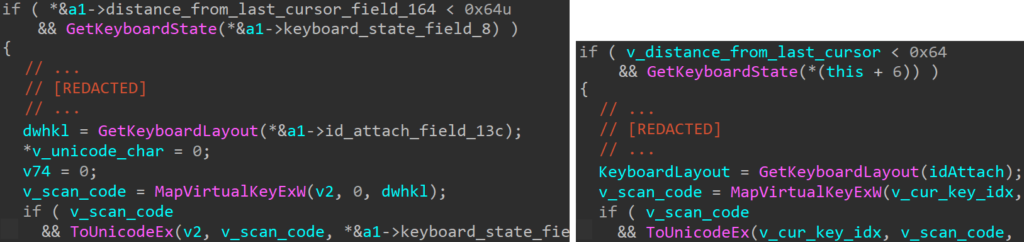
Researchers discovered that SLIMAGENT shares code similarities with XAgent, an older malware implant previously used by APT28 during cyber operations in the 2010s.
Evolution From XAgent Malware
Analysis suggests that SLIMAGENT evolved from XAgent, a well known espionage malware used by the group in earlier campaigns.
Security researchers found overlapping code patterns, especially in the keylogging functionality, between SLIMAGENT and XAgent samples that were discovered in attacks against European government entities as early as 2018.
Both malware families generate espionage logs in HTML format, using a similar color scheme to categorize captured information such as:
- application name
- typed keystrokes
- window titles
This similarity strongly suggests a shared development lineage.
BEARDSHELL Backdoor for Remote Control
Another malware component deployed alongside SLIMAGENT is BEARDSHELL, a backdoor that allows attackers to execute PowerShell commands on compromised systems.
BEARDSHELL communicates with attackers through the cloud storage service Icedrive, which is used as a command and control channel.
Researchers identified a unique obfuscation technique in BEARDSHELL known as opaque predicate, a rare method also seen in the tool XTunnel, which APT28 used during the Democratic National Committee hack.
The reuse of this uncommon technique strengthens the attribution linking BEARDSHELL to APT28’s malware ecosystem.
Modified COVENANT Framework for Espionage
The third major tool used in these operations is COVENANT, an open source .NET post exploitation framework.
Threat actors have heavily customized the framework to support stealthy long term espionage operations. Since July 2025, the modified version has used the cloud storage service Filen as a command and control infrastructure.
Previously, the group relied on other cloud platforms for the same purpose, including:
- pCloud in 2023
- Koofr between 2024 and 2025
Researchers noted that the attackers have gained deep technical expertise in adapting the framework even though its official development stopped in 2021.
Long Standing Dual Malware Strategy
This multi tool espionage approach is not new for APT28.
Security firm Trellix previously reported in 2021 that the group used a similar dual implant strategy involving the Graphite backdoor alongside PowerShell Empire during attacks targeting senior government officials and defense sector personnel in Western Asia.
The latest campaign highlights the group’s continued focus on long term intelligence gathering operations, particularly against Ukrainian military targets.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


