Cybersecurity researchers have uncovered a sophisticated botnet loader named Aeternum C2 that leverages blockchain technology to maintain a resilient and takedown resistant command and control infrastructure. Instead of relying on conventional domains or centralized servers, the malware stores encrypted instructions directly on the Polygon blockchain.
According to research published by Qrator Labs, this strategy enables the botnet to remain operational even when traditional infrastructure is disrupted. By embedding commands within public blockchain transactions, the threat actor ensures persistence that is extremely difficult for law enforcement or hosting providers to dismantle.
Blockchain Powered Command and Control
Aeternum C2 writes its operational commands into smart contracts deployed on the Polygon network. Compromised systems retrieve these instructions by querying public remote procedure call endpoints. Since blockchain transactions are immutable once confirmed, commands cannot be modified or deleted except by the wallet owner controlling the contract.
This tactic is not entirely new. In 2021, Google reported disrupting the Glupteba botnet, which used the Bitcoin blockchain as a backup mechanism for locating its primary command server. However, Aeternum takes the concept further by fully integrating blockchain transactions into its core control mechanism.
The botnet first gained attention in December 2025 when Outpost24’s KrakenLabs revealed that a threat actor known as LenAI was marketing the malware on underground forums. The entry level package reportedly cost $200 and included a management panel and a preconfigured build. A full C++ source code package with updates was allegedly offered for $4,000.
Technical Architecture and Functionality
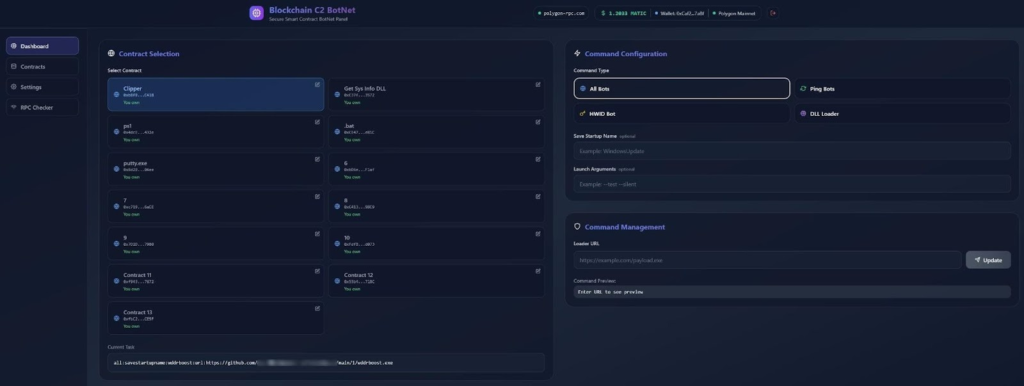
Aeternum is developed in C++ and distributed in both 32 bit and 64 bit variants. Operators manage infections through a web based panel, where they can select smart contracts, define command types, and specify payload URLs. Once a command is submitted, it is recorded as a blockchain transaction and becomes accessible to all infected machines polling the network.
The panel, reportedly built as a Next.js web application, allows operators to deploy smart contracts directly onto the Polygon blockchain. When the malware queries the contract, it retrieves encrypted instructions, decrypts them locally, and executes them on the compromised host.
Operators can maintain multiple smart contracts simultaneously, assigning each one to deliver different malicious payloads such as credential stealers, remote access trojans, cryptocurrency miners, or clipboard hijackers.
Anti Analysis and Low Operational Costs
Beyond its blockchain based infrastructure, Aeternum includes multiple anti analysis mechanisms to extend infection longevity. These include checks for virtualized or sandboxed environments to evade malware researchers.
Customers are also reportedly encouraged to scan their custom builds through online services such as Kleenscan to ensure they remain undetected by antivirus solutions.
Operational costs are minimal. Researchers noted that approximately one dollar worth of MATIC tokens, the native cryptocurrency of the Polygon network, is sufficient to conduct between 100 and 150 command transactions. Since operators do not need to lease servers, register domains, or maintain hosting infrastructure, their only requirements are a cryptocurrency wallet and a local control panel.
The threat actor later attempted to sell the complete toolkit for $10,000, citing limited availability for ongoing support and involvement in other projects.
Links to Additional Crimeware Operations
Investigations indicate that LenAI is also associated with another malicious toolkit called ErrTraffic, designed to automate ClickFix style attacks. These attacks generate fake error messages or website glitches to create urgency and trick users into executing malicious instructions.
In parallel developments, cybersecurity firm Infrawatch disclosed an underground operation named DSLRoot. This service deploys dedicated laptop hardware into residential homes across the United States, converting them into part of a residential proxy network.
The deployed devices reportedly run a Delphi based program known as DSLPylon, capable of identifying supported modems on local networks and remotely managing residential routers and Android devices using Android Debug Bridge (ADB) integration.
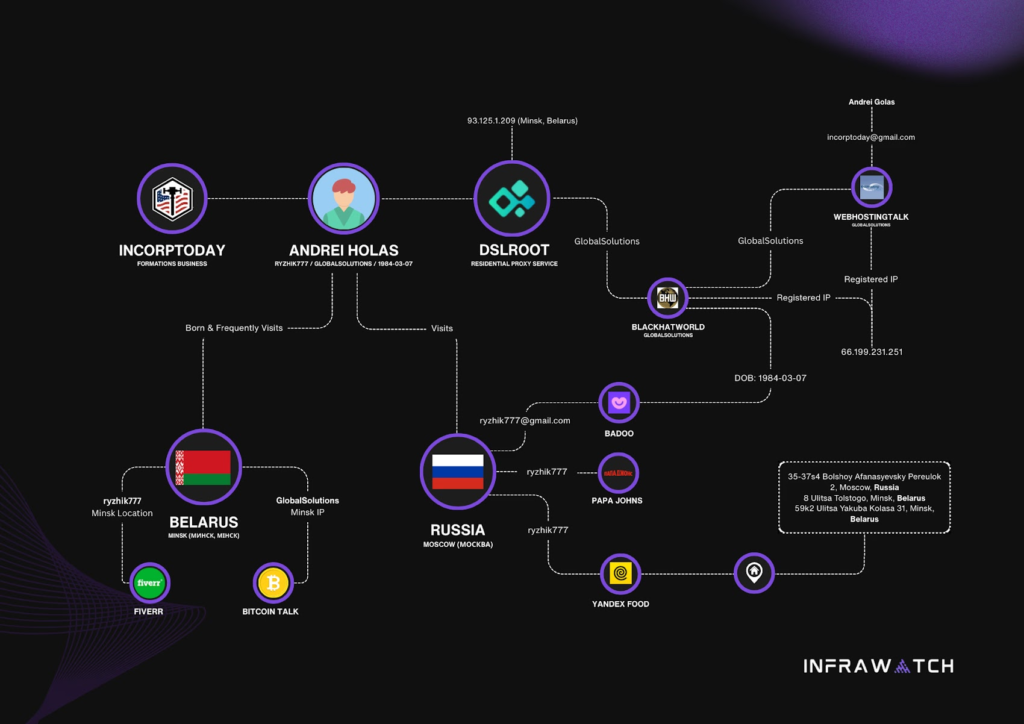
Attribution analysis suggests the DSLRoot operation is linked to an individual identified as Andrei Holas, also known under alternate spellings. The service has been advertised on underground forums offering U.S. residential ADSL proxy access on a subscription basis.
Researchers estimate that roughly 300 active hardware devices are distributed across more than 20 U.S. states, enabling clients to route traffic through residential IP addresses without authentication. Such infrastructure significantly complicates attribution and detection efforts for malicious campaigns.
Growing Trend of Decentralized Botnet Infrastructure
The emergence of Aeternum C2 highlights a broader evolution in cybercrime tactics. By integrating decentralized blockchain platforms into malware command systems, threat actors are creating infrastructures that are persistent, low cost, and highly resistant to traditional takedown operations.
As blockchain adoption expands across legitimate industries, security researchers warn that similar abuse cases are likely to increase, further complicating global cyber defense strategies.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.