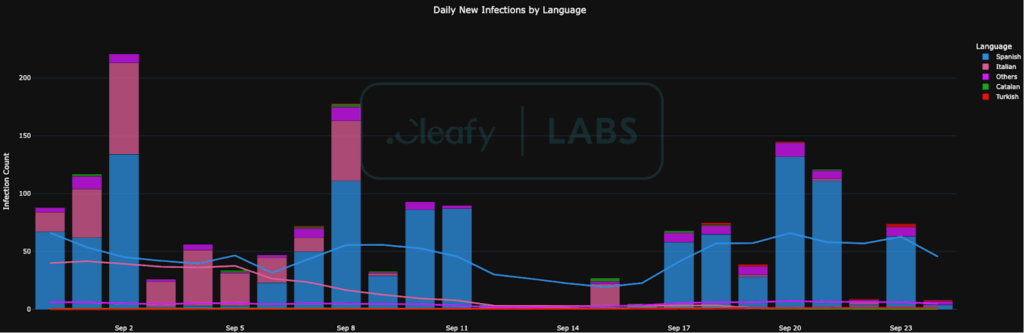
A newly discovered Android banking trojan named Klopatra has infected more than 3,000 devices, with the majority of cases reported in Spain and Italy. The malware, identified by the Italian fraud prevention company Cleafy in late August 2025, is a sophisticated remote access trojan (RAT) that leverages Hidden Virtual Network Computing (VNC) for remote control, enabling attackers to steal credentials and execute fraudulent transactions.
A New Standard in Mobile Malware
Security researchers Federico Valentini, Alessandro Strino, Simone Mattia, and Michele Roviello described Klopatra as a major leap in Android malware evolution. Unlike typical trojans, it integrates native libraries with Virbox, a commercial-grade code protection suite. This makes the malware far more resistant to detection and analysis compared to older banking trojans.
Evidence from the malware’s command-and-control (C2) servers and language artifacts points toward a Turkish-speaking criminal group operating it as a private botnet, since no public malware-as-a-service (MaaS) offering has been observed. Researchers have already identified over 40 different builds of Klopatra since March 2025.
Social Engineering Distribution
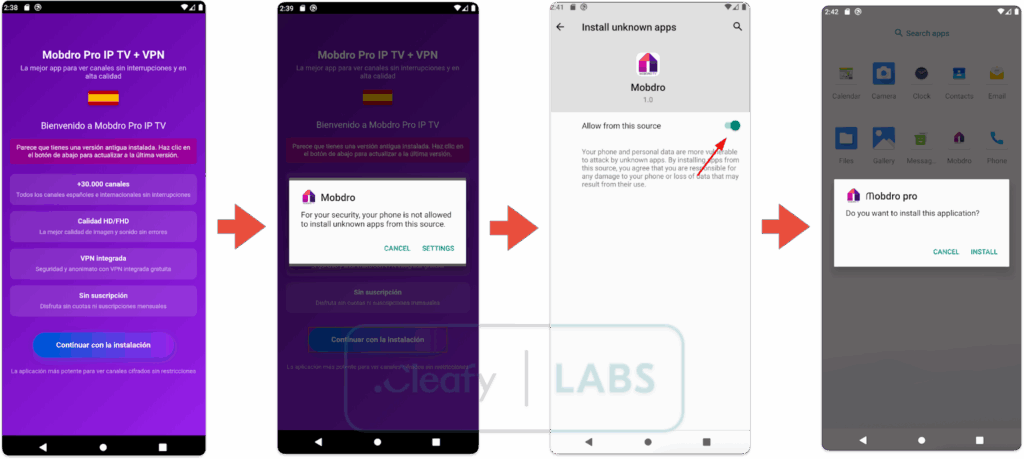
The malware spreads through dropper apps disguised as everyday tools, such as IPTV applications. These apps lure users by promising free access to premium TV channels, a popular bait among those who frequently install apps from unofficial sources. Once downloaded, the dropper requests permission to install packages from unknown sources. After gaining access, it extracts and installs the Klopatra payload hidden within a JSON Packer.
Similar to other banking trojans, Klopatra abuses Android accessibility services. While this feature is designed to assist users with disabilities, cybercriminals weaponize it to read screen content, record keystrokes, and perform actions on behalf of the user.
Advanced Stealth and Resilience
What sets Klopatra apart is its architecture built for stealth and persistence. By shifting many functions from Java to native code, the malware reduces visibility to traditional analysis systems. In addition, it uses code obfuscation, anti-debugging methods, and runtime integrity checks to make reverse-engineering extremely difficult.
The use of VNC capabilities allows attackers to control infected devices in real time. This includes showing victims a black screen overlay while secretly executing banking transactions in the background.
Persistence and Fraud Techniques
Once installed, Klopatra grants itself extra permissions and attempts to uninstall antivirus apps hard-coded into its list of targets. It also deploys fake login overlays over financial and crypto apps to steal credentials. These overlays are sent dynamically from the C2 server whenever the victim opens a targeted application.
Researchers noted that fraud operators often act in a carefully orchestrated sequence. For instance, if a device is charging, the screen is off, and no user activity is detected, Klopatra dims the screen to zero brightness and applies a fake black overlay. The attackers then unlock the phone using a stolen PIN or pattern, open the banking app, and transfer money without the victim’s knowledge.
A Professional-Grade Threat
Cleafy’s report emphasizes that Klopatra signals a new stage in the professionalization of mobile malware. Its use of commercial-grade tools and advanced evasion techniques shows that attackers are investing heavily in long-term operations and profitability. Moreover, operators often schedule their attacks at night, when victims are asleep, ensuring minimal risk of detection.
This discovery follows another case flagged by ThreatFabric, which identified the Android trojan Datzbro capable of device takeover (DTO) attacks targeting elderly users.
Google’s Response
After the report was published, a Google spokesperson confirmed that no apps containing Klopatra have been found on Google Play. They added that Google Play Protect, which is enabled by default on devices with Google Play Services, automatically blocks or warns users about known malicious apps, even those downloaded from outside the Play Store.