Cybersecurity researchers have uncovered six new Android malware families designed to steal sensitive data from infected devices and carry out financial fraud. These threats primarily target banking applications, cryptocurrency wallets, and digital payment platforms.
The discovered malware includes several banking trojans and remote access tools capable of monitoring user activity, hijacking financial transactions, and gaining full control over infected smartphones.
Malware Families Identified
Researchers identified the following Android threats:
While some function as traditional banking trojans, others operate as full remote administration tools (RATs) capable of controlling devices remotely.
PixRevolution Targets Brazil’s Pix Payment System
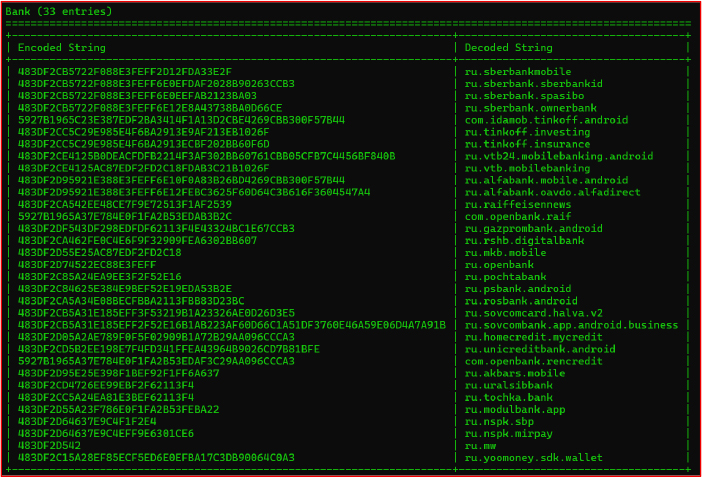
One of the most notable threats, PixRevolution, specifically targets Brazil’s widely used Pix instant payment platform.
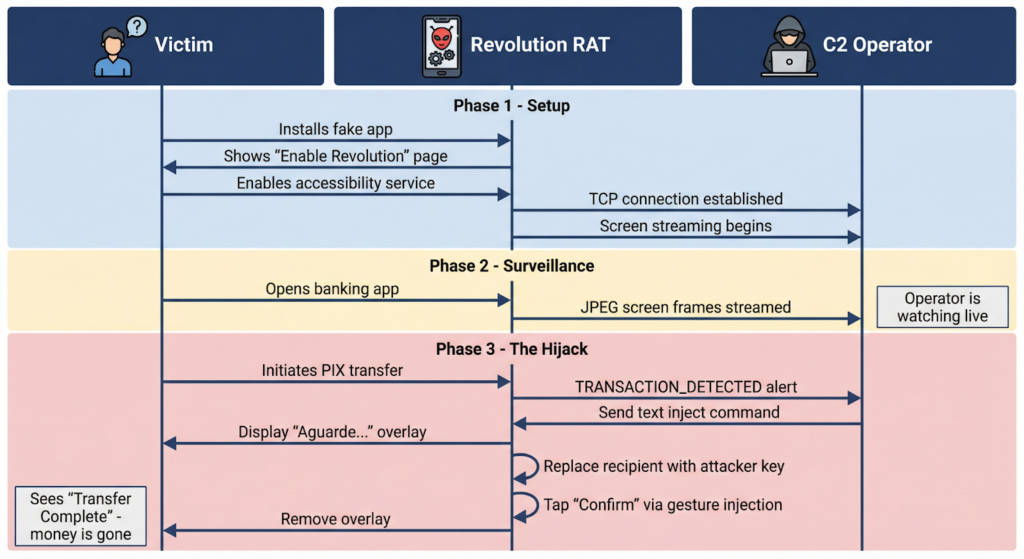
The malware remains hidden on the device until a victim initiates a Pix transaction. At that moment, attackers remotely monitor the screen and intervene during the transfer process.
According to researchers, the attacker may actively observe the victim’s device in real time and modify the payment details before the transaction is completed.
The infection often begins when users download fake applications from websites that imitate official Google Play Store pages. These fake pages advertise well known services such as Expedia, Sicredi, or Correios to trick users into installing malicious APK files.
Once installed, the malware asks victims to enable Android accessibility services, allowing it to monitor the screen and manipulate actions.
When the user attempts to send money through Pix, the malware displays a fake overlay showing a loading message. While the victim sees the loading screen, the malware silently replaces the recipient’s Pix key with the attacker’s account.
Because Pix payments are instant and irreversible, victims may only realize the fraud long after the money has been transferred.
BeatBanker Uses Unusual Persistence Method
Another campaign targeting Brazilian users involves the BeatBanker Android malware.
This threat spreads mainly through phishing websites that mimic the Google Play Store. One unusual technique used by BeatBanker to remain active on infected devices is the continuous playback of an almost inaudible audio file.
This looping audio prevents the operating system from shutting down the malicious process.
The malware also includes several advanced capabilities:
- Monitoring device battery conditions
- Detecting analysis environments or emulators
- Running a cryptocurrency mining component
- Performing banking overlays to steal credentials
For example, when a victim attempts a USDT transaction, BeatBanker may display fake pages for platforms like Binance or Trust Wallet while secretly replacing the wallet address with one controlled by attackers.
TaxiSpy RAT Enables Full Device Surveillance
TaxiSpy RAT combines banking trojan functions with full remote access capabilities.
The malware abuses accessibility services and Android’s MediaProjection API to collect large amounts of data from infected devices, including:
- SMS messages
- Call logs
- Contacts
- Clipboard data
- Installed applications
- Notifications
- Lock screen PIN codes
- Keystrokes
Researchers found that the malware can also create overlays targeting banking, cryptocurrency, and government applications to steal login credentials.
Mirax and Oblivion Offered as Malware Services
Another banking trojan called Mirax is being marketed on underground forums as a Malware as a Service (MaaS) platform.
The full version reportedly costs about $2,500 per month, while a lighter version costs around $1,750 monthly. Mirax includes features such as credential harvesting, banking overlays, and a SOCKS5 proxy that routes malicious traffic through compromised devices.
Similarly, Oblivion RAT is being sold through subscription plans starting at roughly $300 per month. The malware claims to bypass security restrictions across multiple Android operating systems including:
- Xiaomi MIUI and HyperOS
- Samsung One UI
- OPPO ColorOS
- Honor MagicOS
- OnePlus OxygenOS
One notable feature is its automated permission granting mechanism that requires minimal interaction from victims.
SURXRAT Distributed Through Telegram Malware Marketplace
Another Android malware family called SURXRAT is reportedly distributed through a Telegram based MaaS ecosystem and is believed to be an improved variant of the Arsink malware framework.
SURXRAT abuses accessibility permissions to maintain persistent control over infected devices and communicates with attackers through a Firebase based command and control infrastructure.
Some variants even include ransomware style screen locking capabilities, allowing attackers to block access to the device until a payment is made.
AI Components Appearing in Android Malware
Researchers also discovered that some malware samples include a large language model (LLM) component, suggesting that threat actors are experimenting with artificial intelligence to enhance their attacks.
Interestingly, the AI module only activates under specific conditions, such as when certain gaming apps are installed on the victim’s device.
This trend highlights how cybercriminals are increasingly combining traditional malware techniques with emerging AI technologies to improve surveillance, automation, and evasion.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


