Cybersecurity experts have uncovered two dangerous Android spyware campaigns known as ProSpy and ToSpy, targeting users in the United Arab Emirates (U.A.E.). These malicious campaigns disguise themselves as popular apps such as Signal Encryption Plugin and ToTok Pro to trick unsuspecting victims into installing spyware on their devices.
Fake Apps and Distribution Tactics
According to Slovak cybersecurity company ESET, the malware is distributed through fraudulent websites and social engineering tactics. Victims are lured into manually installing the infected APK files, believing they are downloading legitimate app upgrades.
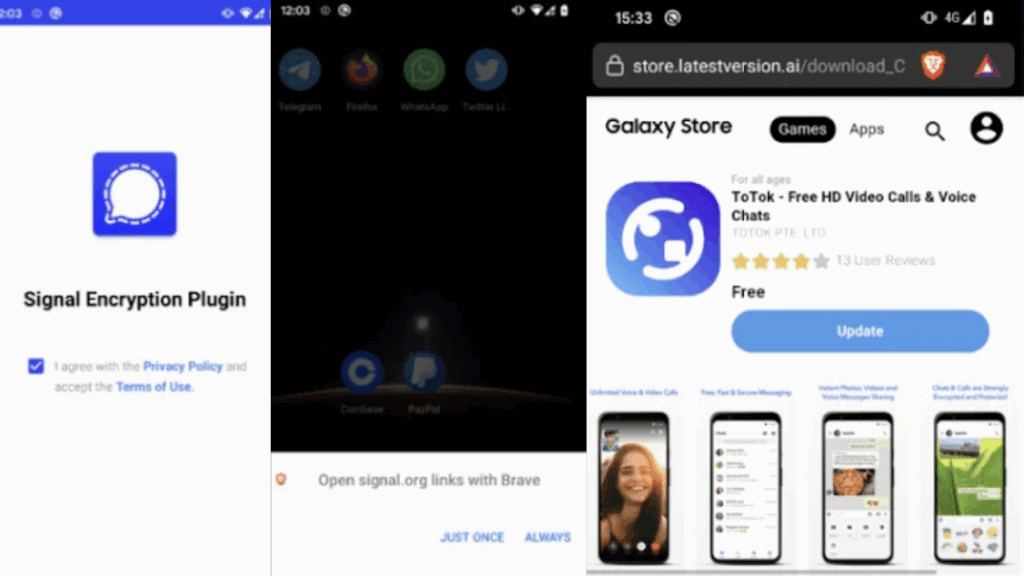
- The ProSpy campaign, first identified in June 2025, has been active since 2024. It spreads through fake websites imitating Signal and ToTok, offering manipulated APK files that appear to be app enhancements.
- The ToSpy campaign is believed to have started in June 2022 and continues to this day. It uses fake sites imitating ToTok to distribute spyware.
Notably, these malicious applications were never available on official app stores like Google Play or Apple App Store, making manual installation from third-party sources the only infection vector.
Exploiting ToTok’s Controversial History
The attackers deliberately exploit the reputation of ToTok, a messaging app banned from Google Play and the Apple App Store in December 2019 due to allegations of government surveillance in the U.A.E. At the time, the app was accused of secretly collecting users’ conversations, locations, and personal data.
Despite the developers denying the accusations, cybercriminals now leverage the app’s notoriety to make their fake versions appear more convincing.
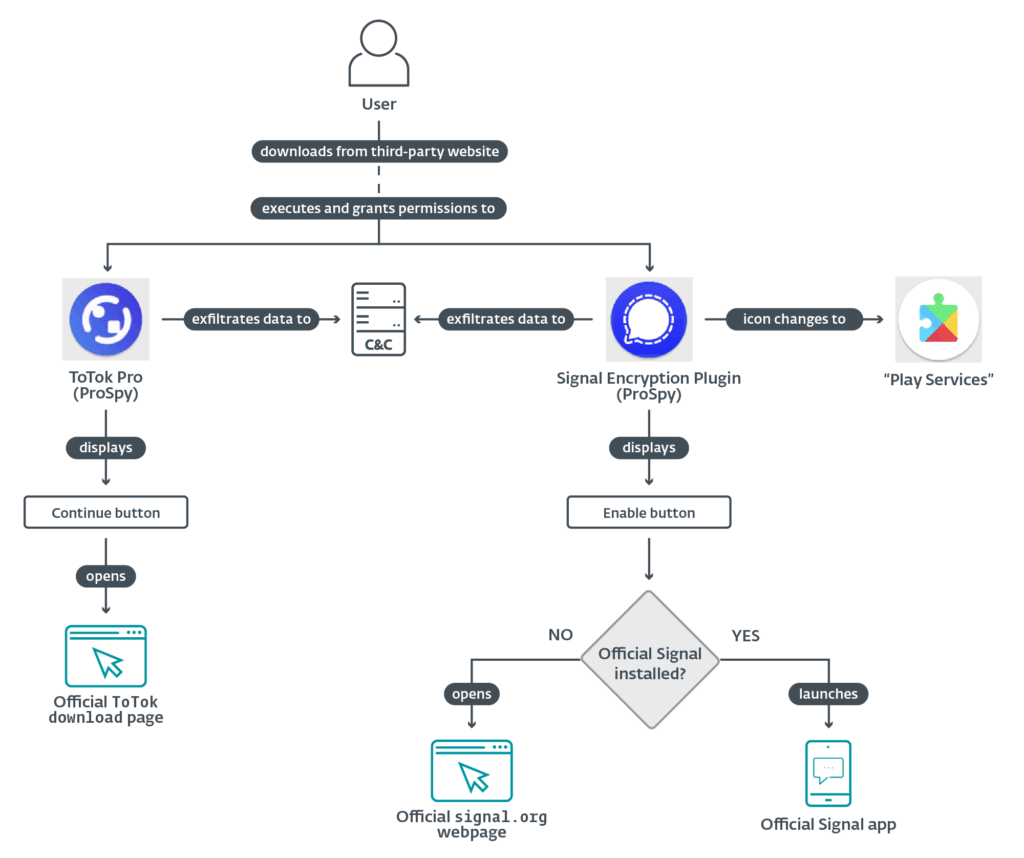
How ProSpy Works
The rogue ProSpy apps aggressively request device permissions, including:
- Access to contacts
- SMS messages
- File storage
- Device information
Once granted, the spyware silently extracts sensitive data. To maintain legitimacy, ProSpy’s fake ToTok Pro app displays a “CONTINUE” button that redirects users to the official ToTok download page. This creates the illusion of authenticity while still running spyware in the background.
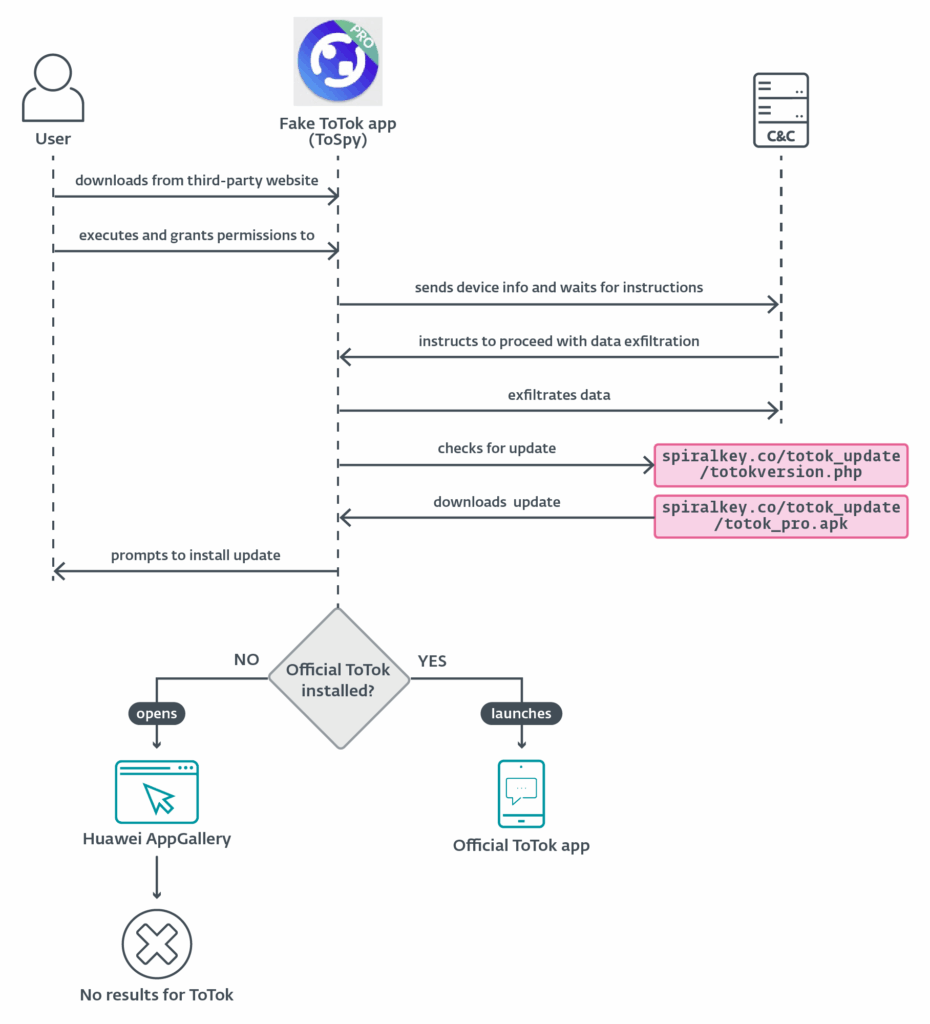
How ToSpy Deceives Users
The ToSpy malware also employs deception. Depending on whether the real ToTok app is installed, ToSpy behaves differently:
- If ToTok is not installed, it redirects victims to Huawei AppGallery or the browser to download the official app.
- If ToTok is already installed, ToSpy shows a fake update-checking screen before silently launching the real app.
In both cases, spyware runs in the background, stealing contacts, sensitive files, device details, and ToTok data backups (*.ttkmbackup).
Persistence and Stealth Mechanisms
Both spyware families employ advanced persistence tactics to avoid detection:
- Running as a foreground service with a persistent notification
- Using AlarmManager to restart services if terminated
- Relaunching background services after device reboot
These strategies ensure the malware continues spying on victims even if they attempt to shut it down.
The Bigger Picture
ESET researchers note that while ProSpy and ToSpy share similarities, they are being tracked separately due to differences in delivery infrastructure and methods. The actual threat actors behind the campaigns remain unknown.
Recommendations for Users
To reduce the risk of infection, users are strongly advised to:
- Avoid downloading apps from unofficial sources
- Disable installation from unknown origins in Android settings
- Only install applications from Google Play, Apple App Store, or official vendor websites
- Remain cautious of apps claiming to be plugins or enhancements for trusted services
ESET emphasized, “Any future launches of these malicious apps open the legitimate versions, creating an illusion of safety, while spyware continues to operate in the background.”