A newly identified hacking cluster known as ShadowSilk has been linked to a wave of cyber intrusions aimed at government agencies in Central Asia and the Asia-Pacific (APAC) region.
Rising Campaigns and Overlaps with Other Groups
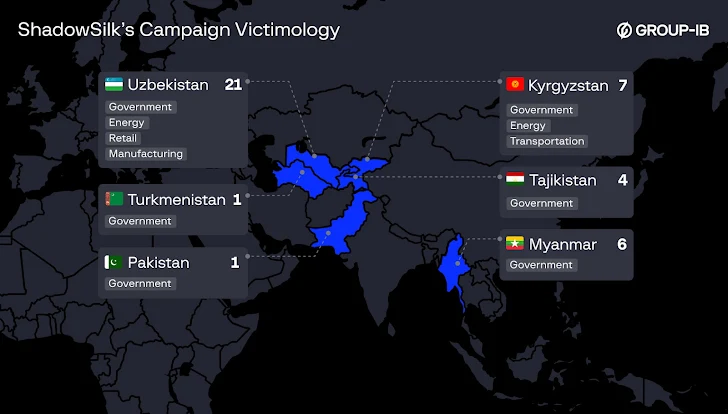
Group-IB reports that nearly 36 victims have been confirmed so far, with attackers primarily focused on stealing sensitive data. Investigations reveal overlaps in tools and infrastructure with previously known cyber groups including YoroTrooper, SturgeonPhisher, and Silent Lynx.
The targeted entities include government organizations in Uzbekistan, Kyrgyzstan, Myanmar, Tajikistan, Pakistan, and Turkmenistan. Non-government sectors such as energy, transportation, retail, and manufacturing were also affected.
Researchers Nikita Rostovcev and Sergei Turner described the operation as a collaboration between Russian-speaking developers (linked to YoroTrooper’s older code) and Chinese-speaking intrusion operators, creating a multi-regional threat presence. However, the full extent of cooperation between the sub-groups is still unclear.
Historical Background of Related Groups
- YoroTrooper was first exposed by Cisco Talos in March 2023. It had been conducting cyber attacks on European government and energy organizations since mid-2022, with activity possibly starting as early as 2021 according to ESET.
- Later research suggested that some YoroTrooper members were based in Kazakhstan, as indicated by their fluency in Kazakh and Russian, alongside a noticeable absence of attacks against Kazakh targets.
- In January this year, Seqrite Labs revealed cyber campaigns from Silent Lynx, which targeted organizations in Kyrgyzstan and Turkmenistan, again showing links to YoroTrooper operations.
Attack Techniques and Tools
ShadowSilk’s latest operations rely heavily on spear-phishing emails as the initial attack vector. Victims receive password-protected archive files that launch a custom loader, which hides C2 traffic inside Telegram bots to bypass detection and download further payloads. Persistence is achieved by altering Windows Registry entries to ensure malware runs automatically after system reboot.
Image import
The group also exploits known vulnerabilities including:
- Drupal exploits (CVE-2018-7600, CVE-2018-76020)
- WP-Automatic WordPress plugin exploit (CVE-2024-27956)
Its toolkit includes FOFA, Fscan, Gobuster, Dirsearch, Metasploit, and Cobalt Strike. Additionally, ShadowSilk integrates JRAT and Morf Project web panels (sourced from darknet forums) for managing compromised systems. A specialized tool is also used to steal Google Chrome password storage files along with their decryption keys.
The attackers often compromise legitimate websites to host malicious payloads, further complicating detection.
Post-Exploitation and Data Theft
Once inside, the group uses web shells (ANTSWORD, Behinder, Godzilla, FinalShell), Sharp-based exploitation tools, and tunneling software like Resocks and Chisel to move laterally, escalate privileges, and extract sensitive data.
The attacks eventually deploy a Python-based Remote Access Trojan (RAT) that communicates with a Telegram bot, disguising data exfiltration as normal messaging traffic. Tools like Cobalt Strike and Metasploit modules enable screen captures and webcam surveillance. A custom PowerShell script scans for files with specific extensions, compresses them into ZIP archives, and sends them to external servers.
Evidence of Chinese Operator Involvement
While Group-IB confirms that YoroTrooper developers are fluent in Russian, screenshots from an attacker’s workstation revealed evidence of Chinese-speaking operators. Findings included:
- Chinese vulnerability scanners
- Automatic translations of Kyrgyz government websites into Chinese
- Chinese keyboard layouts in use
This suggests a joint operation between Russian and Chinese speakers, with one side handling malware development and the other carrying out active intrusions.
Ongoing Activity
Group-IB notes that ShadowSilk remains highly active, with new victims identified as recently as July 2025. The group continues to target government sectors across Central Asia and APAC, highlighting the urgent need for infrastructure monitoring, proactive defense, and long-term compromise prevention.


