A suspected China-linked cyber threat group known as APT24 has been actively deploying a previously undocumented malware called BADAUDIO as part of a prolonged espionage campaign. The operation, ongoing for nearly three years, has targeted organizations in Taiwan and compromised over 1,000 domains.
Google Threat Intelligence Group (GTIG) researchers Harsh Parashar, Tierra Duncan, and Dan Perez noted that APT24 has shifted from broad website compromises to more sophisticated, targeted attacks. These include phishing campaigns and repeated compromise of a regional digital marketing firm to execute supply chain attacks.
APT24, also known as Pitty Tiger, has historically targeted sectors such as government, healthcare, engineering, mining, nonprofits, and telecommunications in Taiwan and the United States. Earlier malware used by the group includes CT RAT, MM RAT (Goldsun-B), variants of Gh0st RAT (Paladin RAT, Leo RAT), and backdoors like Taidoor (Roudan).
BADAUDIO Malware Overview
BADAUDIO is a highly obfuscated C++ malware designed to resist reverse engineering. It functions as a first-stage downloader capable of fetching, decrypting, and executing an AES-encrypted payload from a hard-coded command and control (C2) server. The malware collects basic system information and sends it to the C2 server, which responds with the payload to execute. In some cases, the payload included Cobalt Strike Beacon.
Typically, BADAUDIO manifests as a malicious DLL leveraging DLL Search Order Hijacking (MITRE ATT&CK T1574.001) and uses encrypted archives containing DLLs, VBS, BAT, and LNK files for execution.
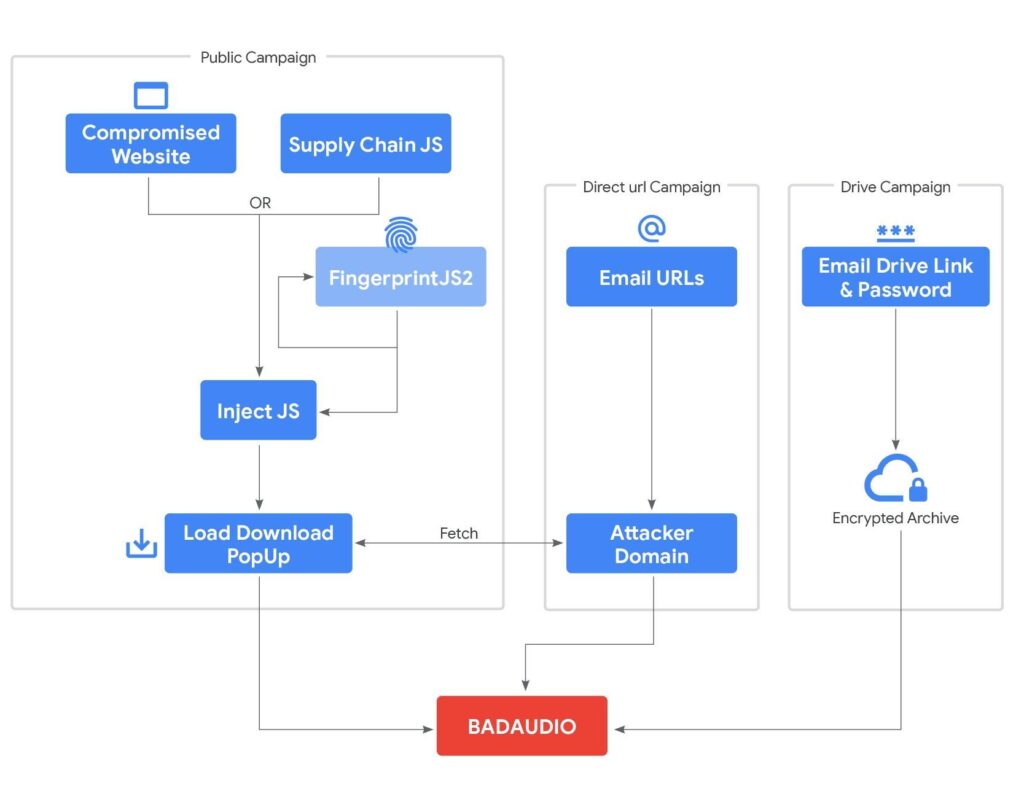
From November 2022 to early September 2025, APT24 compromised more than 20 legitimate websites, injecting malicious JavaScript to selectively target non-macOS, iOS, and Android visitors, generate browser fingerprints using FingerprintJS, and deliver a fake pop-up prompting users to download BADAUDIO as a supposed Chrome update.
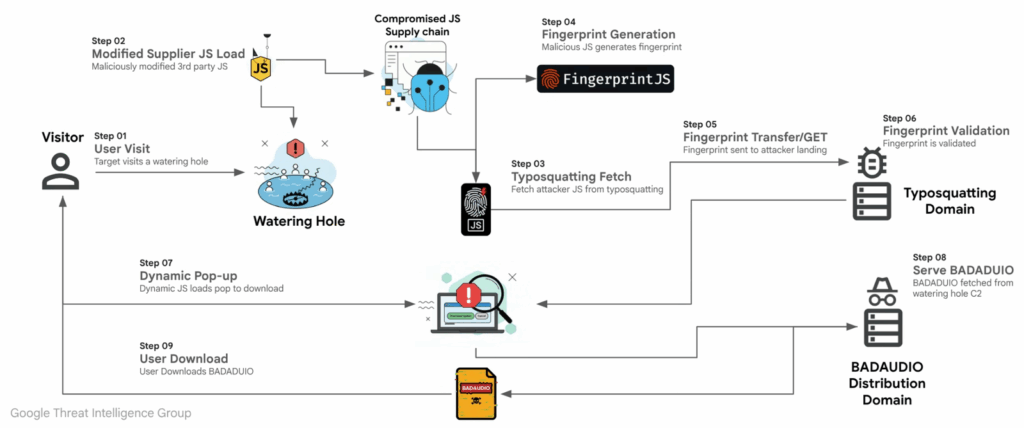
Starting in July 2024, APT24 compromised a regional digital marketing firm in Taiwan, injecting malicious scripts into a widely used JavaScript library. This allowed the attackers to compromise over 1,000 domains through the supply chain attack. The modified script contacted a typosquatted CDN to fetch attacker-controlled JavaScript, fingerprint the victim machine, and deliver a pop-up for BADAUDIO download.
GTIG reported that in June 2025, conditional script loading based on unique web IDs limited attacks to a single domain, but a ten-day lapse in August 2025 temporarily allowed all 1,000 domains to be affected.
Targeted Phishing Campaigns
APT24 has conducted spear-phishing since August 2024, using lures related to animal rescue organizations. Encrypted archives hosted on Google Drive and Microsoft OneDrive delivered BADAUDIO, with tracking pixels confirming whether targets opened the emails.
These operations combine supply chain compromises, advanced social engineering, and abuse of legitimate cloud services, demonstrating APT24’s persistence and sophistication.
Additional Regional Threat Activity
Separately, a China-linked APT actor conducted a campaign dubbed Autumn Dragon, targeting government, media, and news sectors in Southeast Asia, including Laos, Cambodia, Singapore, the Philippines, and Indonesia. The attacks used spear-phishing with RAR attachments exploiting WinRAR CVE-2025-8088 (CVSS 8.8) and executed batch scripts to establish persistence and download further payloads via PowerShell from cloud hosting.
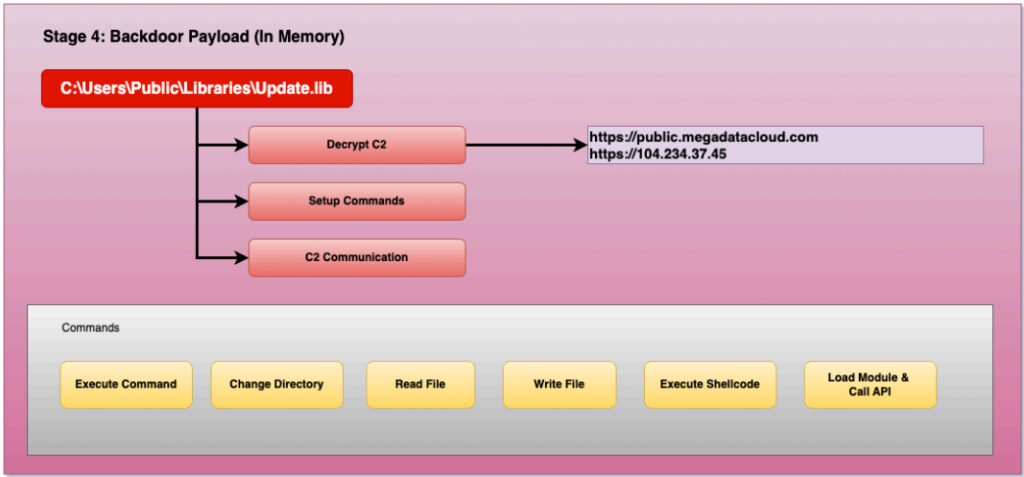
The third stage involved DLL sideloading using legitimate binaries to deploy a lightweight C++ implant that communicates with public.megadatacloud[.]com. The malware supports commands including executing shellcode, running DLLs, reading and writing files, updating configurations, and exfiltrating data.
Targeted, Geo-Restricted Campaigns
Researchers noted that the attacks use geo-restrictions, Cloudflare hosting, and HTTP user agent filtering to limit detection. This targeting, combined with multi-stage malware deployment, underscores the intermediate operational capabilities of the group, likely linked to China-nexus operations.