A high severity Microsoft vulnerability patched during February 2026 Patch Tuesday may have been actively exploited by the Russia linked threat group APT28, according to new research from Akamai.
The flaw, tracked as CVE-2026-21513 with a CVSS score of 8.8, affects the MSHTML Framework and enables attackers to bypass key Windows security protections.
Microsoft described the issue as a protection mechanism failure within MSHTML that allows an unauthorized attacker to bypass a security feature over a network. Although the vulnerability was fixed in February 2026 updates, Microsoft confirmed that it had already been exploited as a zero day in the wild.
The vulnerability was reported by multiple security teams, including Microsoft Threat Intelligence Center, Microsoft Security Response Center, Office Product Group Security Team, and Google Threat Intelligence Group.
How the MSHTML Zero Day Attack Works
In a typical attack scenario, a threat actor could trick a victim into opening a malicious HTML file or a specially crafted Windows shortcut file, LNK, delivered through phishing emails or embedded links.
Once opened, the file manipulates how the browser and Windows Shell process the content. This forces the operating system to execute attacker controlled content, enabling the bypass of built in security protections and potentially leading to remote code execution.
While Microsoft has not publicly disclosed technical details about the exploitation chain, Akamai researchers identified a suspicious file uploaded to VirusTotal on January 30, 2026. The infrastructure associated with this artifact has been linked to APT28.
Connection to APT28 and CERT UA Findings
The identified sample had previously been flagged by the Computer Emergency Response Team of Ukraine, CERT UA, in relation to APT28 operations exploiting another Microsoft Office vulnerability, CVE-2026-21509 with a CVSS score of 7.8.
APT28, widely associated with Russian state sponsored cyber operations, has a long history of targeting government entities, defense organizations, and critical infrastructure.
Technical Root Cause in ieframe.dll
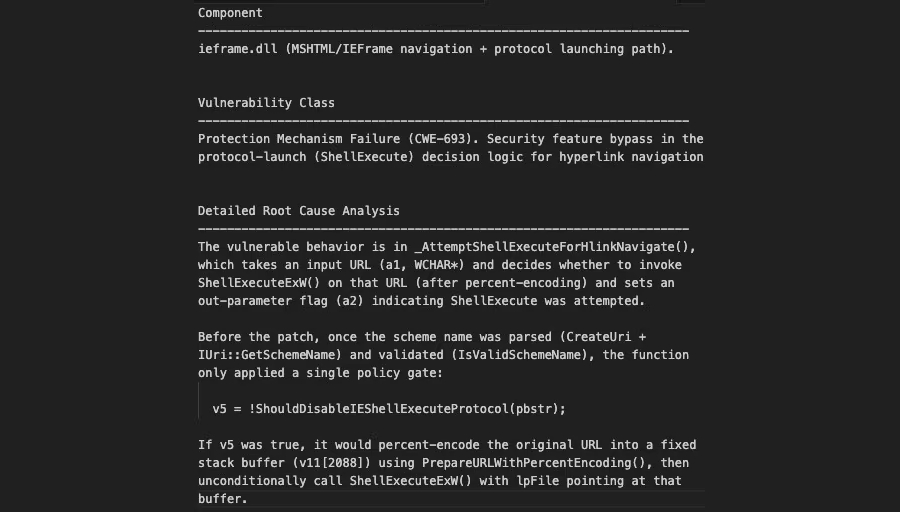
Akamai’s analysis revealed that CVE-2026-21513 originates from flawed logic in ieframe.dll, specifically in the component responsible for hyperlink navigation.
The vulnerability stems from inadequate validation of target URLs. This weakness allows attacker controlled input to reach execution paths that invoke ShellExecuteExW, a Windows API function capable of launching local or remote resources.
Security researcher Maor Dahan explained that the exploit involves a specially constructed LNK file containing an embedded HTML file appended after the normal shortcut structure. When executed, the shortcut connects to wellnesscaremed[.]com, infrastructure attributed to APT28 and used in multi stage attack campaigns.
The exploit chain uses nested iframes and multiple Document Object Model contexts to manipulate browser trust boundaries and force unintended execution behavior.
Bypassing Mark of the Web and IE ESC
Akamai reported that this technique enables attackers to bypass Mark of the Web (MotW) and Internet Explorer Enhanced Security Configuration (IE ESC) protections.
By downgrading the security context, attackers can execute malicious code outside the browser sandbox using ShellExecuteExW. This significantly increases the risk of full system compromise.
Although the observed campaign relied on malicious LNK files, researchers warned that any application embedding MSHTML could potentially trigger the vulnerable code path. This means additional delivery methods beyond LNK phishing should be anticipated.
Security Implications and Enterprise Risk
The exploitation of CVE-2026-21513 highlights ongoing risks associated with legacy browser components embedded within Windows systems.
Organizations are strongly advised to ensure that February 2026 security updates are fully deployed across all endpoints. Additional mitigations include restricting execution of LNK files from untrusted sources, enhancing email filtering controls, and monitoring outbound connections to suspicious domains.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


