The Russian state sponsored cyber threat actor widely known as APT28 has been linked to a long running credential harvesting campaign aimed at users of UKR[.]net, a popular Ukrainian webmail and news service. The activity was uncovered by the Insikt Group, the threat intelligence division of Recorded Future, and was observed between June 2024 and April 2025.
Researchers noted that this campaign builds on earlier findings published in May 2024, which detailed attacks against European targets involving the HeadLace malware and credential stealing phishing pages. The latest activity reflects continuity in both objectives and operational tradecraft.
APT28 is tracked under several aliases including BlueDelta, Fancy Bear, Forest Blizzard, FROZENLAKE, Iron Twilight, ITG05, Pawn Storm, Sednit, Sofacy, and TA422. The group is assessed to be linked with Russia’s military intelligence agency, the Main Directorate of the General Staff of the Armed Forces of the Russian Federation, commonly referred to as the GRU.
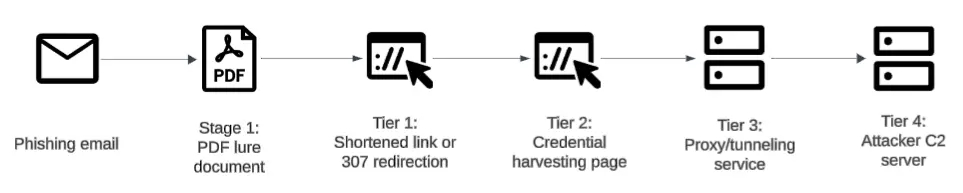
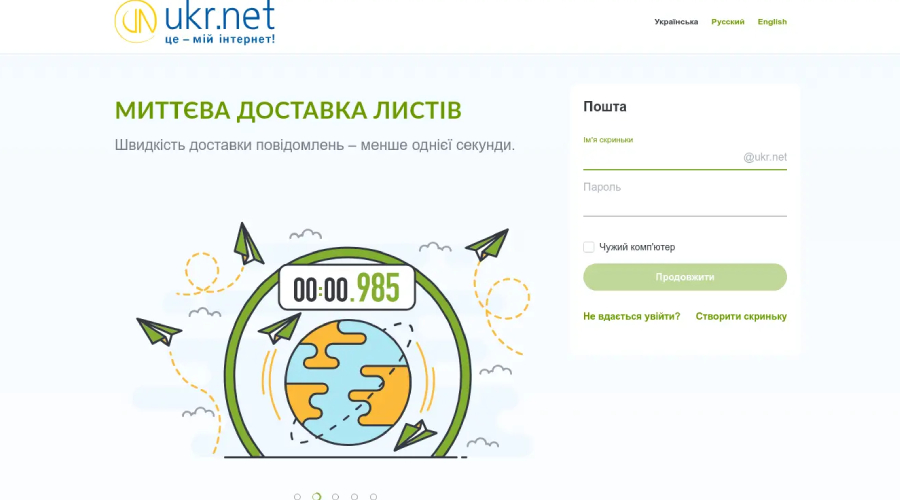
According to investigators, the recent attacks rely on fake UKR[.]net themed login pages hosted on legitimate online services such as Mocky. Victims are lured into entering their email credentials and two factor authentication codes. Access to these phishing pages is delivered through links embedded inside PDF files sent via phishing emails.
To further obscure the infrastructure, the malicious links are shortened using services like tiny[.]cc and tinyurl[.]com. In other instances, the attackers have created subdomains on platforms such as Blogger to establish a two step redirection chain that ultimately leads to the credential harvesting page.
The campaign is part of a much broader phishing and credential theft effort that APT28 has conducted since the mid 2000s. Historically, these operations have targeted government bodies, defense contractors, arms suppliers, logistics companies, and policy focused think tanks in support of Russian strategic and intelligence objectives.
In commentary shared with The Hacker News, analysts from the Mastercard owned Recorded Future emphasized that while specific victims are not publicly named, the intent is clear. The group’s long standing reliance on credential theft strongly suggests an effort to collect sensitive information from Ukrainian users to meet broader GRU intelligence requirements.
One notable evolution in this campaign is the shift away from using compromised routers toward proxy tunneling services such as ngrok and Serveo. These tools are used to capture and relay stolen credentials and 2FA codes in real time.
Researchers concluded that the continued abuse of free hosting platforms and anonymized tunneling services reflects an adaptive response to infrastructure takedowns carried out by Western authorities in early 2024. The campaign underscores the persistent interest of Russian intelligence in compromising Ukrainian user accounts amid the ongoing war in Ukraine.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


