A Pakistan-linked threat actor, identified as Transparent Tribe (APT36), has been observed launching spear-phishing attacks against Indian government entities using a Golang-based remote access trojan (RAT) called DeskRAT. The campaign, active during August and September 2025, continues a series of operations first highlighted by CYFIRMA in August 2025 and now monitored by Sekoia.
Attack Methodology
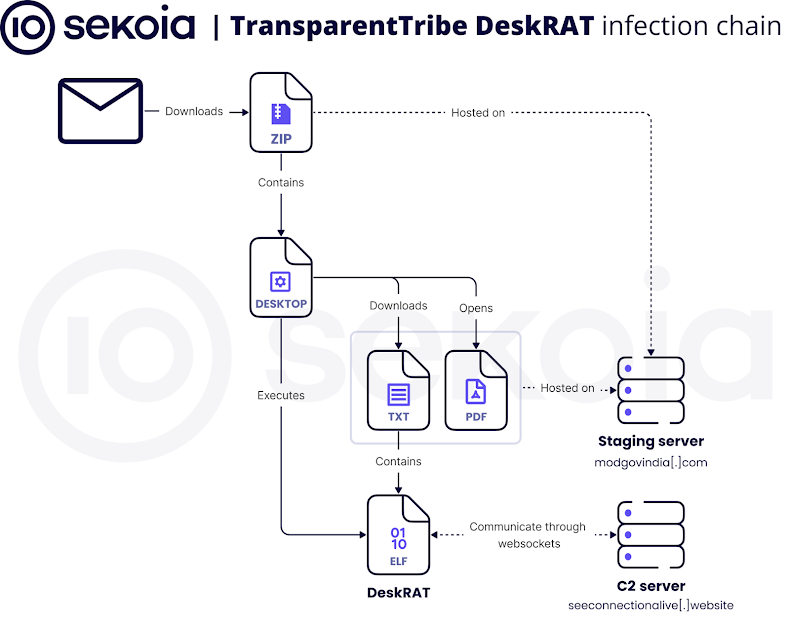
The attackers typically send phishing emails containing either a ZIP file or a link to an archive hosted on legitimate cloud platforms like Google Drive. The ZIP file includes a malicious Desktop file that launches a decoy PDF, “CDS_Directive_Armed_Forces.pdf”, via Mozilla Firefox while simultaneously executing the main DeskRAT payload. Both components are retrieved from modgovindia[.]com for execution.
The campaign specifically targets BOSS Linux systems, and the malware establishes a command-and-control (C2) channel using WebSockets. DeskRAT supports four persistence techniques:
- Creating a systemd service
- Setting up a cron job
- Adding itself to the Linux autostart directory (“$HOME/.config/autostart”)
- Modifying .bashrc to execute via a shell script in “$HOME/.config/system-backup/”
Capabilities of DeskRAT
DeskRAT can execute five main commands:
- ping – sends a JSON timestamp along with “pong” to the C2 server
- heartbeat – sends a JSON heartbeat_response with timestamp
- browse_files – enumerates directory contents
- start_collection – searches and exfiltrates files under 100 MB matching specific extensions
- upload_execute – deploys and runs additional Python, shell, or desktop payloads
According to French cybersecurity firm Sekoia, DeskRAT’s C2 servers are “stealth servers,” meaning they do not appear in public NS records. Earlier campaigns used cloud platforms like Google Drive, but recent operations rely on dedicated staging servers.
Cross-Platform Context
QiAnXin XLab also identified StealthServer variants for Windows, which share functionality with DeskRAT:
- Windows-V1: Uses anti-debug techniques, persists via scheduled tasks, PowerShell scripts, and registry changes, communicates over TCP
- Windows-V2: Adds further anti-debug checks for OllyDbg, x64dbg, IDA
- Windows-V3: Uses WebSocket communication, functionally similar to DeskRAT
Additionally, two Linux StealthServer variants exist: DeskRAT (with an extra “welcome” command) and an HTTP-based version supporting browse, upload, execute commands. These Linux variants exfiltrate files recursively from the root directory using HTTP POST requests to modgovindia[.]space:4000.
Other Regional Threat Activity
APT36’s operations are part of a broader surge in South and East Asian cyber campaigns:
- Bitter APT targeted government, power, and military sectors in China and Pakistan, delivering a C# implant “cayote.log” via Excel or RAR attachments exploiting CVE-2025-8088.
- SideWinder launched attacks on maritime and other sectors in Pakistan, Sri Lanka, Bangladesh, Nepal, and Myanmar, using credential-harvesting portals and multi-platform malware (Operation SouthNet).
- OceanLotus (APT-Q-31) targeted enterprises and government entities in China and Southeast Asia with the Havoc post-exploitation framework.
- Mysterious Elephant (APT-K-47) attacked government and foreign affairs sectors in Pakistan, Afghanistan, Bangladesh, Nepal, India, and Sri Lanka using BabShell, MemLoader HidenDesk, and MemLoader Edge to deploy malware in memory.
These campaigns often exfiltrate sensitive communications from WhatsApp using modules like Uplo Exfiltrator, Stom Exfiltrator, and also use ChromeStealer Exfiltrator to harvest browser cookies, tokens, and files.