Security researchers have uncovered a widespread campaign where attackers exploited publicly available ASP.NET machine keys to break into Windows IIS web servers, then installed a malicious IIS module to hijack traffic and profit from fake search rankings. The group, tracked as REF3927, leveraged keys published in places like Microsoft documentation and online forums, making many servers vulnerable without targeted reconnaissance. Keywords, IIS security, ASP.NET machine key, webshell, TOLLBOOTH, SEO poisoning.
How the attack works
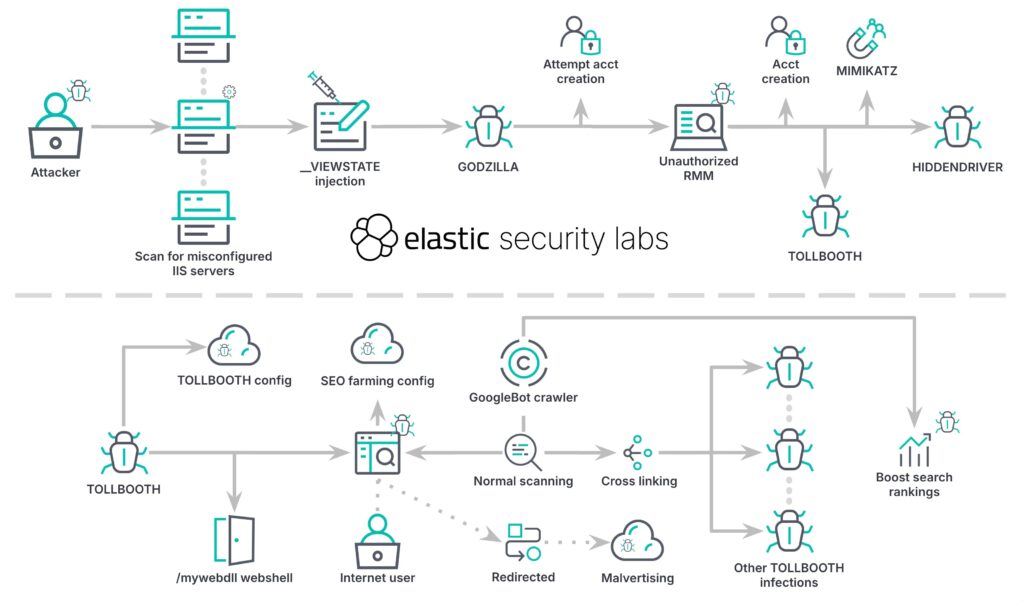
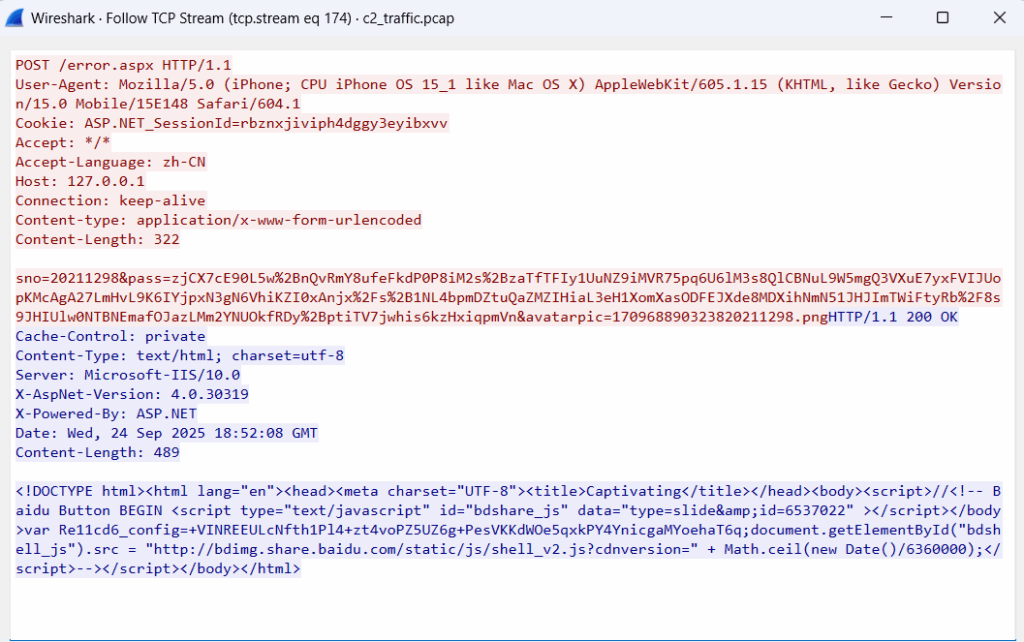
Attackers scanned for IIS sites that reused or copied ASP.NET machine keys from public sources, rather than creating unique keys per application. These machine keys are intended to protect sensitive web app data, such as cookies and ViewState, which is the hidden mechanism ASP.NET pages use to preserve state across requests. When a key is leaked, an attacker can forge a ViewState payload containing malicious code, submit it in a normal web request, and execute commands on the server, bypassing protections that rely on those keys.
Tooling and persistence, webshells, rootkits
Once they gained code execution, the attackers dropped a webshell derived from the open source Godzilla project, referred to in reports as Z-Godzilla_ekp. This webshell enables remote command execution, credential theft, network scanning, and covert communications that resemble normal web traffic. The intruders also attempted to create administrative accounts and used credential harvesting tools such as Mimikatz, although detections by defenders sometimes interrupted these steps.
To remain hidden, the campaign used a modified rootkit based on an open source project named Hidden, this rootkit conceals files, processes, and registry entries so cleanup is more difficult.
The TOLLBOOTH module, SEO manipulation for profit
The primary monetization mechanism is a malicious IIS module called TOLLBOOTH. This module cloaks harmful pages from search engine crawlers while serving keyword-stuffed, scammy landing pages to bots like Googlebot, in order to boost search rankings. TOLLBOOTH builds networks of infected sites that link to each other, artificially inflating SEO signals and driving traffic to scam pages, affiliate links, or ad farms. The module also contains a built-in webshell and diagnostic utilities for operators, and it retrieves configuration from a command and control domain, listed in some reports as c[.]cseo99.com, storing secrets temporarily on the victim host.
Scope, victims, and attribution
Elastic Security Labs, working with scanning firm Validin, identified over 570 infected servers across multiple countries, with industries ranging from finance to technology. Notably, reports indicate no infections in China, a pattern researchers interpret as deliberate avoidance by the attackers. Microsoft first described similar techniques in February 2025, and AhnLab published follow-up findings in April, suggesting this is a continuing campaign, likely run by Chinese-speaking operators that cast a wide, opportunistic net rather than targeting specific high-value organizations.
Why reinfection happened, recommended mitigation steps
Many victims were reinfected after initial remediation because administrators removed malware but failed to regenerate compromised ASP.NET machine keys. To recover securely, administrators should, at minimum, do the following, generate new, unique machine keys within IIS, remove any malicious modules and webshells, scan for and remove rootkit components, rotate credentials that may have been stolen, and monitor for unusual web traffic patterns or newly installed modules. Consider engaging managed detection services or incident responders if the infection shows signs of deep persistence.