Security researchers have uncovered a new Astaroth banking trojan campaign that uses GitHub as a fallback infrastructure, allowing the malware to remain operational even after traditional command and control servers are taken down. By hosting encrypted configuration data on GitHub, the attackers make the campaign more resilient, and victims continue to be compromised across multiple Latin American countries, especially Brazil.
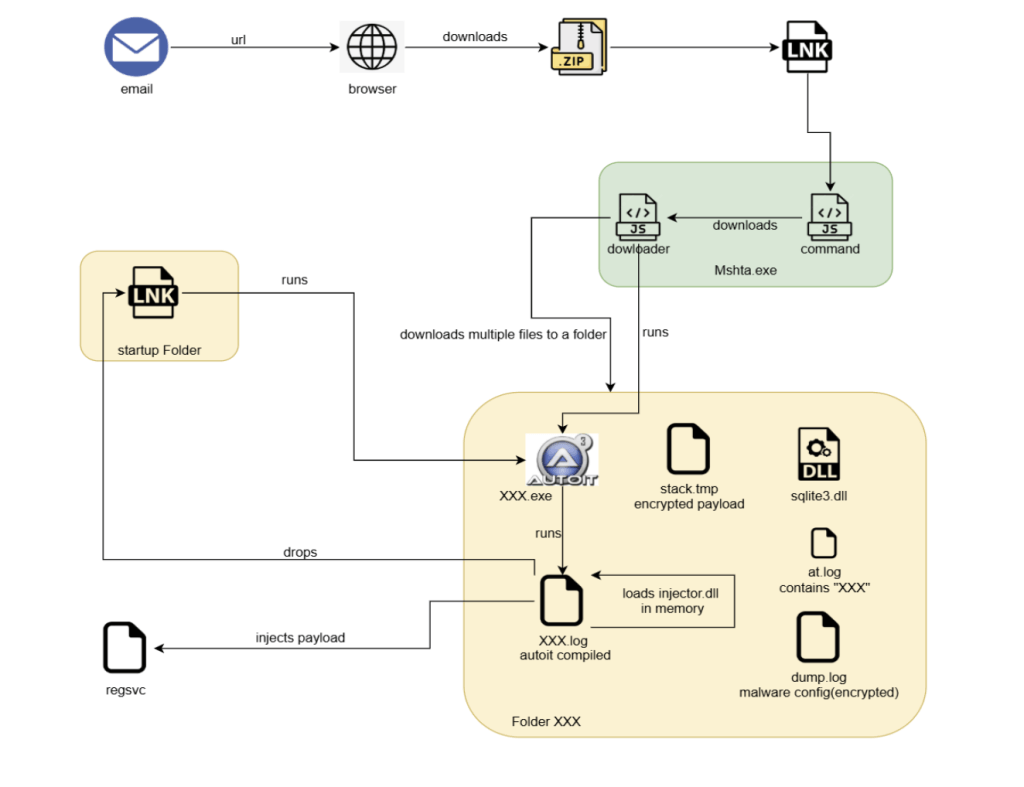
How the campaign works, step by step
- Phishing delivery, the chain begins with a DocuSign-themed email that lures victims to download a ZIP archive containing a Windows shortcut file (.lnk).
- LNK execution, the shortcut runs obfuscated JavaScript, which fetches additional JavaScript from an external server.
- Secondary payloads, the newly retrieved JavaScript downloads several files from one of several hard-coded servers, including an AutoIt script.
- Execution flow, the AutoIt script is run by the JavaScript, it then loads and executes shellcode, which in turn loads a Delphi-based DLL. That DLL decrypts and injects the Astaroth payload into a newly created RegSvc.exe process.
- Credential theft, Astaroth monitors active browser windows once every second, and if it detects a banking or cryptocurrency site, it hooks keyboard events to log keystrokes and capture credentials. The stolen data is exfiltrated using an Ngrok reverse proxy.
- Persistence and evasion, the malware drops an LNK file into the Windows Startup folder so it runs after reboot, and it self-terminates if it detects analysis tools or environments, including QEMU Guest Agent, HookExplorer, IDA Pro, ImmunityDebugger, PE Tools, WinDbg, and Wireshark. The campaign also geofences the initial URL, and it avoids systems with English or U.S. locale settings.
Targets and impact, countries and sites affected
McAfee Labs notes the campaign focuses heavily on Brazil, but Astaroth has historically targeted other Latin American countries, including Mexico, Uruguay, Argentina, Paraguay, Chile, Bolivia, Peru, Ecuador, Colombia, Venezuela, and Panama. Some of the websites targeted for credential harvesting are listed below, these are shown in obfuscated form to avoid accidental clicks, replace the brackets to visit them:
- caixa.gov[.]br
- safra.com[.]br
- itau.com[.]br
- bancooriginal.com[.]br
- santandernet.com[.]br
- btgpactual[.]com
- etherscan[.]io
- binance[.]com
- bitcointrade.com[.]br
- metamask[.]io
- foxbit.com[.]br
- localbitcoins[.]com
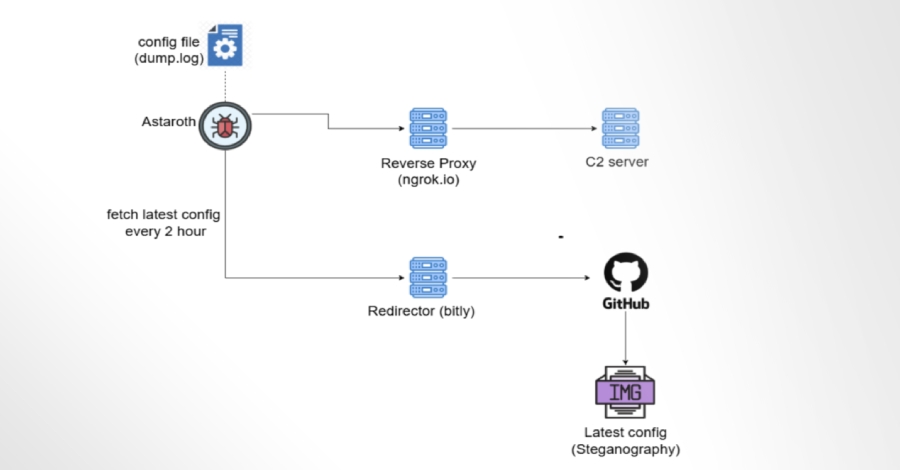
GitHub as resilient configuration storage, technique overview
Rather than rely only on conventional C2 servers that can be seized or disabled, the attackers host configuration data on GitHub, often embedding that data inside images using steganography. This allows Astaroth to fetch fresh configuration files from legitimate GitHub repositories when primary servers are unavailable. McAfee worked with GitHub to remove the repositories involved, temporarily disrupting the operation, but the design demonstrates how threat actors can weaponize public hosting platforms as backup infrastructure.
Why this matters, defender takeaways and mitigation suggestions
- Use layered defenses, combine email filtering, endpoint detection, and behavior monitoring to catch the different stages of the attack chain.
- Harden email gateways, increase phishing awareness training, and block or sandbox suspicious attachments such as .lnk files delivered in ZIP archives.
- Monitor for unusual process injection and persistence mechanisms, such as AutoIt scripts launching unfamiliar executables from the Startup folder.
- Restrict use of developer and public hosting platforms where possible, and monitor for suspicious repositories or image files containing hidden payloads.
- Apply locale and regional telemetry when investigating infections, since the malware avoids English and U.S. locales.
- Collaborate with platform providers, report malicious repositories to hosting services like GitHub, and follow coordinated takedown procedures.