New Advanced VoidLink Malware Targets Linux Cloud and Container Environments
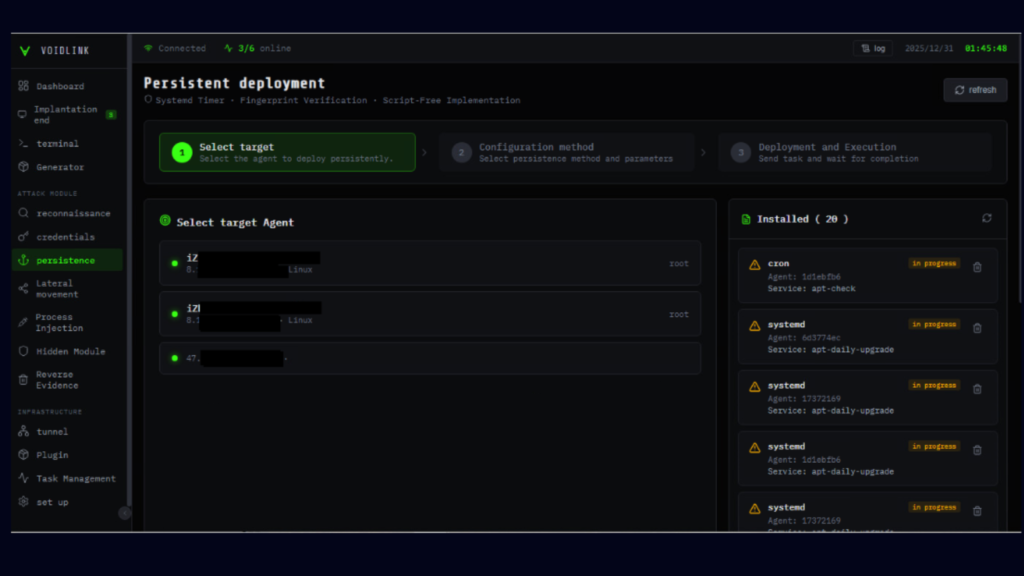
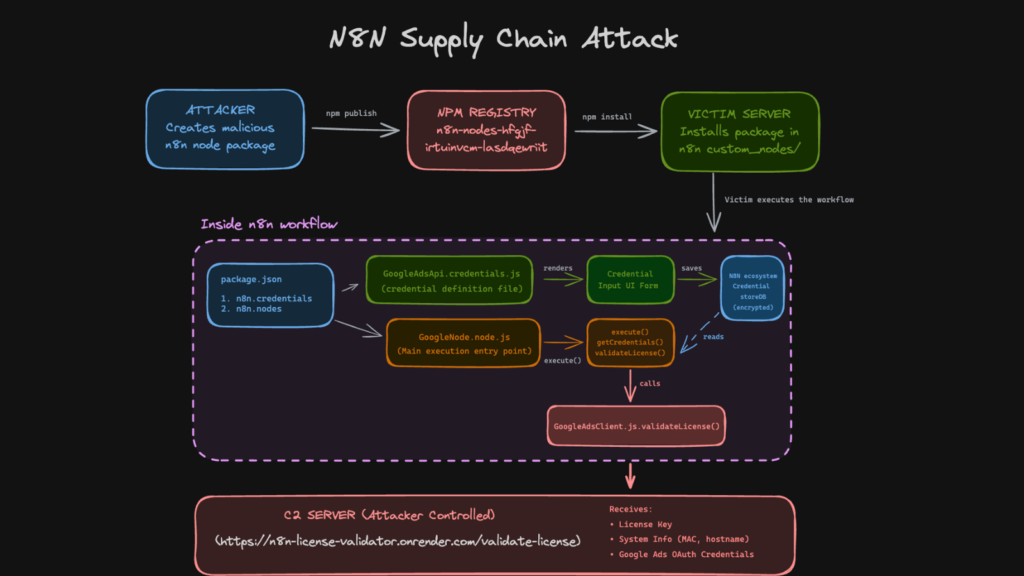
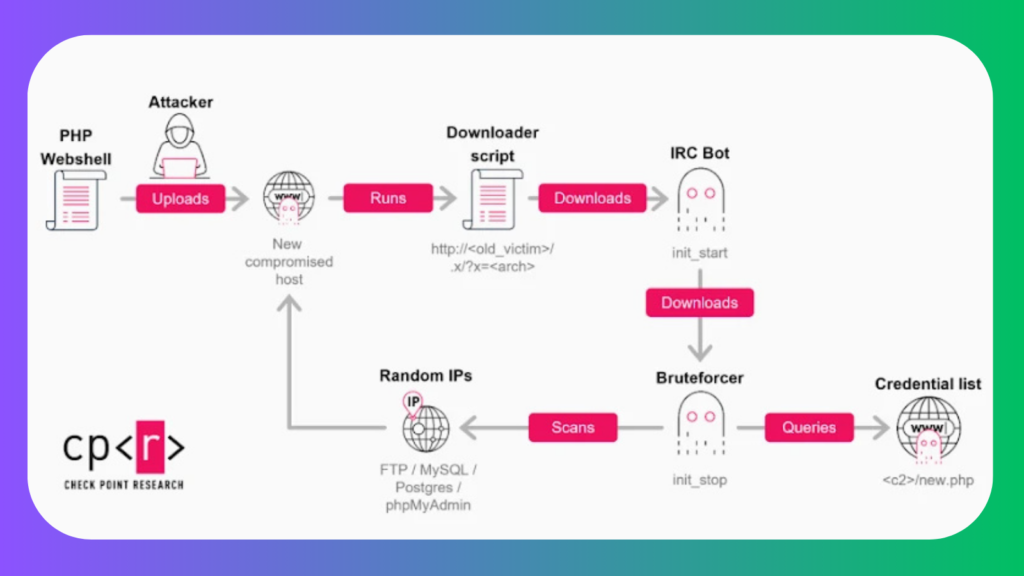
Cybersecurity researchers have revealed a previously unknown and highly sophisticated Linux malware framework known as VoidLink, which is purpose built to maintain long term, covert access to cloud based infrastructures. The malware specifically targets Linux systems that form the backbone of modern cloud services and containerized environments. According to a recent analysis published by Check Point […]
New Advanced VoidLink Malware Targets Linux Cloud and Container Environments Read More »