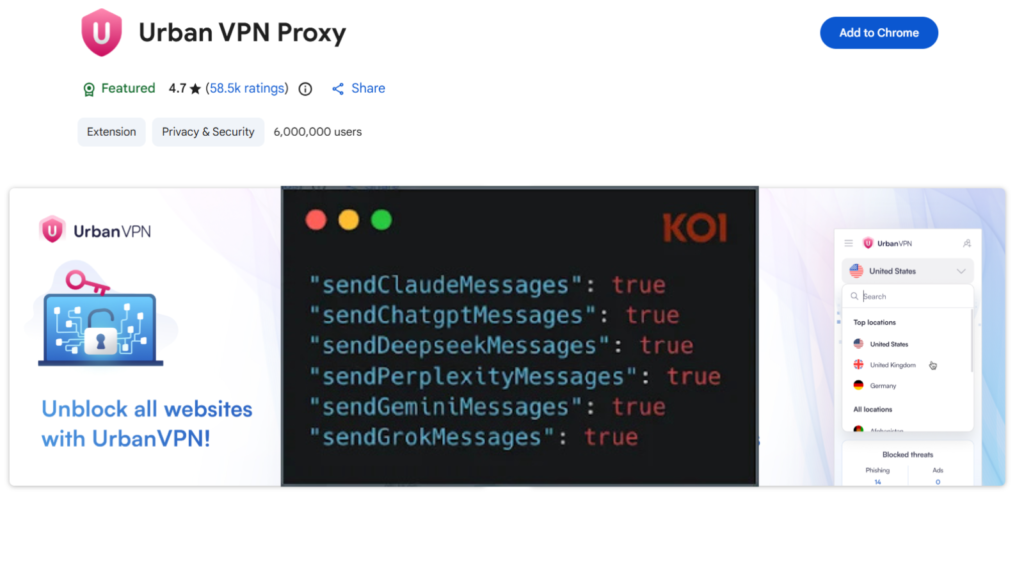
GhostPoster Malware Discovered in 17 Firefox Add ons with Over 50,000 Downloads
A newly identified malware campaign named GhostPoster has been uncovered abusing logo image files embedded within browser extensions to deliver malicious JavaScript code. The operation targeted users of Mozilla Firefox through at least 17 compromised add-ons that collectively recorded more than 50,000 downloads before being removed. The findings were disclosed by Koi Security, which identified […]
GhostPoster Malware Discovered in 17 Firefox Add ons with Over 50,000 Downloads Read More »