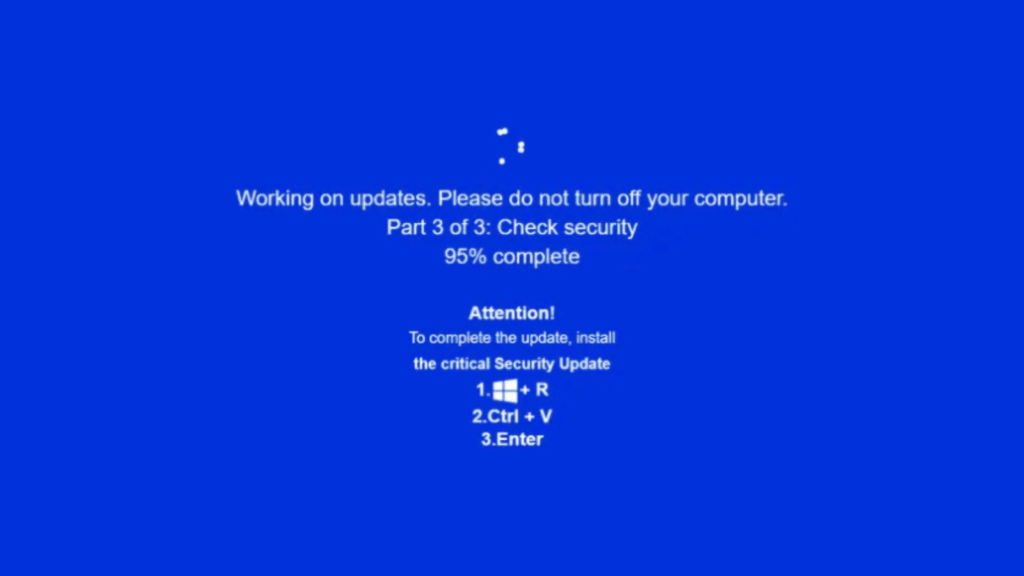
JackFix spreads multiple stealers via fake Windows Update pop ups on adult sites.
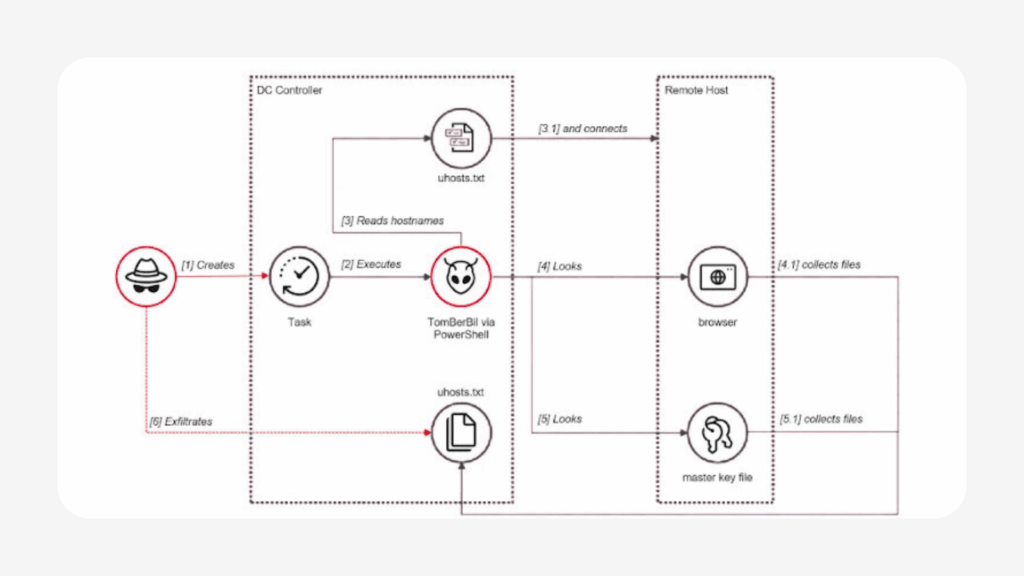
A newly uncovered malware campaign is exploiting adult themed phishing sites and deceptive ClickFix style lures to trick users into executing malicious Windows commands disguised as urgent security updates. Cybersecurity researchers from Acronis have identified the activity, warning that the threat actors are using highly convincing fake Windows update screens to distribute multiple information stealers. […]
JackFix spreads multiple stealers via fake Windows Update pop ups on adult sites. Read More »