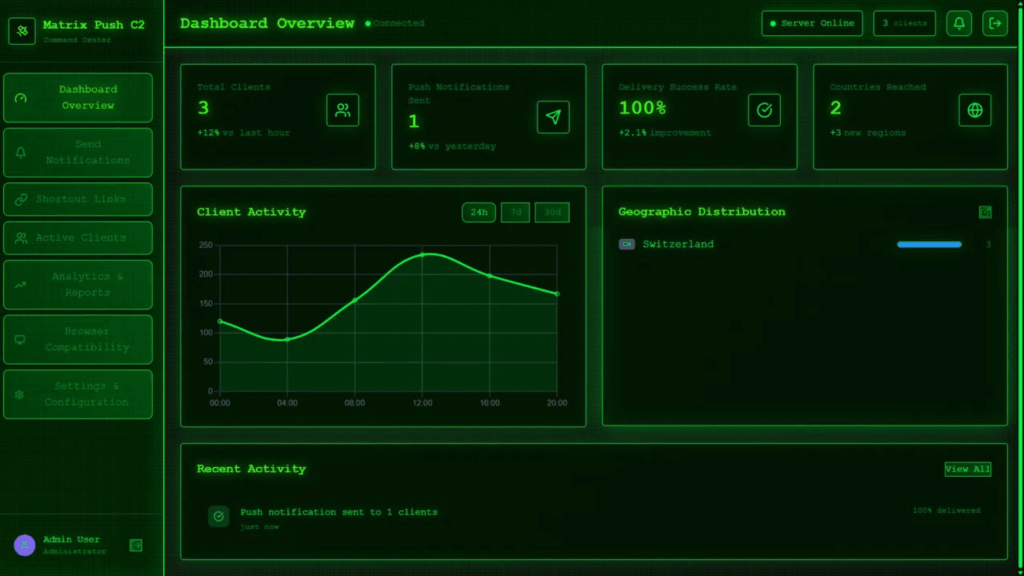
Matrix Push C2 Uses Browser Notifications for Fileless and Cross Platform Phishing Attacks
Cybersecurity analysts have identified a new trend in phishing operations, where browser notifications are being misused to push malicious links through a command and control platform known as Matrix Push C2. According to a recent report from BlackFog researcher Brenda Robb, the framework operates entirely within the browser environment, using push alerts, fake system style […]