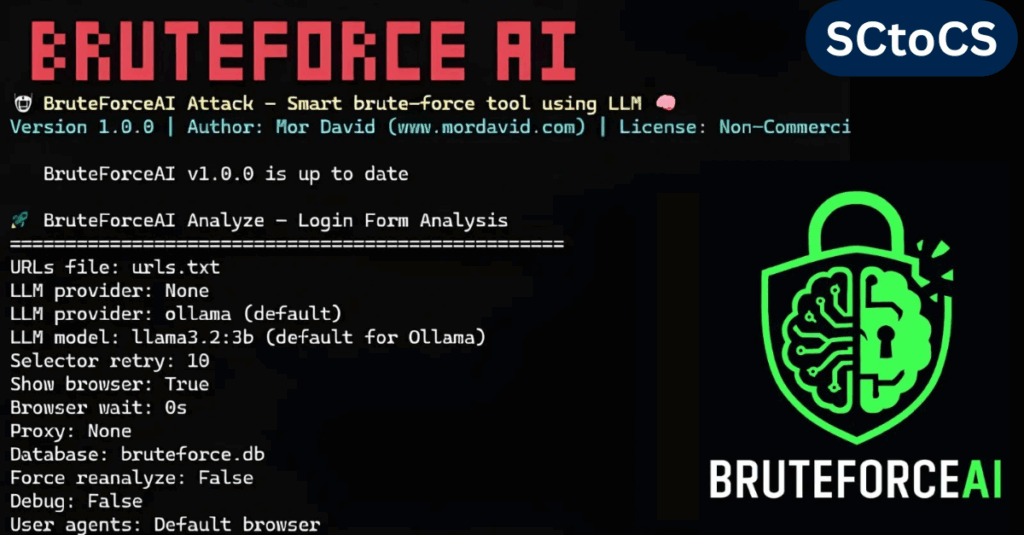
BruteForceAI Tool Automates Login Page Detection and Smart Brute-Force Attacks
BruteForceAI, created by security researcher Mor David, is a modern penetration testing tool that combines large language models (LLMs) with browser automation to automatically detect login forms and perform advanced brute-force testing. By merging AI-powered form analysis, evasion strategies, and detailed logging, this framework makes credential-testing faster and more efficient, helping security professionals quickly uncover […]
BruteForceAI Tool Automates Login Page Detection and Smart Brute-Force Attacks Read More »