BlackSuit Ransomware Servers Targeting U.S. Critical Infrastructure Dismantled in Major Law Enforcement Operation
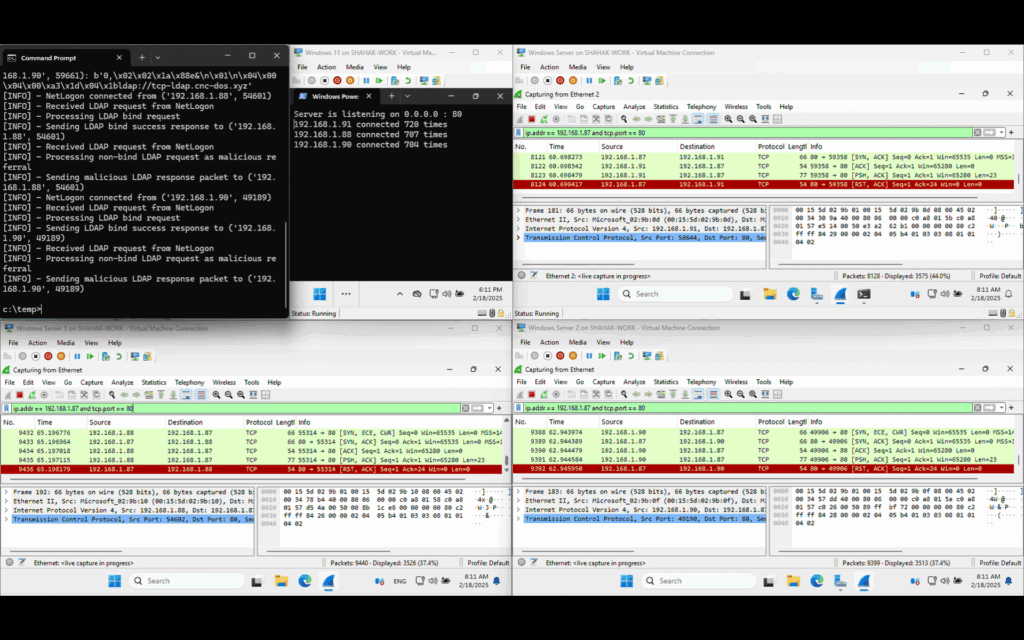
In a landmark coordinated effort, international law enforcement agencies have taken down critical infrastructure linked to the BlackSuit ransomware group (also known as Royal), marking a significant blow against one of the most persistent cybercriminal operations targeting the United States. The operation, conducted on July 24, 2025, led to the seizure of four servers, nine […]