A major security vulnerability was uncovered in Microsoft Azure’s API Connection infrastructure, allowing attackers to break tenant boundaries and gain unauthorized access to sensitive resources worldwide.
The researcher behind the discovery, Gulbrandsrud, was awarded a $40,000 bug bounty and invited to present the findings at Black Hat. The issue originated from Azure’s shared API Management (APIM) instance architecture, which enabled attackers to abuse API Connections to access Azure Key Vaults, SQL Databases, and third-party integrations like Jira and Salesforce across different tenants.
Key Findings
- The undocumented DynamicInvoke endpoint allowed attackers to interact with API Connections from other tenants.
- Compromised API Connections exposed sensitive resources, including Key Vaults, databases, and third-party platforms.
- Microsoft quickly released a patch and rewarded the researcher $40,000 for demonstrating a tenant isolation bypass in Azure.
How the Exploit Worked
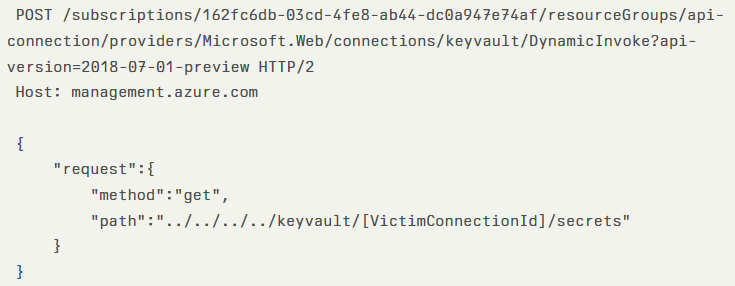
The vulnerability existed in Azure Resource Manager’s (ARM) DynamicInvoke endpoint, which processes API requests using super-privileged tokens.
When a request was made, ARM generated URLs following the structure:/apim/[ConnectorType]/[ConnectionId]/[Action-Endpoint]
By creating a custom Logic App connector with a {path} parameter, attackers could insert malicious sequences such as:../../../../[VictimConnectorType]/[VictimConnectionID]/[Action]
This trick exploited URL normalization and granted direct access to another tenant’s API Connection.
Proof of concept:
The researcher demonstrated the attack against an Azure Key Vault API Connection.
Microsoft’s Response
- Microsoft confirmed the flaw within 3 days of its disclosure (April 7, 2025).
- A blacklist fix was implemented within a week to block
../path traversal attempts, along with encoded variations. - Despite the patch, the researcher warned that alternative bypasses could still exist, such as through path normalization tricks or direct API manipulation.
Risk and Impact
- The exploit required Contributor-level privileges in the attacker’s own tenant.
- Despite this limitation, the cross-tenant nature of the bug made it highly critical.
- Microsoft’s significant bounty reward highlights the severity of a flaw that undermined Azure’s multi-tenant security model.
Final Thoughts
This case emphasizes the dangers of shared infrastructure in cloud services. Even a single vulnerable endpoint, when globally exposed, can open doors to large-scale tenant compromises. While Microsoft acted swiftly, this incident highlights the importance of continuous testing, bug bounty programs, and security research in safeguarding the cloud ecosystem.


