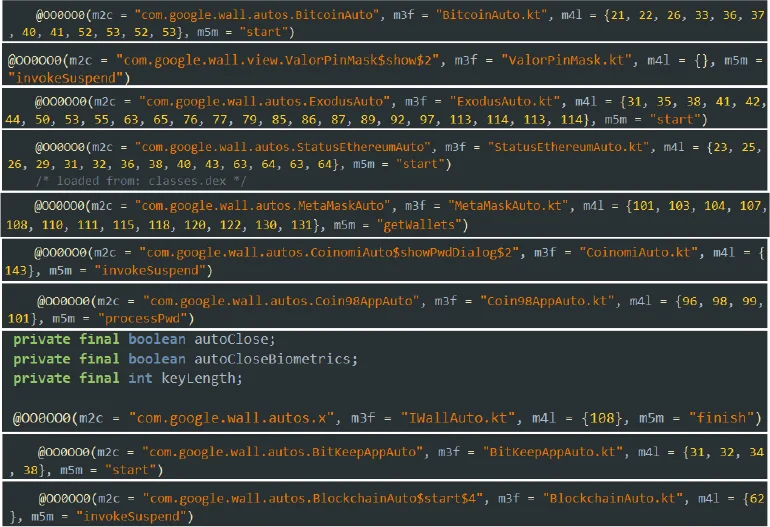
Cybersecurity researchers have exposed two sophisticated Android trojans, BankBot-YNRK and DeliveryRAT, which are actively stealing sensitive financial information from users worldwide. These malware families employ advanced evasion techniques and abuse core phone functionalities to commit fraud and data theft on a significant scale.
BankBot-YNRK: A Highly Evasive Banking Trojan
Analyzed by CYFIRMA, BankBot-YNRK is a dangerous malware strain that incorporates multiple checks to avoid analysis and target specific devices. Before activating, it performs several anti-detection routines:
- It checks if it is running in a virtualized or emulated environment (like a security researcher’s sandbox).
- It extracts device details like manufacturer and model to confirm it’s on a real user’s phone.
- It specifically identifies if the device is an Oppo, Google Pixel, or Samsung model from a predefined list, allowing it to apply device-specific optimizations and avoid execution on untargeted or unrecognized devices.
The malware is distributed through APK packages with names designed to impersonate a legitimate Indonesian government application, “Identitas Kependudukan Digital” (Digital Population Identity). The identified malicious package names are:
com.westpacb4a.payqingynrk1b4acom.westpacf78.payqingynrk1f78com.westpac91a.payqingynrk191a
BankBot-YNRK’s Malicious Capabilities
Once installed, the trojan initiates a comprehensive attack:
- Stealth Mode: It sets the volume for ringtones, music, and notifications to zero, silencing the device to prevent the user from being alerted.
- Accessibility Abuse: It communicates with a remote server (
ping.ynrkone[.]top) and, upon command, aggressively urges the user to enable Accessibility services. This grants it elevated privileges to perform automated, malicious actions. - Persistence: It uses Android’s JobScheduler service to ensure it restarts automatically after a device reboot.
- Data Theft: It can harvest contacts, SMS messages, location data, installed app lists, and clipboard content.
- Advanced UI Manipulation: It can capture screens to reconstruct the interface of banking apps, impersonate Google News, and use overlays to display fake verification messages while performing malicious acts in the background.
A critical limitation for the malware is that it only effectively targets devices running Android 13 and below. Android 14 introduced a crucial security feature that prevents apps from using Accessibility services to auto-grant themselves permissions, forcing users to approve permissions directly via the system.
The DeliveryRAT Threat: Malware-as-a-Service for Russian Users
In a parallel development, the updated DeliveryRAT trojan is being distributed primarily to Russian Android users. This malware is offered under a Malware-as-a-Service (MaaS) model via a Telegram bot named “Bonvi Team.”
The malware disguises itself as apps for:
- Food delivery services
- Online marketplaces
- Banking services
- Parcel tracking
Victims are contacted on messaging apps like Telegram and tricked into downloading the app under the pretense of tracking an order or for a fake remote job opportunity. Once installed, the app:
- Requests access to notifications and disables battery optimizations to run persistently in the background.
- Steals SMS messages and call logs.
- Hides its icon from the home screen, making it difficult for average users to find and uninstall.
- Some variants can even perform DDoS attacks by flooding a target URL with requests or by tricking users into scanning a malicious QR code.
The Broader Threat: NFC Payment Data Theft
Adding to the mobile threat landscape, a report from Zimperium discovered over 760 fake Android apps since April 2024 that abuse Near-Field Communication (NFC) to steal payment data. These apps:
- Pose as financial applications.
- Prompt users to set them as the default payment method.
- Use Android’s Host-based Card Emulation (HCE) to intercept contactless credit card and payment information.
- Send the stolen data to Telegram channels or dedicated “tapper” apps, allowing criminals to instantly withdraw funds or make unauthorized purchases at point-of-sale terminals. The primary targets are Russian banks, but institutions in Brazil, Poland, the Czech Republic, and Slovakia are also impersonated.