Researchers at Aryaka Threat Research Labs, Aditya K Sood and Varadharajan K, report that attackers impersonate recruiters, sending seemingly legitimate job descriptions and corporate documents that conceal malicious payloads. These lures are designed to look authentic, encouraging recipients to open files that initiate a multi-stage infection.
How the attack works
The campaign commonly uses ZIP archives that contain decoy PDF documents alongside files that masquerade as PDFs, for example shortcuts (LNK) or executables. When a victim opens the LNK file, it runs an embedded PowerShell script which contacts an external server to download a lure document, a PDF for a marketing role at Marriott. The same PowerShell script also fetches a ZIP archive containing XtraViewer related files, likely to establish persistent remote access on the compromised system.
Social engineering, browser trickery, and persistence
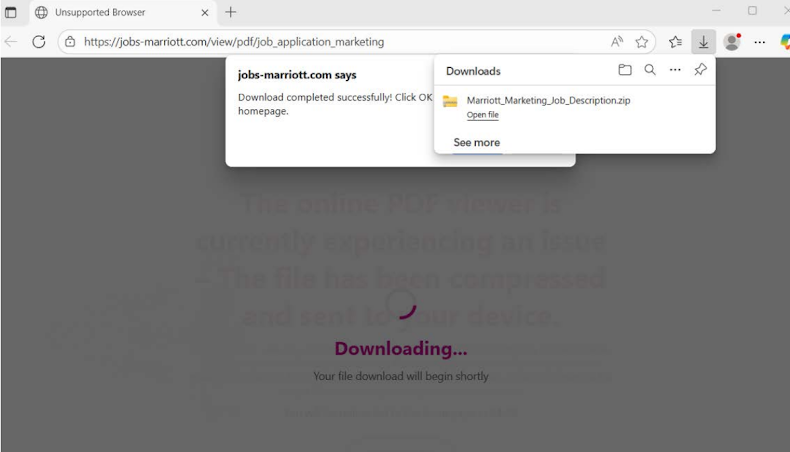
Victims who click a link inside the lure PDF are sent to a landing page that displays a fake error message claiming the browser is unsupported, instructing users that downloads only work in Microsoft Edge. Chrome often blocks the redirect, so the page prompts users to copy the URL and open it in Edge, turning the download into a user-initiated action. If the victim follows the instruction and opens the URL in Edge, the page shows another message about the online viewer failing, and states the file has been compressed and sent to the device, which triggers an automatic ZIP download.
The ZIP archive contains a malicious executable named “Marriott_Marketing_Job_Description.pdf.exe”, which uses spacing tricks to resemble a PDF file. Once executed, the Go-based Vampire Bot activates.
Vampire Bot capabilities
Vampire Bot, written in Golang, is capable of profiling the infected machine, exfiltrating various categories of data, taking screenshots at configurable intervals, and maintaining communication with an attacker-controlled command and control domain, “api3.samsungcareers[.]work”. Through that channel, the operators can issue commands or deliver additional payloads.
Attribution and historical context
Researchers link BatShadow to Vietnam based on use of an IP address, 103.124.95[.]161, previously associated with Vietnam-linked malicious operations. The targeting profile, focusing on digital marketing professionals, aligns with prior campaigns by financially motivated Vietnamese groups that have deployed stealers to hijack Facebook business accounts. In October 2024, Cyble detailed a similar multi-stage phishing campaign targeting job seekers and marketing professionals, which delivered Quasar RAT via booby-trapped job description files.
BatShadow has been active for at least a year, using domains such as samsung-work.com in past campaigns to distribute malware families like Agent Tesla, Lumma Stealer, and Venom RAT. Aryaka warns that the group continues to refine its social engineering techniques, delivering a sophisticated Go-based surveillance and exfiltration tool via disguised documents and staged downloads.