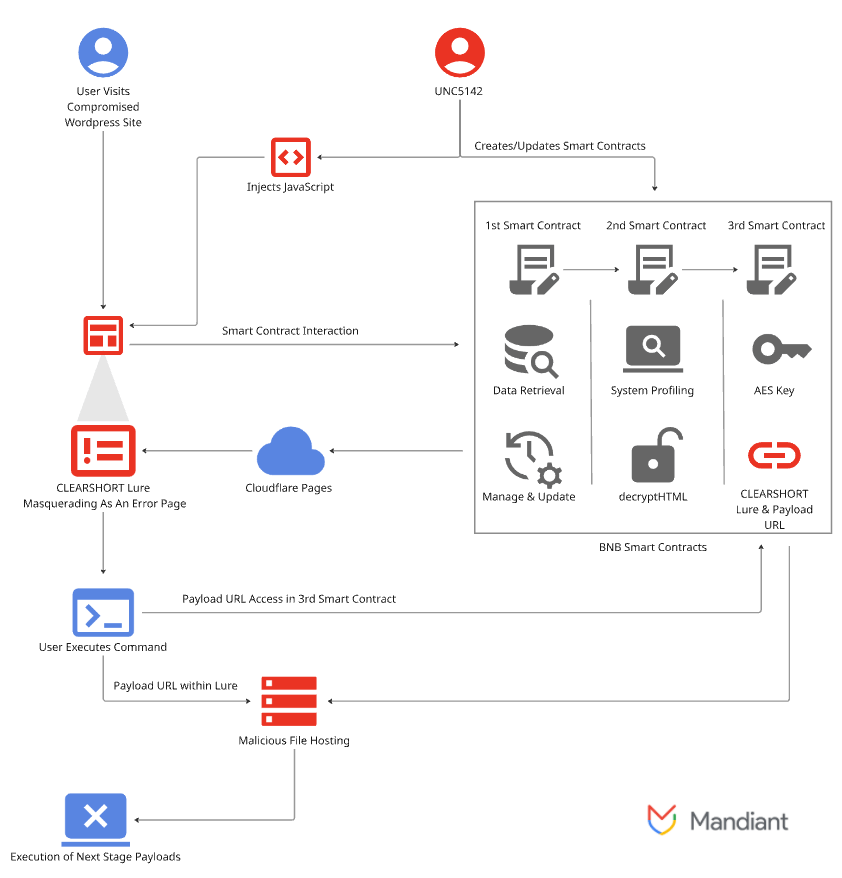
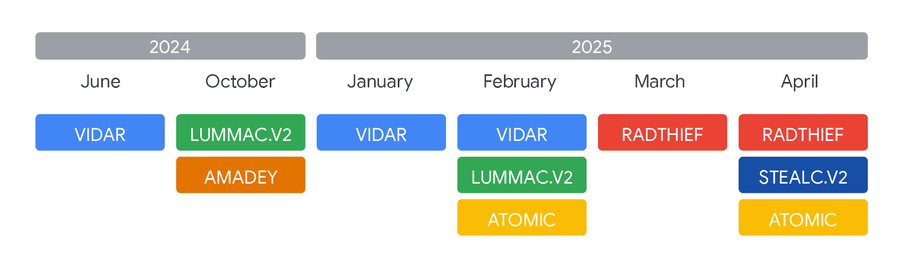
Cybersecurity researchers have observed a financially motivated threat actor, tracked as UNC5142, leveraging blockchain smart contracts to distribute information-stealing malware targeting both Windows and macOS systems. This operation demonstrates how attackers combine traditional web compromises with modern Web3 technology to evade detection and increase operational resilience.
Malware Distribution via WordPress and Blockchain
According to the Google Threat Intelligence Group (GTIG), UNC5142 primarily abuses compromised WordPress websites and uses a method called EtherHiding, where malicious code or data is stored on a public blockchain like the BNB Smart Chain (BSC) to hide its presence.
As of June 2025, GTIG flagged approximately 14,000 web pages containing JavaScript injected by UNC5142, showing a widespread targeting of vulnerable WordPress sites. However, no activity was observed after July 23, 2025, suggesting a pause or a strategic shift.
EtherHiding was first documented by Guardio Labs in October 2023, when attacks used Binance Smart Chain contracts to serve malicious code through fake browser update alerts.
CLEARSHORT: Multi-Stage JavaScript Downloader
A core component of these campaigns is CLEARSHORT, a multi-stage JavaScript downloader.
- Stage One: Malicious JavaScript is inserted into plugin files, theme files, or the WordPress database. It interacts with a malicious smart contract on BSC to fetch the second stage.
- Stage Two: The smart contract retrieves a CLEARSHORT landing page hosted externally, employing the ClickFix social engineering tactic to trick users into executing commands on Windows Run or macOS Terminal.
For Windows, the command executes an HTA file downloaded from MediaFire. This drops a PowerShell script that fetches the encrypted malware payload from GitHub, MediaFire, or private infrastructure, running it directly in memory without touching the disk.
For macOS, attackers used ClickFix decoys to prompt users to run a bash command in Terminal, which downloads a shell script that retrieves the Atomic Stealer payload via curl from remote servers.
CLEARSHORT and ClearFake Connection
CLEARSHORT is a variant of ClearFake, a rogue JavaScript framework first analyzed by French cybersecurity firm Sekoia in March 2025. ClearFake has been active since July 2023, delivering malware via drive-by downloads, with ClickFix added around May 2024.
Blockchain Advantages for Attackers
Leveraging blockchain technology provides multiple benefits for UNC5142:
- Blends malicious activity with legitimate Web3 operations.
- Increases resilience against detection and takedown efforts.
- Enables rapid updates to landing pages or decryption keys using smart contract data modifications, costing only $0.25–$1.50 per update.
Smart Contract Infrastructure
The threat actor transitioned from a single-contract system to a three-smart contract architecture by November 2024, enhancing operational agility. This Router-Logic-Storage setup allows precise control over updates without modifying the WordPress-injected JavaScript.
UNC5142 operates two parallel infrastructures:
- Main Infrastructure: Created November 24, 2024, serves as the primary campaign backbone with continuous updates.
- Secondary Infrastructure: Funded February 18, 2025, supports tactical campaigns, testing new lures, or increasing operational resilience.
The high volume of compromised sites, frequent updates, and diverse malware payloads indicate that UNC5142 has achieved measurable operational success over the past 18 months.