Security researchers have exposed two coordinated malware campaigns, GhostCall and GhostHire, linked to the North Korea-associated Lazarus sub-group BlueNoroff, also tracked under names like APT38, CryptoCore, Genie Spider, Nickel Gladstone, Sapphire Sleet, and Stardust Chollima. The campaigns focus on the Web3 and blockchain ecosystem, and together they form part of a larger, long-running operation Kaspersky calls SnatchCrypto, active since at least 2017. Key SEO keywords: BlueNoroff, GhostCall, GhostHire, macOS malware, Web3 security, phishing.

Overview of the Campaigns
Kaspersky reports that GhostCall primarily targets macOS systems, notably the devices of executives at tech companies and venture capital firms, while GhostHire concentrates on recruiting lures aimed at Web3 developers, with heavy activity observed in Japan and Australia. The research traces continuous activity from mid-2023 for GhostCall, and Kaspersky has been tracking both campaigns since April 2025. Multiple vendors, including Microsoft, SentinelOne, Huntress, and others, have documented related activity over the past year.
GhostCall, the Fake Meeting Ruse
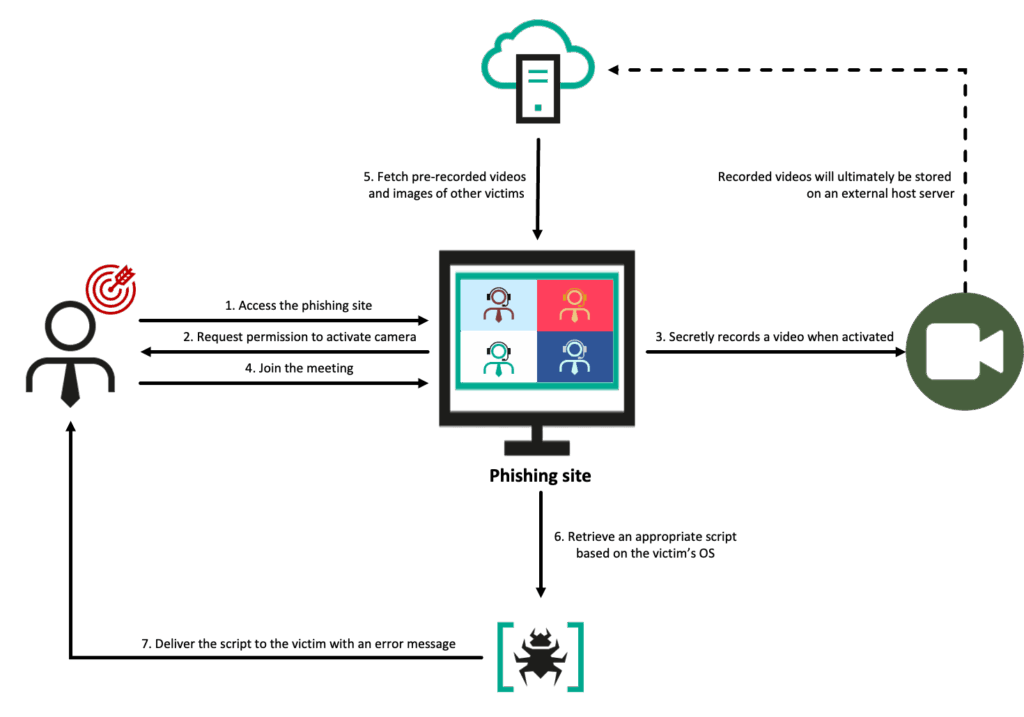
GhostCall uses realistic, invitation-based social engineering. Attackers contact targets on platforms like Telegram and invite them to investment or meeting calls hosted on spoofed, Zoom-like web pages. Victims who join encounter a staged “live” call, often using recordings of real victims rather than AI deepfakes, then see a short error message and are prompted to download a Zoom SDK or TeamsFx SDK update.
If the target clicks “Update Now”, macOS victims receive an AppleScript, while Windows victims are pushed a PowerShell command via a ClickFix technique. Each interaction with the fake meeting page is tracked, with attacker servers logging victim actions. Recently, the actor has shifted between Zoom and Microsoft Teams lures but kept the same update-to-infect workflow.
GhostHire, the Malicious Assessment
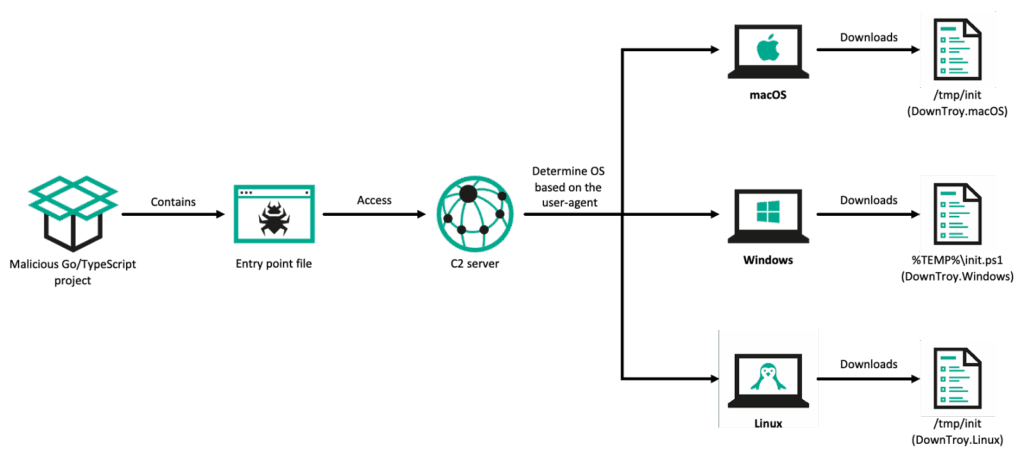
GhostHire pursues Web3 engineers through Telegram, posing as recruiters and directing candidates to complete timed coding assessments. The actor often uses a Telegram bot that impersonates corporate branding, then sends a ZIP containing a project, pressuring recipients to run it quickly, usually within 30 minutes, to increase the chance of execution.
The delivered project appears benign but includes a malicious dependency hosted on GitHub, for example a trojanized Go module. When executed, the dependency determines the victim’s operating system and deploys an OS-appropriate payload, commonly DownTroy, which continues the infection chain.
The DownTroy Ecosystem, payload families and loaders
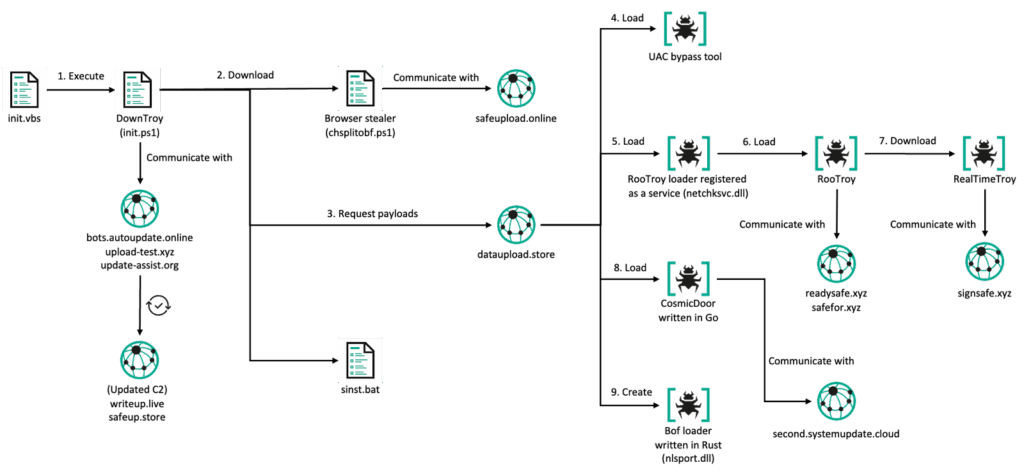
DownTroy serves as a central downloader and pivot, delivering multiple follow-on payloads and, crucially, bypassing macOS privacy controls like TCC (Transparency, Consent, and Control). Kaspersky outlines eight distinct attack chains tied to DownTroy, examples include:
- ZoomClutch / TeamsClutch, a Swift implant masquerading as a meeting app, that coerces users to enter their system password, then exfiltrates it to a remote server.
- DownTroy v1, a Go-based dropper that launches AppleScript-based components, repeatedly fetching scripts until the host is rebooted.
- CosmicDoor, a backdoor injected at runtime via a C++ loader called GillyInjector (aka InjectWithDyld), available in multiple language variants (Go, Rust, Python, Nim), and capable of destructive file-wiping when invoked with specific flags. CosmicDoor also drops SilentSiphon, a script stealer suite.
- RooTroy and RealTimeTroy, backdoors delivered via Nimcore loader and GillyInjector, that enumerate systems, manage files, and maintain two-way communication with command-and-control infrastructure.
- SysPhon, a C++ downloader in the RustBucket family, which performs reconnaissance and fetches binary payloads, and has been used in other campaigns.
These components demonstrate an actor developing cross-platform toolchains, with Windows and macOS-specific implants and loaders, plus variations compiled in multiple languages for flexibility and evasion.
SilentSiphon, targets and data theft
SilentSiphon is a comprehensive credential and secrets harvester, designed to collect data from Apple Notes, Telegram, browser extensions, credential stores, and many development and cloud services. The list of targeted systems and services is extensive, and includes code repositories and package managers (GitHub, GitLab, npm, pip, cargo), cloud providers (AWS, Google Cloud, Azure, Oracle Cloud), hosting and CI/CD services (Vercel, Netlify, CircleCI), payment processors and APIs (Stripe, Twilio), container and orchestration platforms (Docker, Kubernetes), and multiple blockchain ecosystems (Solana, Aptos, NEAR, Sui, Algorand). This broad scope allows the actor to harvest credentials and keys that grant access to infrastructure, developer accounts, and blockchain wallets.
Tactics, Techniques and Timeline
The campaigns build on a shift by the actor toward macOS targeting, a trend first notable in the RustBucket activity. After that pivot, the operator expanded tooling and introduced families such as KANDYKORN, ObjCShellz, and TodoSwift. The actor leverages social engineering, supply-chain style malicious dependencies, loader injection techniques, credential prompts, and AI-assisted tooling, including image enhancement via generative models, to craft convincing lures and profile targets.
Kaspersky notes the actor has iteratively improved the toolchain, reusing a unified command-and-control infrastructure to coordinate cross-platform implants. The use of generative AI reportedly accelerated development and lowered operational costs for the threat actor.
Attribution and Impact
The activity is attributed to BlueNoroff, a Lazarus sub-cluster long connected to financially motivated operations targeting cryptocurrency and Web3 infrastructure. The campaigns show a strategic expansion from simple credential theft to broad data acquisition, focusing on infrastructure, collaboration tools, code repositories, note applications, and messaging platforms, enabling reconnaissance, account takeover, and potential theft of crypto assets.


