Brazil is facing a growing wave of cyberattacks as the threat actor known as Water Saci rolls out a more advanced infection chain that spreads banking malware through WhatsApp Web and relies on layered delivery techniques using PDF and HTA files.
WhatsApp Worm Used to Deliver Banking Trojan
Threat analysts from Trend Micro reported that Water Saci has shifted away from PowerShell based propagation and adopted a Python variant capable of spreading malware to the victim’s WhatsApp Web contacts.
How the attack works
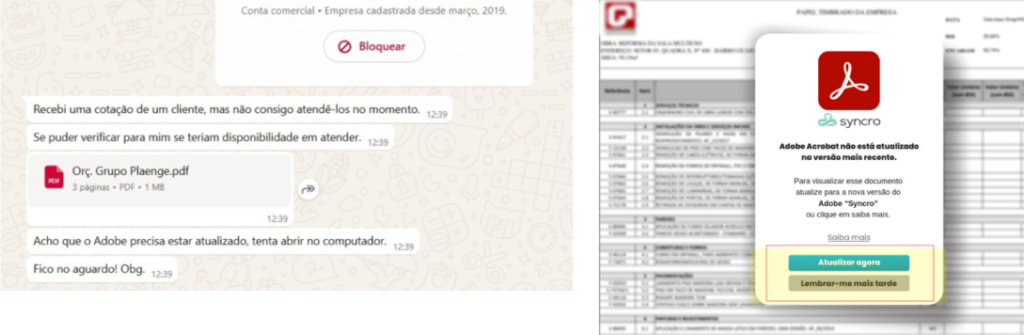
Users receive messages from trusted WhatsApp contacts containing malicious PDF or HTA attachments.
- The PDF instructs users to update Adobe Reader by clicking an embedded link.
- The HTA triggers a Visual Basic Script that runs PowerShell commands to download payloads, including
- an MSI installer for the banking trojan
- a Python script that enables WhatsApp Web worm like distribution
Trend Micro said the Python based version offers broader browser compatibility, object oriented code, improved error handling, and faster automation.
AutoIt Loader and System Targeting
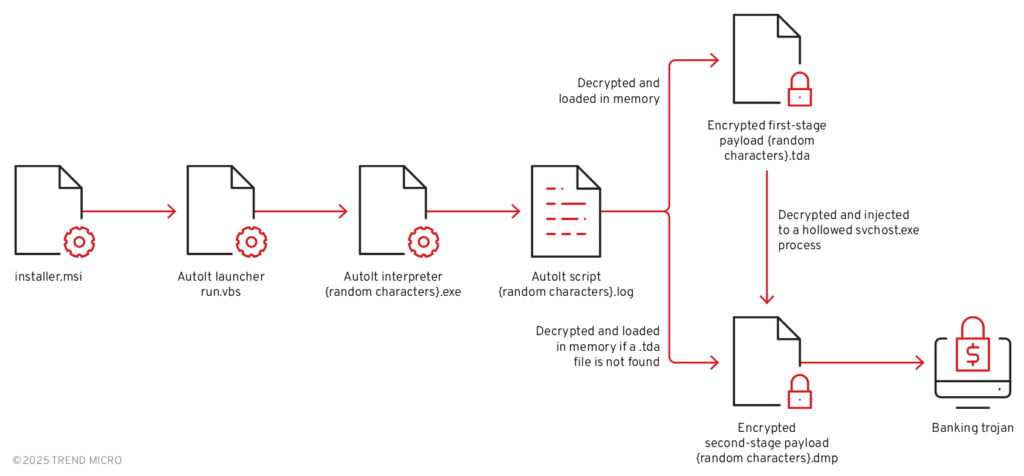
The MSI installer deploys the banking trojan using AutoIt scripts. These scripts
- ensure only a single instance runs
- check for a marker file named executed.dat
- report to an attacker server at manoelimoveiscaioba[.]com
Other AutoIt files check for Portuguese Brazil system language and scan for folders linked to Brazilian banks such as Bradesco, Itaú, Sicoob, and Santander. The malware also reviews Chrome history to detect banking website visits.
Multi Stage Injection Process
Once active, the script checks for TDA or DMP payload files
- If TDA exists, it is decrypted and injected into a hollowed svchost.exe process
- If only DMP exists, the trojan loads directly into AutoIt memory
Persistence relies on monitoring the injected svchost.exe process. If it stops, the malware relaunches and waits until the victim visits a banking site again.
Banking Trojan Capabilities
The deployed trojan resembles Casbaneiro, not Maverick. It includes
- window title monitoring for banking or crypto activity
- anti virtualization checks
- WMI based system profiling
- Registry modifications for persistence
- IMAP fallback C2 communications via serverseistemasatu[.]com
Its functionality includes
- system info collection
- keylogging
- screen capture
- forced browser termination
- mouse and click simulation
- file upload and download
- window enumeration
- fake banking overlays
Propagation Script Possibly Written With AI
Trend Micro found similarities between the PowerShell and Python propagation scripts, including console emojis, suggesting possible use of an LLM or automated conversion tool.
Brazil Also Targeted by RelayNFC Android Malware
A separate investigation by Cyble revealed a new Android malware called RelayNFC, active since early November 2025. It performs real time NFC relay attacks to steal contactless payment card data.
RelayNFC
- is developed using React Native and Hermes bytecode
- spreads via Portuguese language phishing pages such as maisseguraca[.]site
- asks users to tap their payment card on the phone
- relays APDU commands via WebSockets
- sends PINs and card data to attacker servers
attackers use this data to complete EMV transactions as if the card were physically present.
Experiments With Host Card Emulation
Cyble also discovered another Android APK hosted on test.ikotech[.]online, containing partial Host Card Emulation logic. The feature is not fully implemented but shows attackers are testing more advanced relay methods.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


