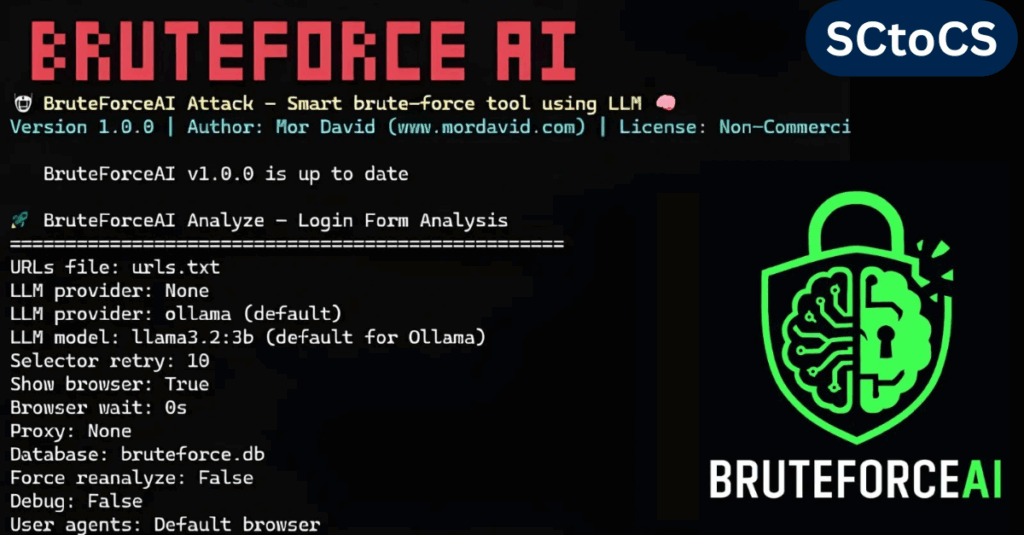
BruteForceAI, created by security researcher Mor David, is a modern penetration testing tool that combines large language models (LLMs) with browser automation to automatically detect login forms and perform advanced brute-force testing.
By merging AI-powered form analysis, evasion strategies, and detailed logging, this framework makes credential-testing faster and more efficient, helping security professionals quickly uncover weak authentication systems.
Two-Stage Working Process
At the heart of BruteForceAI is a two-step approach:
Stage 1: AI-Powered Login Form Detection
The system uses LLMs (via Ollama or Groq) to scan HTML code and detect login form elements with up to 95% accuracy in real-world scenarios.
It reviews page structures, input fields, and submission endpoints, then generates CSS selectors required for the next phase of testing.
Stage 2: Smart Attack Execution
In this stage, BruteForceAI conducts multi-threaded brute-force attempts with AI-discovered selectors. Users can select between two modes:
- Brute-Force Mode: Tests every possible username/password combination.
- Password-Spray Mode: Uses each password across multiple usernames, lowering the chance of account lockouts.
The tool employs feedback-based learning, DOM-change detection, and human-like timing patterns to improve success rates and bypass security defenses.
Key Features of BruteForceAI
| Feature Category | Capabilities |
|---|---|
| Multi-Threading | 1–100+ threads with smart delay handling |
| Evasion Techniques | Random User-Agent rotation, proxy support, jitter control, hidden browser mode |
| Notifications & Logs | Real-time alerts (Discord, Slack, Teams, Telegram), SQLite logs, detailed output |
| Operational Tools | Auto-updates, retry system, database cleanup, colored terminal interface |
The tool also offers webhook integration for instant credential success alerts and detailed SQLite logs for reviewing every attempt.
Database management features include schema inspection and cleanup, while results can also be exported to files for analysis.
Installation and Setup
BruteForceAI requires Python 3.8+, Playwright browsers, and common libraries like requests and PyYAML.
Installation Steps:
- Clone the GitHub repository
- Run:
pip install -r requirements.txt - Configure your preferred LLM option:
- Local (Ollama): Use models like
llama3.2:3bfor balance orllama3.2:1bfor speed. - Cloud (Groq): Authenticate with an API key and choose
llama-3.3-70b-versatile(recommended) or lightweight options likegemma2-9b-it.
Usage Commands:
- Analyze targets
python main.py analyze --urls targets.txt --llm-provider ollama --llm-model llama3.2:3bpython main.py attack --urls targets.txt --usernames users.txt --passwords passwords.txt --threads 20 --delay 5 --jitter 2Ethical Use
BruteForceAI is built only for authorized penetration testing, research, and education. Any misuse on unauthorized systems is both illegal and unethical. Organizations should always operate within an approved scope, and the developer takes no responsibility for unlawful use.
Conclusion
By combining AI, automation, and evasion strategies, BruteForceAI represents a new evolution in credential testing tools, giving red teams and security auditors the power to find authentication flaws with greater speed, stealth, and accuracy.