A highly sophisticated phishing campaign successfully targeted high-profile developers on the NPM registry in September 2025, leading to one of the most significant supply chain attacks in its history. The attackers combined convincing social engineering with technical precision to steal credentials and inject malicious code into widely used packages, ultimately aiming to hijack cryptocurrency transactions.
The Phishing Lure: A Masterclass in Deception
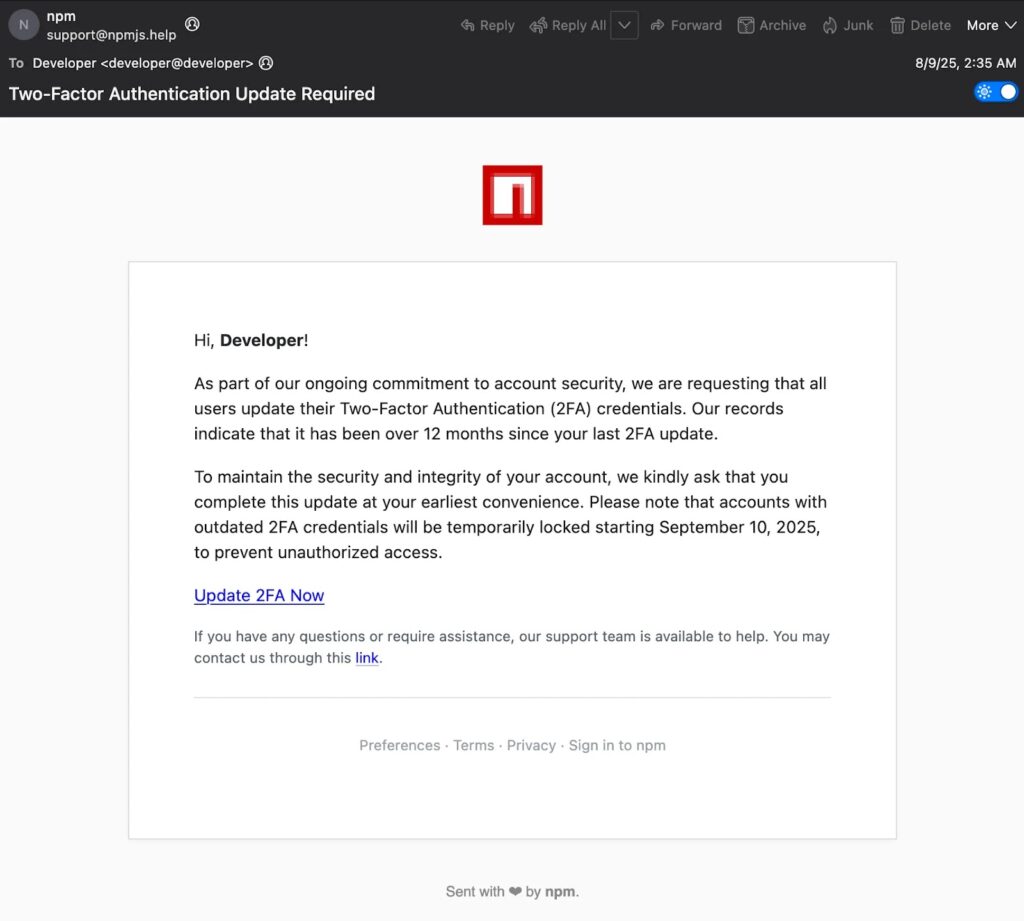
On September 8, 2025, threat actors launched a coordinated attack against prominent NPM maintainers. The campaign used expertly crafted phishing emails designed to appear as official security notifications from NPM itself.
The emails, sent from the deceptive domain support@npmjs[.]help, claimed that the developers needed to urgently update their two-factor authentication (2FA) settings to avoid account suspension. This created a false sense of urgency, pressuring targets to act quickly and bypass their natural skepticism.
Key Elements of the Attack:
- Spoofed Domain: The use of
npmjs[.]helpwas a classic example of typosquatting, making the sender address look legitimate at a glance. - Email Authentication Bypass: The emails cunningly passed standard security protocols like SPF, DKIM, and DMARC, making them appear more trustworthy in inboxes.
- Customized Phishing Links: Each email contained a unique link that directed the victim to a fake NPM login page hosted on the attacker’s domain, where their credentials were harvested.
The Aftermath: Account Takeover and Supply Chain Poisoning
The attack was successful against several developers, including Josh Junon (known as “qix”). The compromised developer accounts had control over popular NPM packages representing a staggering 2.8 billion weekly downloads.
Once inside, the attackers injected a malicious JavaScript payload into twenty different packages. This was not a random act of vandalism but a calculated move to deploy a “clipper” malware designed for financial gain.
The Final Payload: Cryptocurrency Hijacking
The injected malware was a sophisticated clipper designed to monitor for cryptocurrency transactions. When a user of a compromised package initiated a transaction involving major cryptocurrencies like:
- Bitcoin (BTC)
- Ethereum (ETH)
- Solana (SOL)
- Tron (TRX)
- Litecoin (LTC)
- Bitcoin Cash (BCH)
…the malware would silently intercept the transaction. It would then replace the intended recipient’s wallet address with one controlled by the attacker, diverting the funds without the user’s knowledge.
Detection and Mitigation: A Multi-Layered Defense
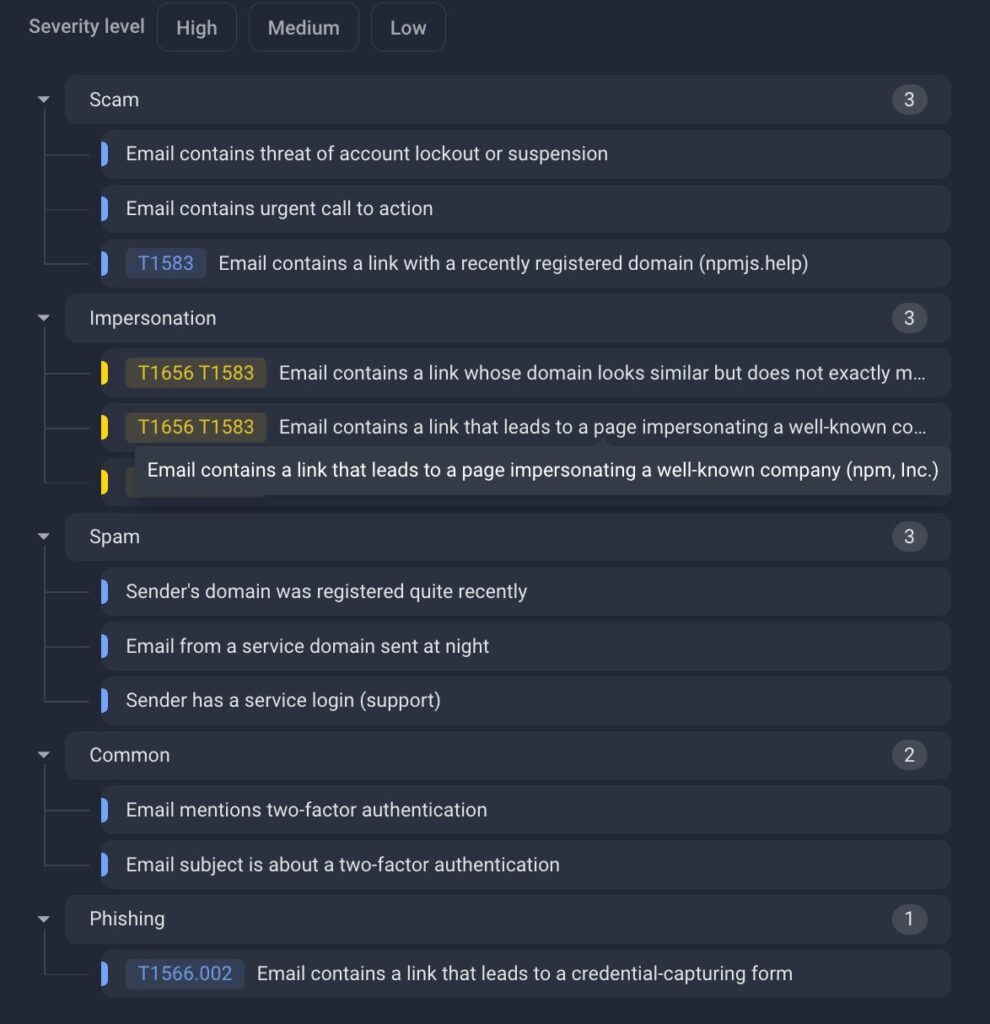
The threat was identified by security analysts who used a multi-layered approach to detect the malicious campaign, which included:
- Domain Intelligence: Checking RDAP records to identify the recently registered and suspicious
npmjs[.]helpdomain. - Brand Impersonation Analysis: Detecting the visual and textual mimicry of the legitimate NPM brand.
- Content and Behavioral Analysis: Identifying the social engineering language and analyzing the phishing page’s functionality, which was designed solely to capture login credentials.
Following the discovery, the affected packages were reverted to their clean versions, and the compromised developer accounts were secured, preventing a wider catastrophe.


