Russia Linked Hackers Abuse Microsoft 365 Device Code Phishing for Account Takeovers
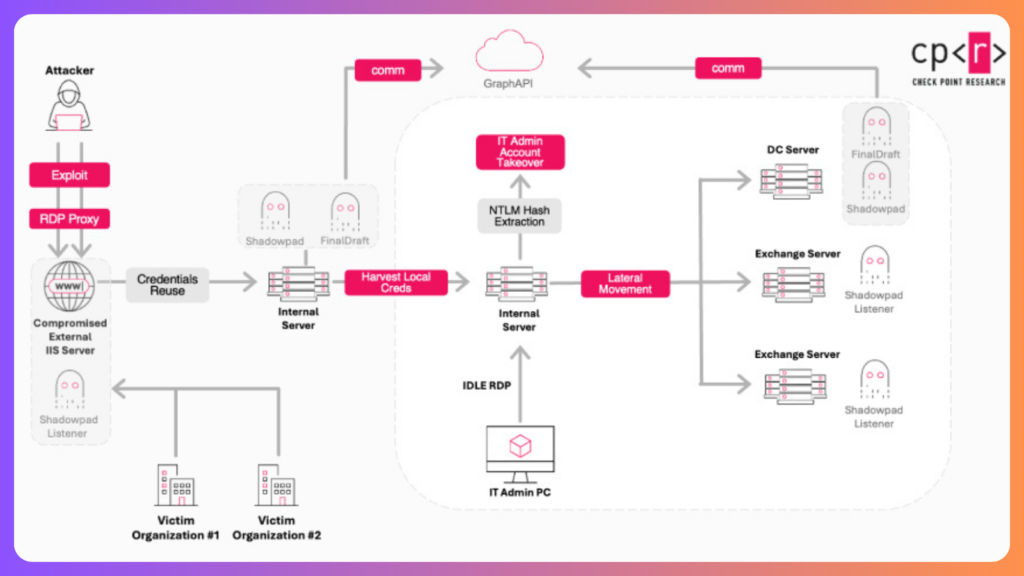
A suspected Russia-aligned threat group has been identified for a phishing campaign targeting Microsoft 365 users by exploiting device code authentication flows to steal credentials and conduct account takeovers. The campaign, active since September 2025, is tracked by Proofpoint under the designation UNK_AcademicFlare. Attackers have primarily targeted email accounts associated with government and military organizations, […]
Russia Linked Hackers Abuse Microsoft 365 Device Code Phishing for Account Takeovers Read More »