SideWinder APT Uses ClickOnce Based Attack Chain to Target South Asian Diplomats
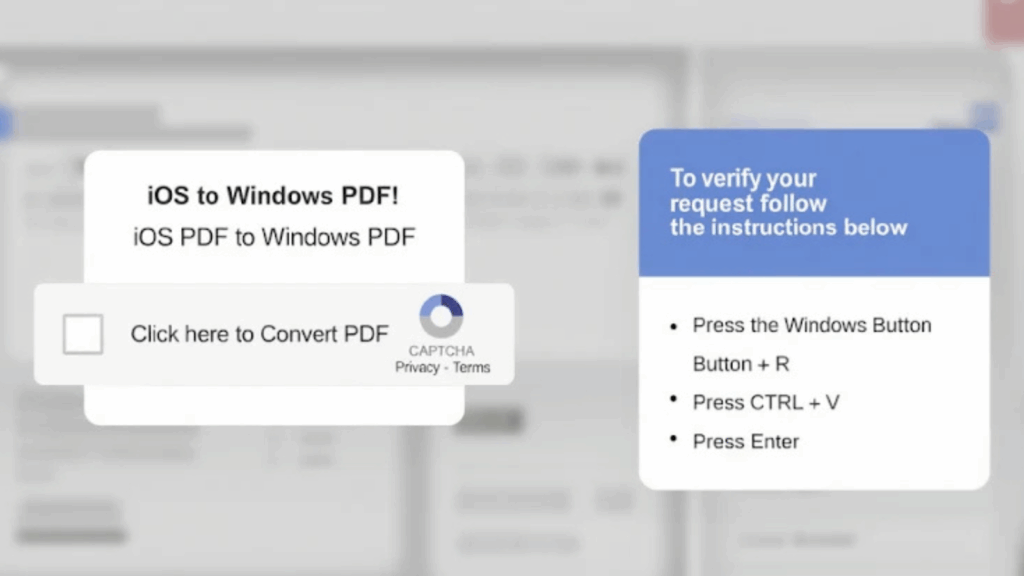
A new cyber espionage campaign has been uncovered, showing the continuous evolution of the SideWinder advanced persistent threat (APT) group. The operation, which took place in September 2025, targeted a European embassy in New Delhi and multiple organizations across Sri Lanka, Pakistan, and Bangladesh. Researchers from Trellix, Ernesto Fernández Provecho and Pham Duy Phuc, have […]
SideWinder APT Uses ClickOnce Based Attack Chain to Target South Asian Diplomats Read More »