Canada House of Commons Hit by Microsoft Exploit
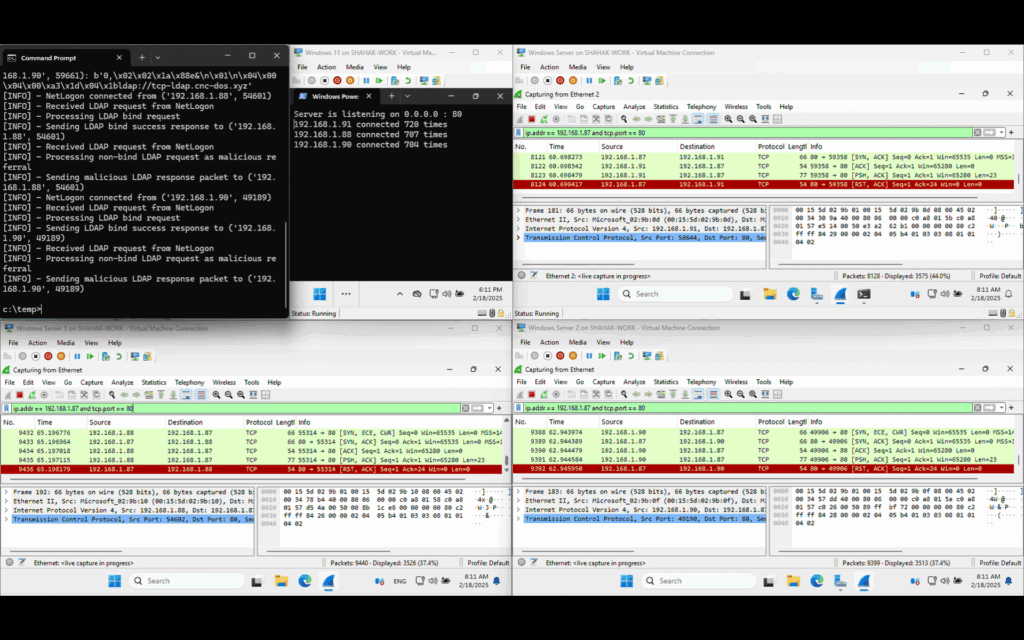
On August 9, 2025, the Canadian House of Commons experienced a cyberattack in which threat actors exploited a recently disclosed Microsoft vulnerability to gain unauthorized access to sensitive employee data. The incident highlights the persistent cybersecurity challenges facing Canadian government institutions amid a rapidly escalating global threat landscape. Details of the Breach According to an […]
Canada House of Commons Hit by Microsoft Exploit Read More »