KadNap Malware Compromises Over 14,000 Edge Devices to Build Stealth Proxy Botnet
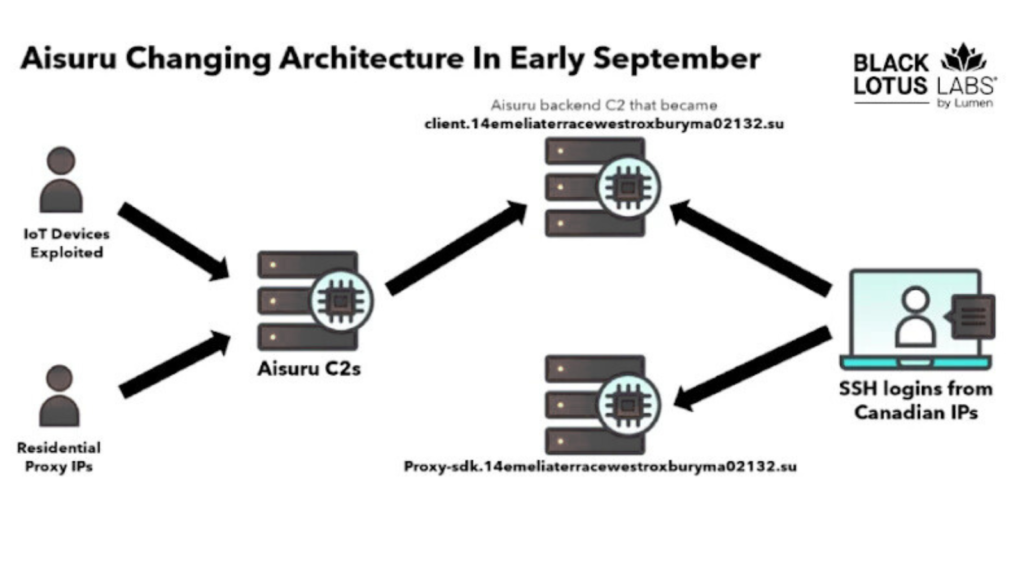
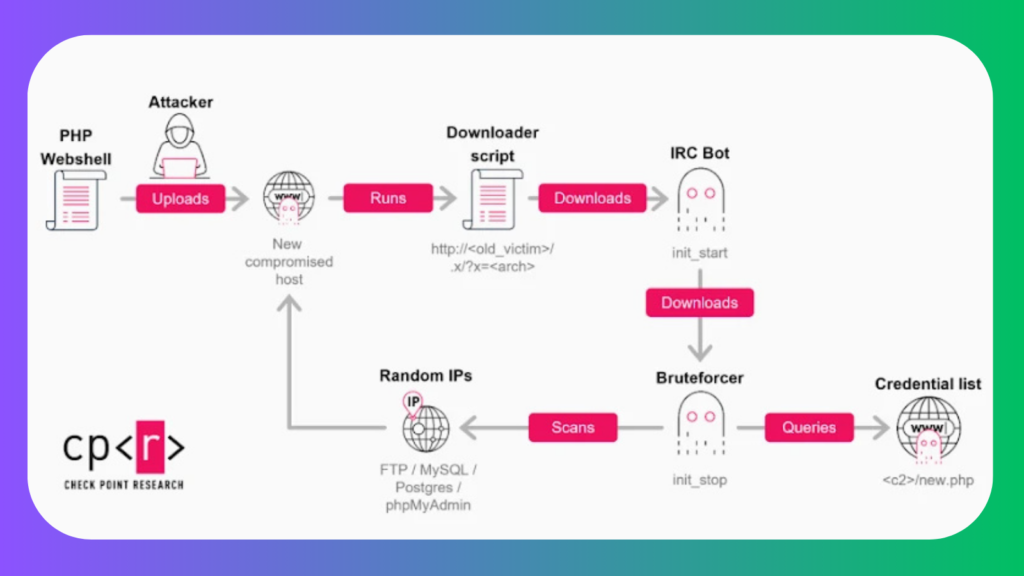
Cybersecurity researchers have uncovered a sophisticated malware campaign involving a threat dubbed KadNap, which primarily targets Asus routers and other edge devices to build a stealthy proxy botnet. The malware has compromised over 14,000 devices globally, with more than 60% of infections in the U.S., according to Black Lotus Labs at Lumen. KadNap uses a custom implementation of the Kademlia Distributed […]
KadNap Malware Compromises Over 14,000 Edge Devices to Build Stealth Proxy Botnet Read More »