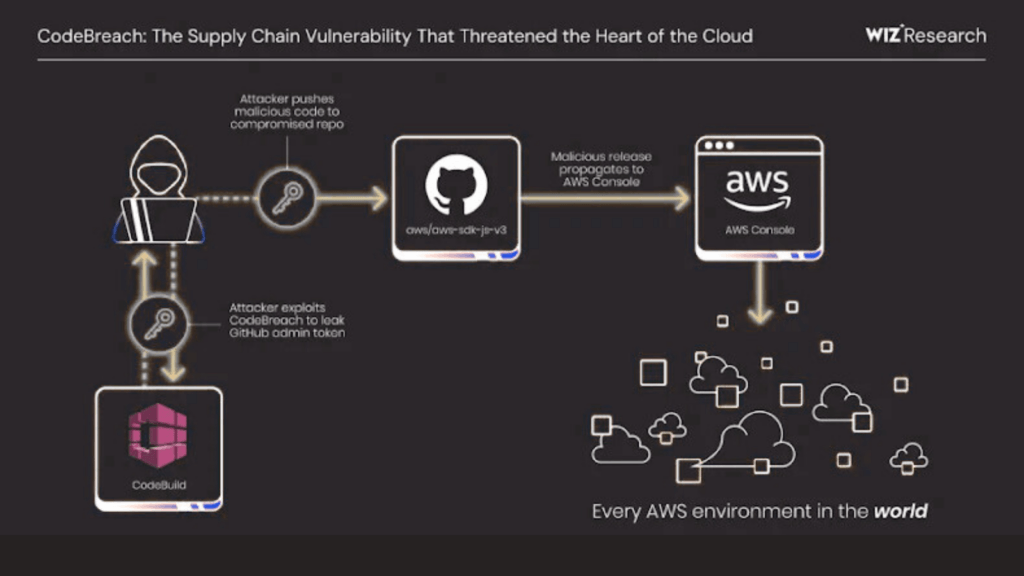
UNC6426 Uses nx npm Supply Chain Attack to Obtain AWS Admin Access Within 72 Hours
Cybersecurity investigators have revealed that a threat actor identified as UNC6426 successfully breached a company’s cloud infrastructure within 72 hours by abusing credentials stolen during a software supply chain compromise involving the Nx npm package. According to findings published in the Google Cloud Threat Horizons Report H1 2026, the attacker initially obtained a developer’s GitHub token. This credential enabled […]
UNC6426 Uses nx npm Supply Chain Attack to Obtain AWS Admin Access Within 72 Hours Read More »