APT28 Deploys BEARDSHELL and COVENANT Malware in Espionage Campaign Against Ukrainian Military
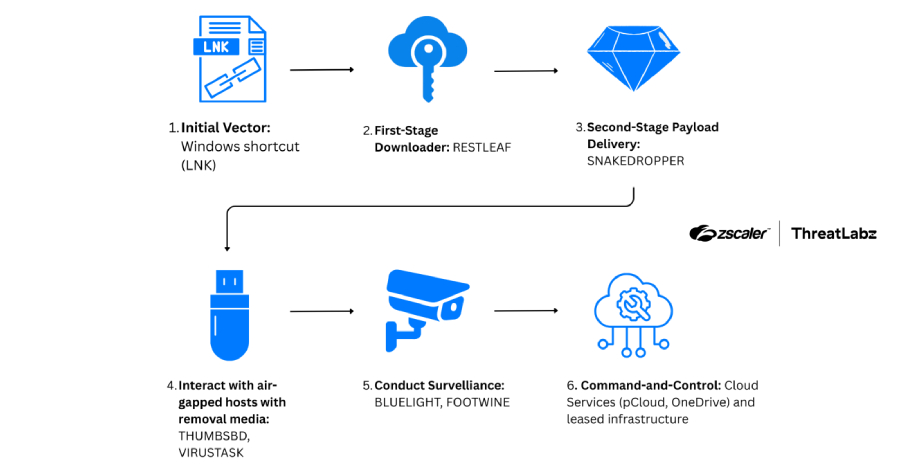
The Russia linked threat group APT28 has been observed deploying two malware implants, BEARDSHELL and COVENANT, in cyber espionage operations targeting Ukrainian military personnel. According to a new investigation by ESET, the malware tools have been actively used since April 2024 to maintain persistent access and conduct long term surveillance. APT28, also widely known by aliases such as Fancy Bear, Sednit, Pawn Storm, and TA422, […]