New Business Email Protection Method Blocks Phishing Attack Behind NPM Breach
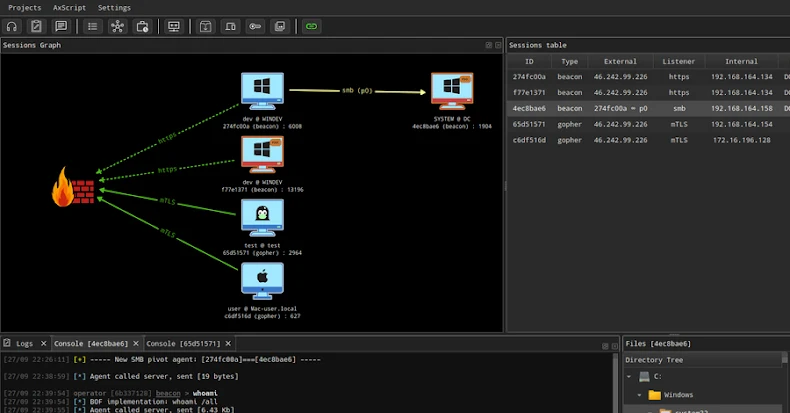
A highly sophisticated phishing campaign successfully targeted high-profile developers on the NPM registry in September 2025, leading to one of the most significant supply chain attacks in its history. The attackers combined convincing social engineering with technical precision to steal credentials and inject malicious code into widely used packages, ultimately aiming to hijack cryptocurrency transactions. […]
New Business Email Protection Method Blocks Phishing Attack Behind NPM Breach Read More »