New Advanced Phishing Kits Use AI and MFA Bypass Techniques to Steal Credentials at Scale
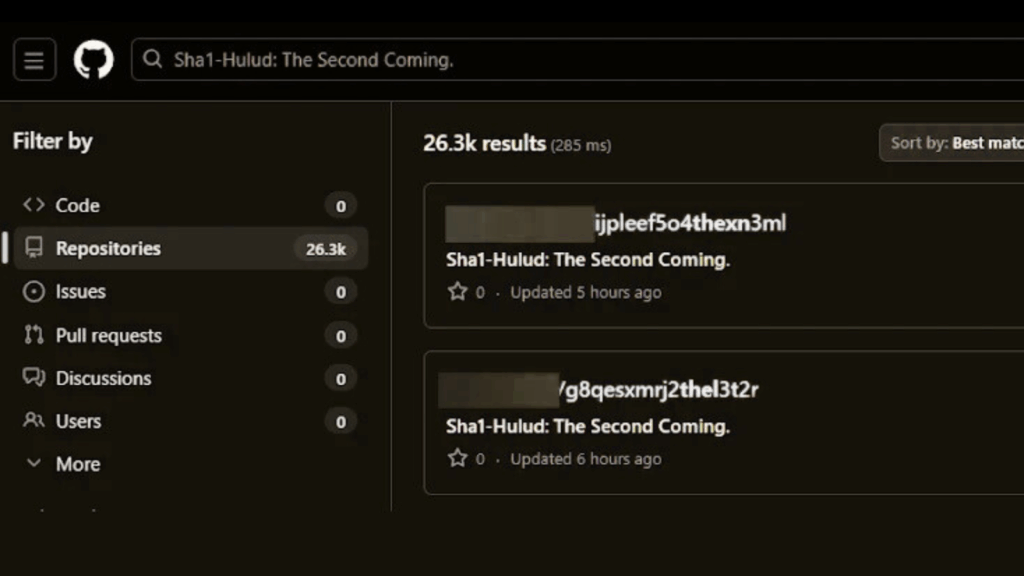
Cybersecurity researchers are warning about a new wave of highly advanced phishing kits that are enabling large scale credential theft by combining automation, artificial intelligence, and multi factor authentication bypass techniques. The newly observed toolkits, known as BlackForce, GhostFrame, InboxPrime AI, and Spiderman, represent a growing shift toward industrialized phishing operations. BlackForce Targets MFA Using […]