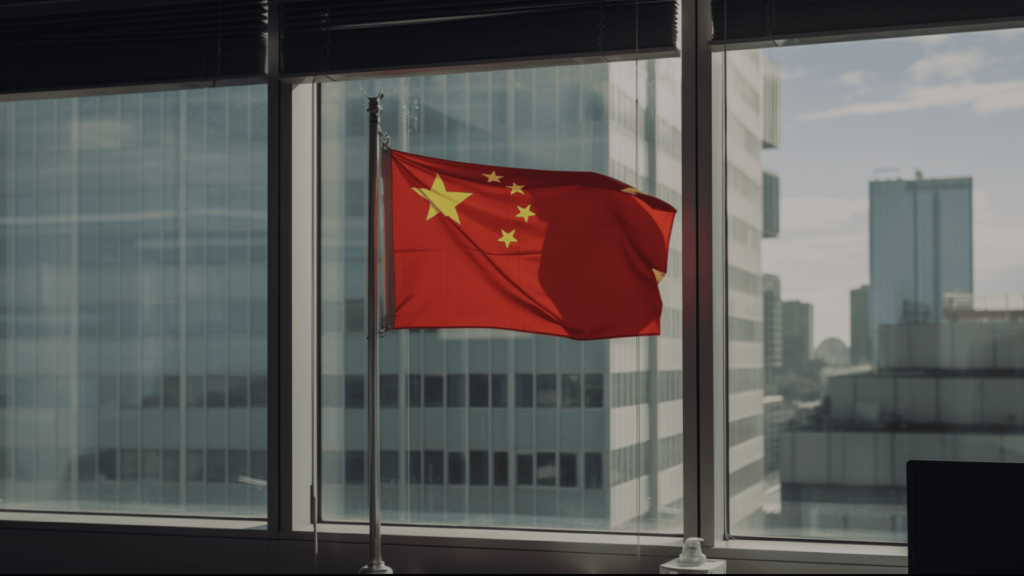
MuddyWater Uses UDPGangster Backdoor in Targeted Campaign Across Turkey, Israel, and Azerbaijan
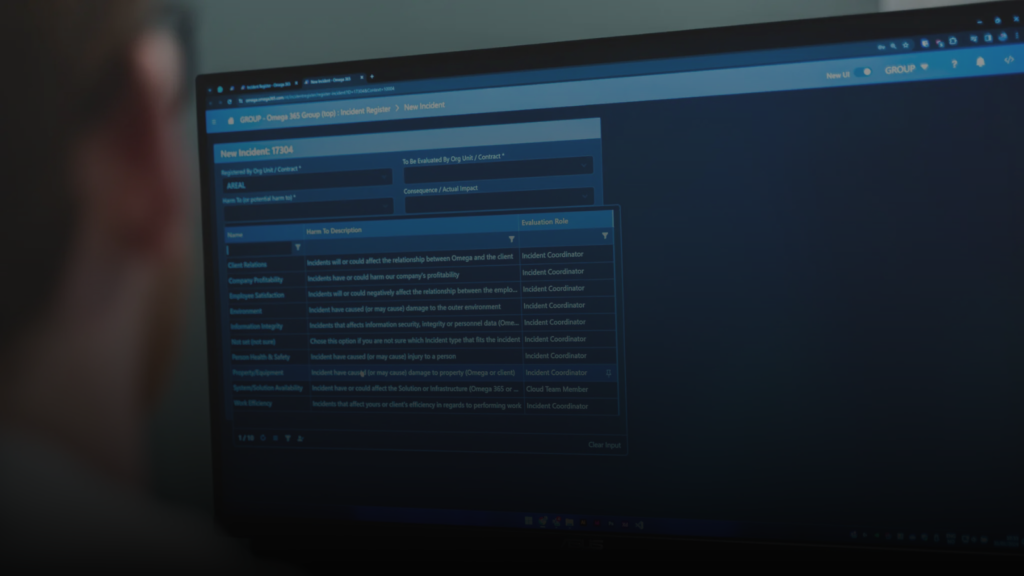
In a newly identified cyber espionage operation, the Iranian aligned group MuddyWater has been found using a previously unknown backdoor named UDPGangster. The malware relies on the User Datagram Protocol (UDP) to manage command and control traffic, a choice that helps attackers avoid traditional network monitoring defenses. Security analysts at Fortinet FortiGuard Labs report that […]