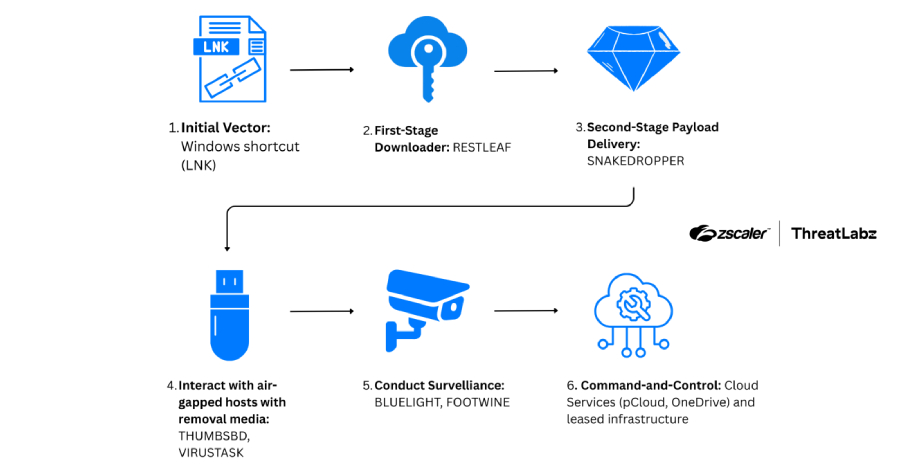
SloppyLemming Targets Government Entities in Pakistan and Bangladesh with Dual Malware Chains
The cyber threat cluster identified as SloppyLemming has been linked to a new wave of targeted attacks against government institutions and critical infrastructure organizations in Pakistan and Bangladesh, according to fresh research from Arctic Wolf. The activity reportedly occurred between January 2025 and January 2026 and involved two separate malware delivery chains. These attack paths […]