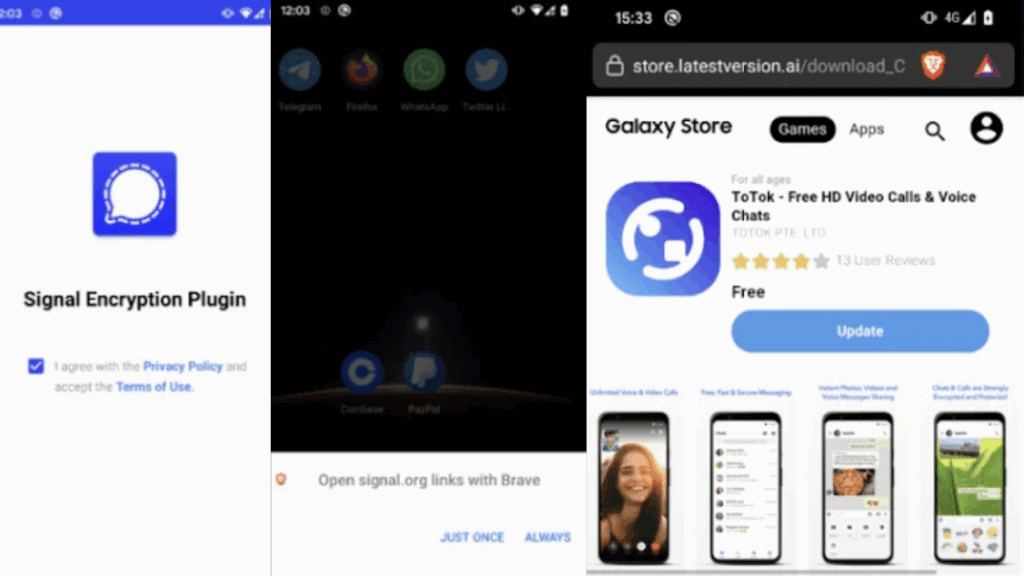
Android Spyware Masquerades as Signal Encryption Plugin and ToTok Pro, Users at Risk
Cybersecurity experts have uncovered two dangerous Android spyware campaigns known as ProSpy and ToSpy, targeting users in the United Arab Emirates (U.A.E.). These malicious campaigns disguise themselves as popular apps such as Signal Encryption Plugin and ToTok Pro to trick unsuspecting victims into installing spyware on their devices. Fake Apps and Distribution Tactics According to […]
Android Spyware Masquerades as Signal Encryption Plugin and ToTok Pro, Users at Risk Read More »