Hackers Exploit SendGrid Service to Steal User Login Credentials
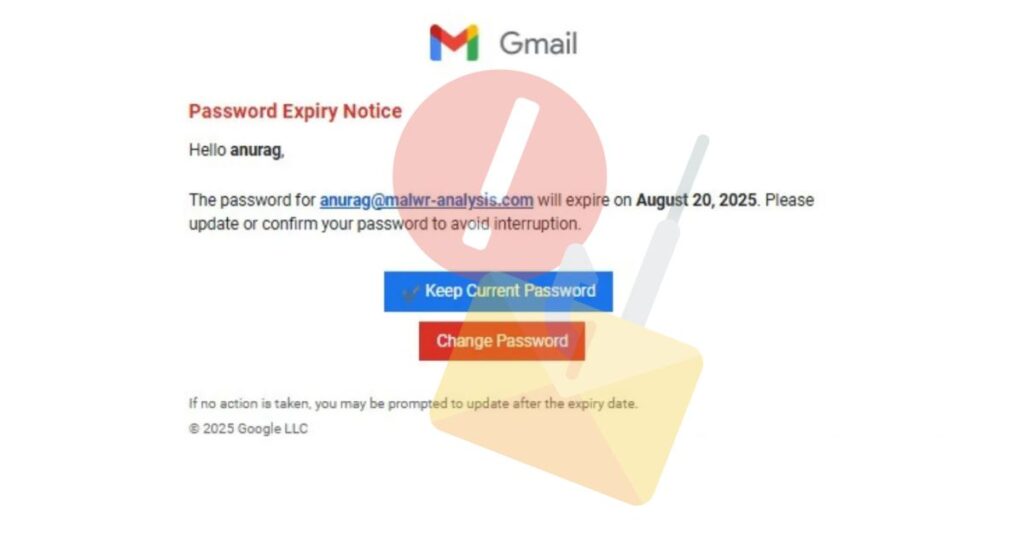
A highly advanced phishing operation has been detected, abusing the trusted reputation of SendGrid to harvest user credentials. Attackers are using SendGrid’s legitimate cloud-based email service to distribute phishing emails that evade traditional email security filters. Campaign Overview This campaign relies on psychological manipulation and urgency tactics, with three crafted email themes designed to pressure […]
Hackers Exploit SendGrid Service to Steal User Login Credentials Read More »