Hackers Abuse ASP.NET Machine Keys to Compromise IIS Servers and Install Malicious Modules
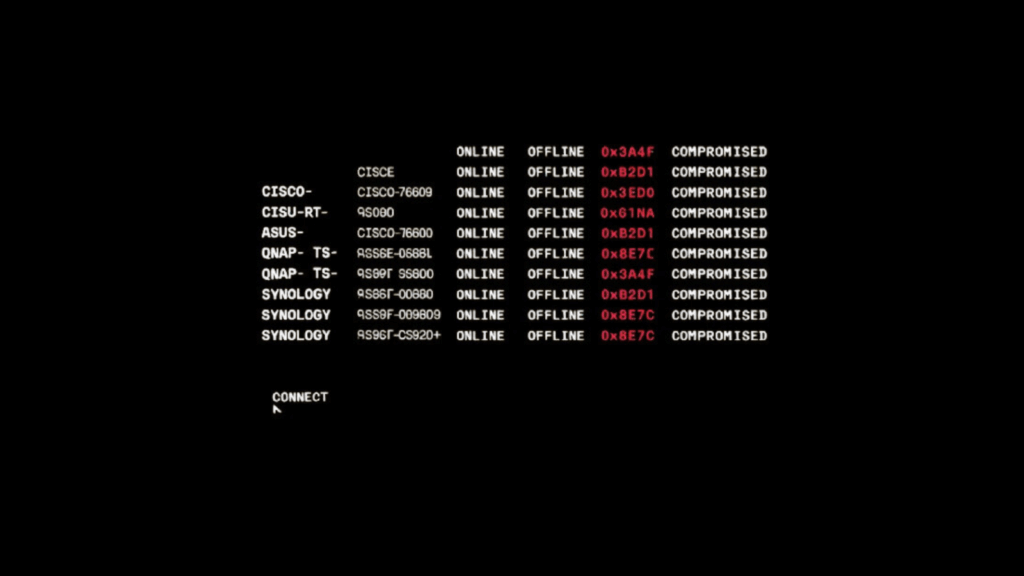
Security researchers have uncovered a widespread campaign where attackers exploited publicly available ASP.NET machine keys to break into Windows IIS web servers, then installed a malicious IIS module to hijack traffic and profit from fake search rankings. The group, tracked as REF3927, leveraged keys published in places like Microsoft documentation and online forums, making many […]