Researchers Reveal TA585’s MonsterV2 Malware Capabilities, Full Attack Chain
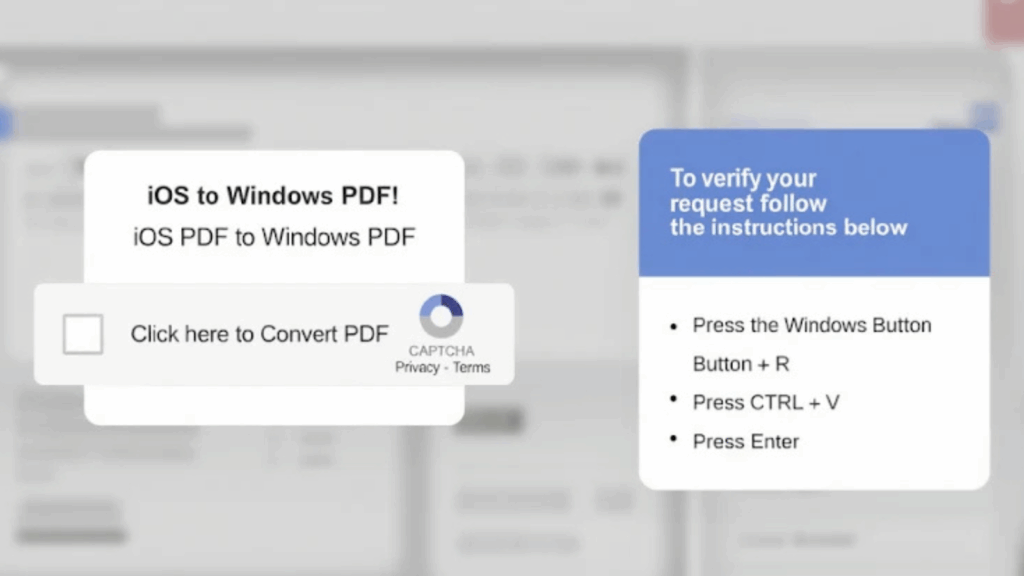
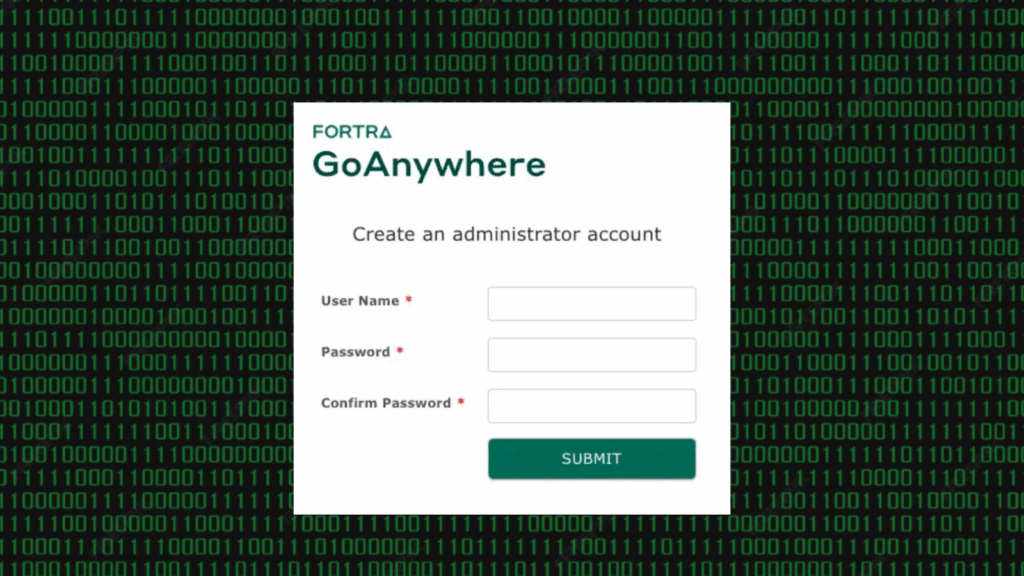
Cybersecurity researchers have exposed a previously undocumented threat actor, TA585, which delivers an off-the-shelf malware called MonsterV2 through targeted phishing campaigns. Proofpoint researchers describe TA585 as operating a self-owned, end-to-end attack chain, managing infrastructure, delivery, and payload installation without relying on third-party distribution services. Background and delivery methods TA585 has used multiple delivery techniques in […]
Researchers Reveal TA585’s MonsterV2 Malware Capabilities, Full Attack Chain Read More »