Shuyal Stealer Targets 19 Browsers to Harvest Login Credentials
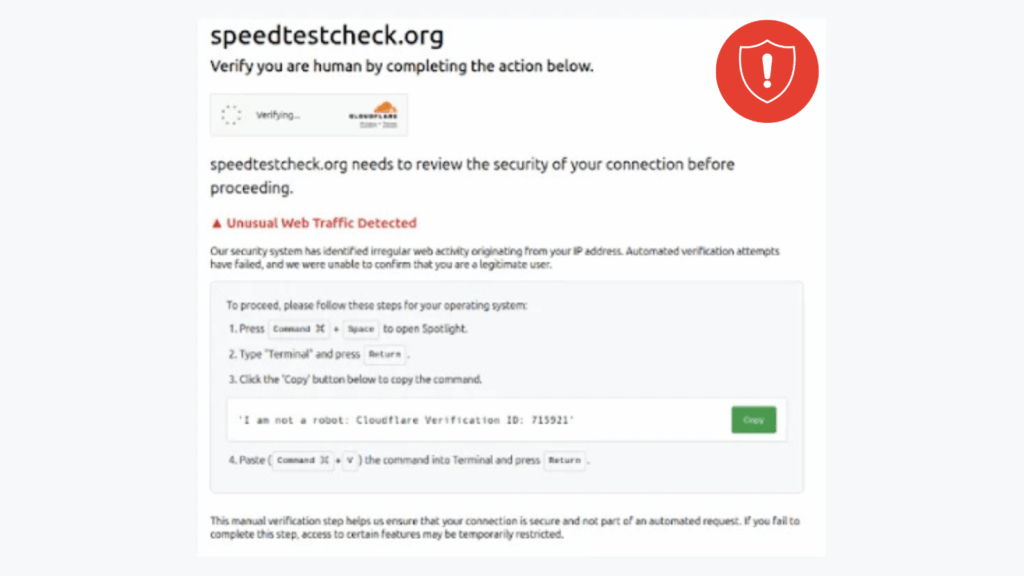
Shuyal Stealer has quickly become one of the most flexible credential theft tools observed in recent months. First seen in early August, its modular design enables it to target a wide variety of web browsers, including Chromium-based, Gecko-based, and legacy engines, making it a high-risk threat for many environments. Early signs and impact Initial indicators […]
Shuyal Stealer Targets 19 Browsers to Harvest Login Credentials Read More »