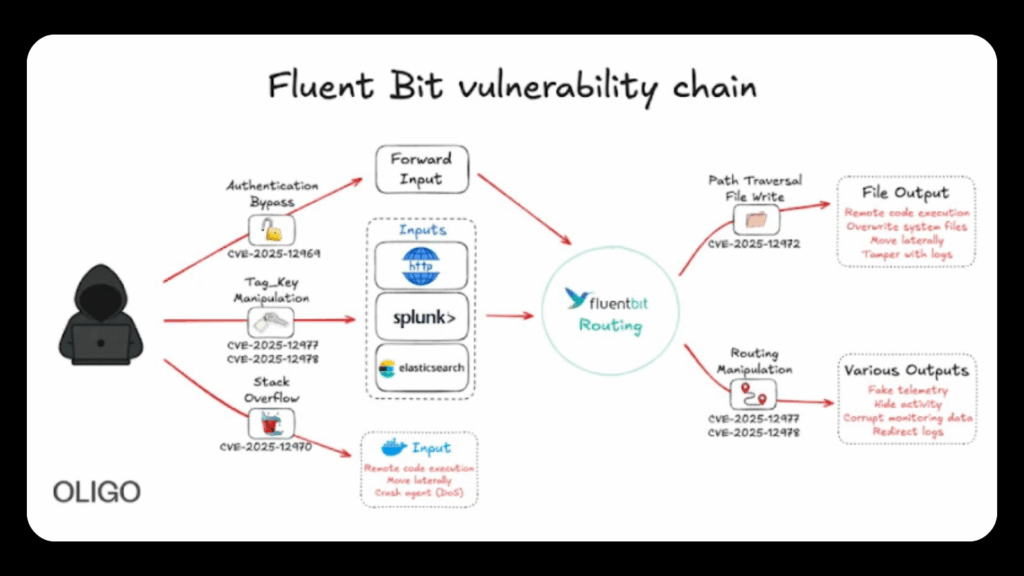
New Fluent Bit Vulnerabilities Expose Cloud Systems to RCE and Stealthy Infrastructure Intrusions
Cybersecurity analysts have identified five significant vulnerabilities in Fluent Bit, a widely used open source telemetry agent. These flaws can be combined to compromise cloud environments and potentially give attackers full control over infrastructure. Oligo Security shared the findings, noting that the weaknesses allow authentication bypass, path traversal, remote code execution, service disruption, and tag […]